The OpenSSH team has released versions 10.3 and 10.3p1 on April 2, 2026, which address a significant shell injection vulnerability and introduce several enhancements to security. Administrators are advised to familiarize themselves with these updates before proceeding with the upgrade.
Key Security Fixes in OpenSSH 10.3
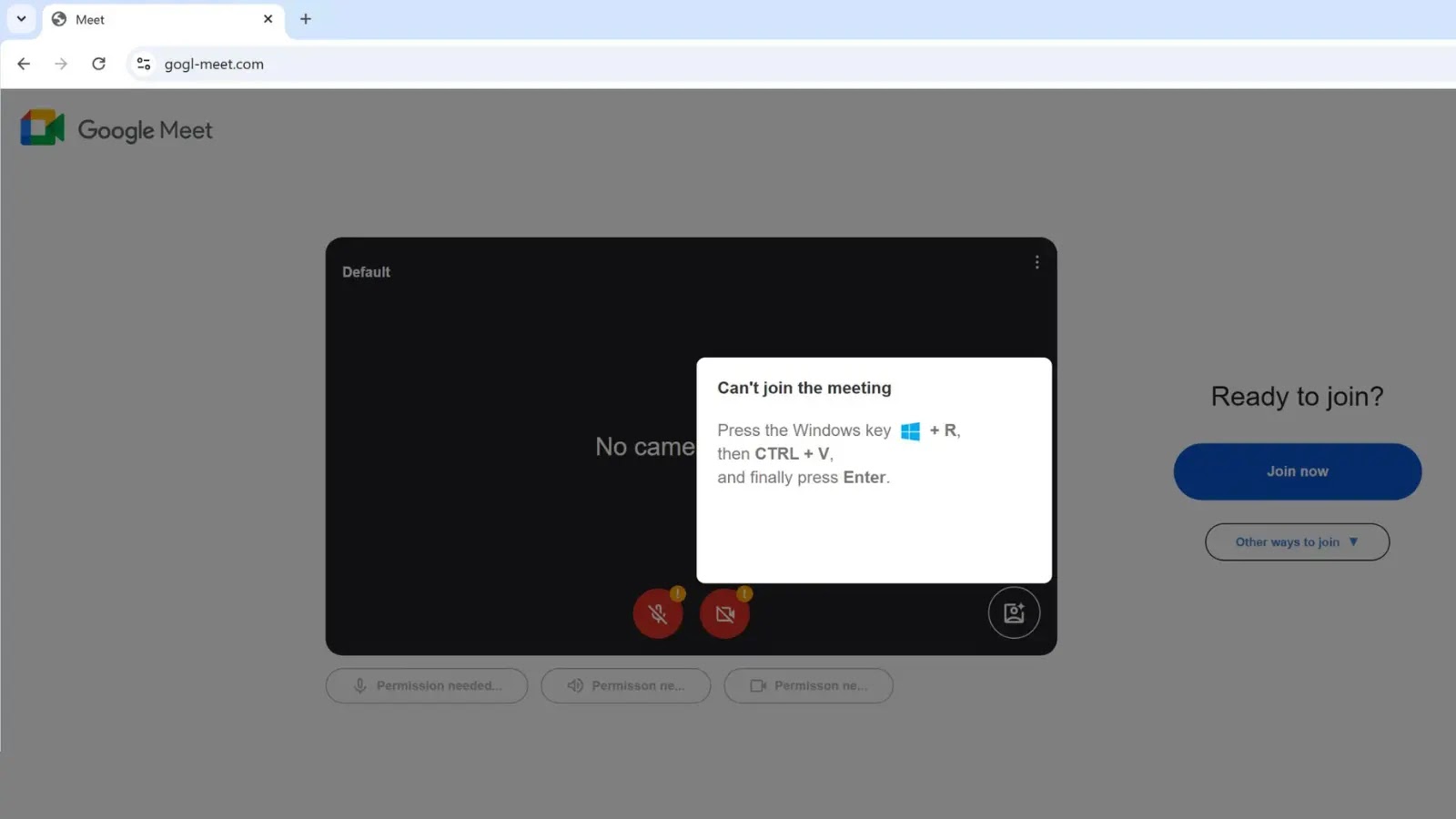
A critical improvement targets the shell injection vulnerability associated with the -J (ProxyJump) command-line option. In previous versions, user and host names entered via -J or -oProxyJump=”…” were not properly validated, potentially allowing malicious actors to exploit this feature if the inputs were adversarial.
This vulnerability was identified by a researcher known as “rabbit.” The developers of OpenSSH have emphasized that exposing these options to untrusted sources was inherently risky. The new update ensures that invalid or harmful values are now blocked during validation, although this fix only applies to command-line usage and not configuration file entries.
Updates to SSH Certificate Handling
Another important change addresses sshd certificate handling. Previously, SSH certificates with empty principals were treated as wildcards, permitting authentication as any user trusting the Certificate Authority (CA). While this was an intentional feature, it posed a security risk if a CA unintentionally issued a certificate without defined principals.
With OpenSSH 10.3, certificates with blank principals no longer match any user, thereby eliminating the potential for unauthorized access. Moreover, wildcard characters in certificate principals are now enforced for host certificates but not for user certificates, ensuring clearer access controls.
Impact on SSH Protocol Compliance
OpenSSH 10.3 also ceases support for SSH implementations that lack transport-layer rekeying. Consequently, older SSH clients or servers unable to manage rekeying will face interoperability issues once a rekey is required. This update enhances protocol adherence and removes a workaround that could compromise security in long-lasting sessions.
Organizations managing SSH infrastructure should prioritize this update, particularly in environments where ProxyJump options are automatically generated or sourced from user input. The changes to certificate principal handling necessitate a review of current CA-issued certificates to ensure compliance.
OpenSSH 10.3 can be downloaded from the official mirrors at openssh.com. The project’s consistent updates reinforce its role as a vital component in secure remote access, addressing subtle yet significant security vulnerabilities.
Stay informed with daily cybersecurity updates by following us on Google News, LinkedIn, and X. Reach out to us to feature your security stories.