Menace actors are more and more abandoning conventional languages like C and C++ in favor of contemporary alternate options similar to Golang, Rust, and Nim.
This strategic shift permits builders to compile malicious code for each Linux and Home windows with minimal modifications.
Among the many rising threats on this panorama is “Luca Stealer,” a Rust-based info stealer that has not too long ago appeared within the wild alongside different notable threats similar to BlackCat ransomware.
The Rise of Luca Stealer
Whereas Rust’s adoption within the malware neighborhood continues to be in its early phases in comparison with Golang, it’s increasing quickly.
Luca Stealer represents a major improvement because it was launched publicly beneath an open-source mannequin.
constructed binary may be opened in a disassembler
This availability gives safety researchers with a singular alternative to check how Rust is utilized in malicious software program design, providing important insights for future protection methods.
The shift to those languages requires defenders to develop new evaluation methods to detect and reverse-engineer these subtle binaries.
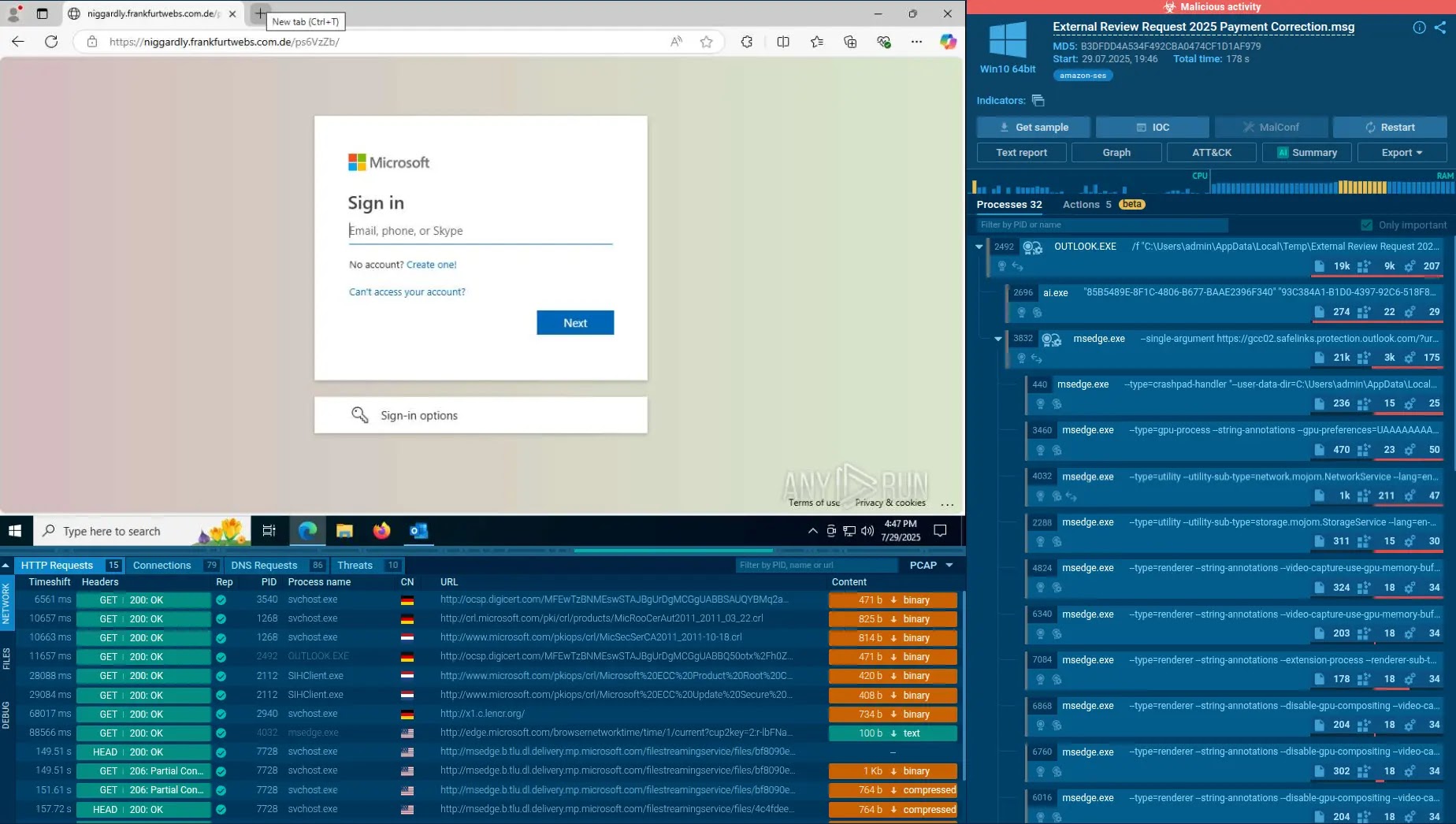
Analyzing Rust binaries presents distinctive challenges for defenders utilizing normal instruments. In contrast to normal C applications, Rust executables deal with strings otherwise.
leak the username of the person who compiled this system relying on the place on disk this system was compiled
Rust strings aren’t null-terminated, that means they don’t finish with a “null byte” to mark the tip of the textual content. This typically causes reverse engineering instruments like Ghidra to misread knowledge, resulting in overlapping string definitions.
Analysts should often manually clear code bytes and redefine strings to establish legitimate knowledge appropriately.
Moreover, discovering the first perform in a Rust binary requires particular data of the compiler’s output.
In keeping with Binary Defence, the entry level usually initialises the surroundings after which calls a particular inner perform (std::rt::lang_start_internal).
This perform receives the tackle of the particular user-written main perform, which researchers can establish by tracing the arguments handed throughout this name.
One benefit for defenders is the presence of artifacts left by the Rust construct system, Cargo. Exterior dependencies, often known as “crates,” are sometimes statically linked into the binary.
Working the “RustDependencyStrings.py” script in opposition to the binary reveals the crates
By looking for particular string patterns, similar to cargoregistry, analysts can record the libraries a malware pattern makes use of, similar to reqwest for HTTP requests.
Moreover, compilation artifacts like PDB paths might stay within the “Debug Information” part, doubtlessly leaking the writer’s username or system paths.
As risk actors proceed to leverage Rust, understanding these structural nuances is important for efficient detection.
Indicators of Compromise (IoCs)
TypeIdentifierDescriptionSHA2568f47d1e39242ee4b528fcb6eb1a89983c27854bac57bc4a15597b37b7edf34a6Unknown Rust Malware SampleStringcargoregistryIndicator of Rust crate dependenciesStringstd::rt::lang_start_internalIndicator of Rust runtime entry level
Comply with us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to characteristic your tales.