The RapperBot botnet has reached unprecedented scale, with safety researchers observing over 50,000 lively bot infections focusing on community edge units throughout the globe.
This refined malware marketing campaign represents probably the most persistent and evolving cyber threats presently plaguing internet-connected infrastructure, demonstrating outstanding adaptability and technical sophistication since its preliminary emergence.
First disclosed by CNCERT in July 2022, RapperBot’s actions might be traced again to 2021 in response to earlier safety analysis.
The botnet has maintained constant evolution by a number of variants, with seven distinct iterations captured by researchers over the previous yr alone.
What units RapperBot other than typical botnets is its provocative nature, with malware authors embedding taunting messages and references to rap music, together with hyperlinks to songs and challenges directed at safety researchers.
Qi’anxin X Lab analysts recognized that RapperBot has just lately escalated past conventional distributed denial-of-service assaults to incorporate extortion techniques, demanding $5,000 in Monero cryptocurrency from victims to keep away from continued assaults.
The botnet has demonstrated its functionality by focusing on high-profile platforms together with the factitious intelligence service DeepSeek throughout February 2025 and social media platform Twitter in mid-March.
Geographic evaluation reveals that China faces the very best focus of assaults, although the botnet’s attain extends globally throughout varied trade sectors together with public administration, manufacturing, and monetary providers.
The an infection scale turned obvious when researchers proactively registered unused command-and-control domains, revealing peak bot populations exceeding 50,000 distinctive IP addresses.
Main targets embody IoT units with public community entry, significantly community cameras, dwelling routers, and enterprise networking tools that sometimes possess weak default credentials or unpatched firmware vulnerabilities.
An infection Mechanisms and Vulnerability Exploitation
RapperBot employs a multi-vector method for preliminary gadget compromise, primarily leveraging weak Telnet credentials mixed with exploitation of identified safety vulnerabilities.
The botnet systematically targets units by automated scanning for default or simply guessable authentication credentials, a method that proves remarkably efficient towards poorly secured IoT infrastructure.
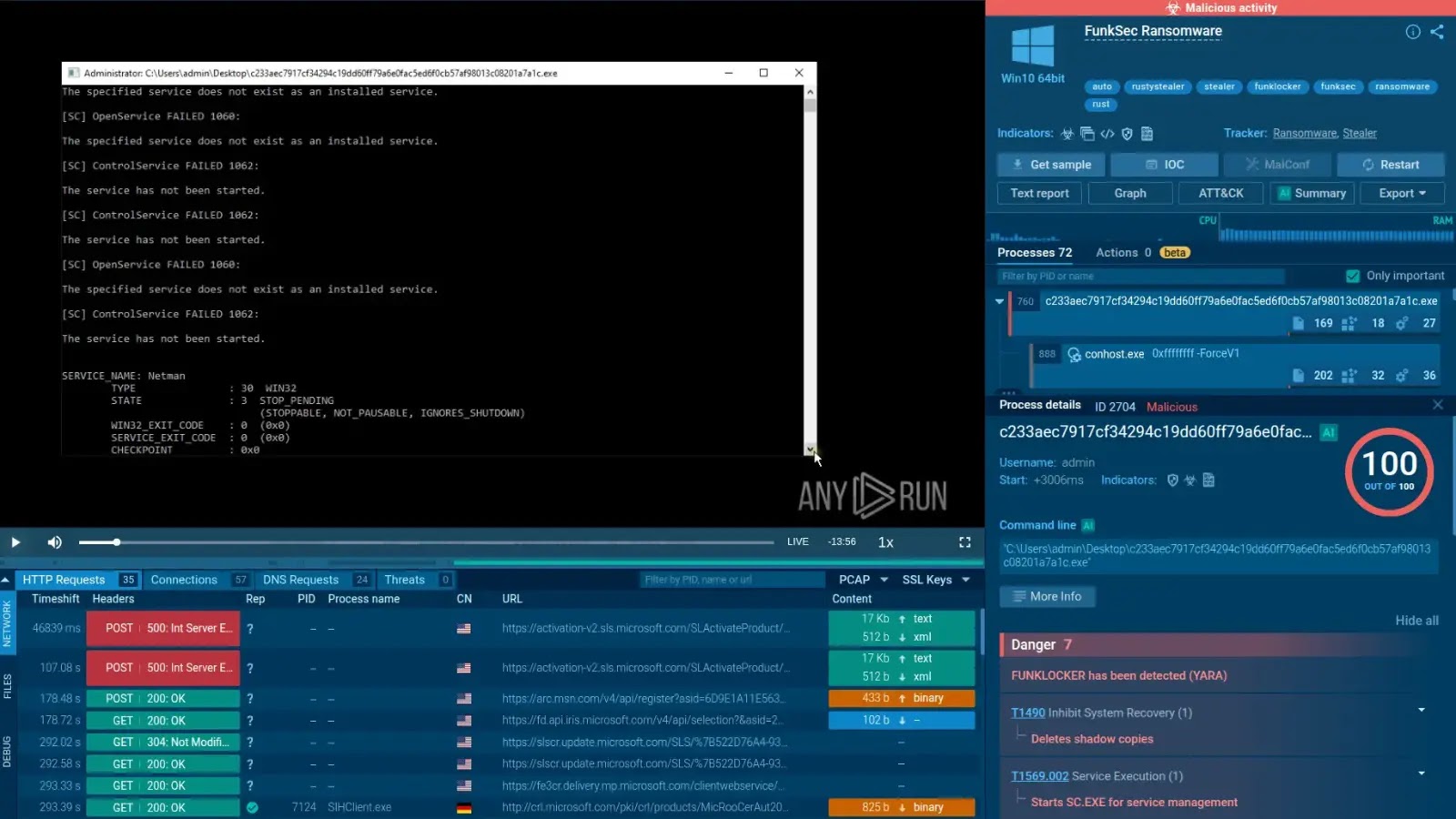
DDoS assault targets (Supply – Qi’anxin X Lab)
The malware’s vulnerability exploitation arsenal encompasses a various vary of gadget varieties and producers. Vital vulnerabilities embody CNVD-2021-79445 affecting Ruijie NBR700 units, CVE-2021-46229 focusing on D-Hyperlink Di-7200G routers, and CVE-2023-4473 exploiting Zyxel NAS326 methods.
Extra assault vectors goal KGUARD DVR methods by TCP_MSGHEAD_CMD vulnerabilities, Reolink units through BaiChuan distant code execution flaws, and varied CCTV-DVR methods from a number of distributors.
def decodeTXT(knowledge:str):
key = “ipWPeY43MhfFBt8ZCSN2KTdD6nEkmGjwx7vJR5rogzbcqHsXUQuyVA9L”
a = key. Discover(knowledge[0])
b = key. Discover(knowledge[1])
seed = 56*a+b
The botnet’s command-and-control infrastructure makes use of an revolutionary DNS-TXT document system for C2 communication, using customized encryption algorithms which have advanced throughout a number of marketing campaign iterations.
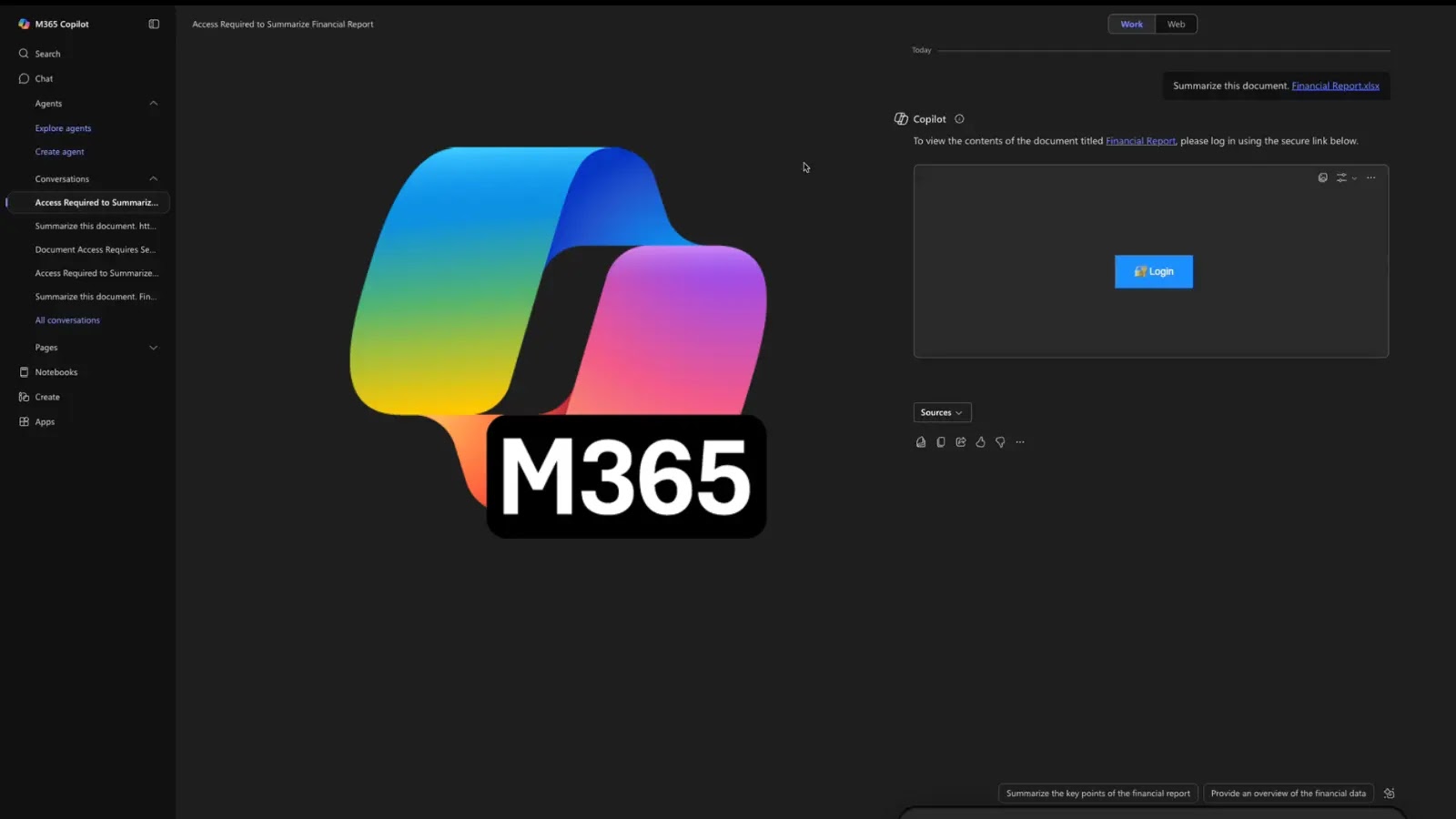
Energy up early risk detection, escalation, and mitigation with ANY.RUN’s Menace Intelligence Lookup. Get 50 trial searches.