Cybersecurity researchers have uncovered a classy marketing campaign the place risk actors impersonate writers from main Korean broadcasting networks to distribute malicious paperwork.
The operation, tracked as Operation Artemis, represents a notable evolution in social engineering ways by leveraging trusted media personalities to ascertain credibility with potential victims earlier than delivering dangerous payloads.
The marketing campaign demonstrates a multi-stage assault technique that mixes deception with superior technical evasion strategies.
Risk actors contact victims via e-mail communications disguised as respectable interview requests or skilled collaboration alternatives.
The attackers current themselves as established writers from acknowledged Korean tv packages, utilizing authentic-sounding proposals associated to North Korean affairs and human rights points to align with goal pursuits.
This method proves significantly efficient as a result of the subjects resonate with teachers, journalists, and coverage specialists who ceaselessly work together with media organizations.
Genians analysts recognized that the malware emerges from malicious HWP paperwork—Hangul Phrase Processor recordsdata that function the usual doc format in South Korea.
These poisoned recordsdata arrive as attachments masked as interview questionnaires or occasion information supplies. As soon as a sufferer opens the doc and clicks embedded hyperlinks, the an infection chain initiates silently within the background.
The technical implementation reveals appreciable sophistication. The assault leverages DLL side-loading, a way the place respectable system utilities from Microsoft Sysinternals turn out to be unwitting accomplices.
Picture Used within the Steganography Assault (Supply – Genians)
Risk actors place malicious DLL recordsdata alongside respectable executables, inflicting Home windows to load the corrupted library as an alternative.
Particularly, the malware creates recordsdata named model.dll that get loaded by respectable processes like vhelp.exe and mhelp.exe.
This technique evades conventional signature-based safety instruments as a result of the guardian processes seem respectable to straightforward antivirus software program.
Assault Circulation (Supply – Genians)
The DLL file employs a number of encryption layers utilizing XOR operations with key values like 0xFA and 0x29 to hide its true objective.
Relying on the goal system’s capabilities, the malware intelligently selects between customary byte-wise XOR decryption or high-speed SSE (Streaming SIMD Extensions) strategies processing 16 bytes concurrently.
This adaptive method will increase processing pace whereas sustaining stealth towards pattern-matching safety programs.
DLL Facet-Loading Technical Breakdown
The malware in the end deploys RoKRAT, a classy data-stealing software. The an infection chain consists of OLE object execution inside HWP paperwork, adopted by non permanent folder deployment of executable recordsdata and malicious DLLs.
The payload undergoes sequential XOR decryption phases earlier than activating as last shellcode.
Forensic evaluation revealed the risk actors maintained command-and-control infrastructure via Yandex Cloud companies in Russia, with account tokens displaying registration dates spanning from October 2023 to February 2025, indicating sustained operational functionality.
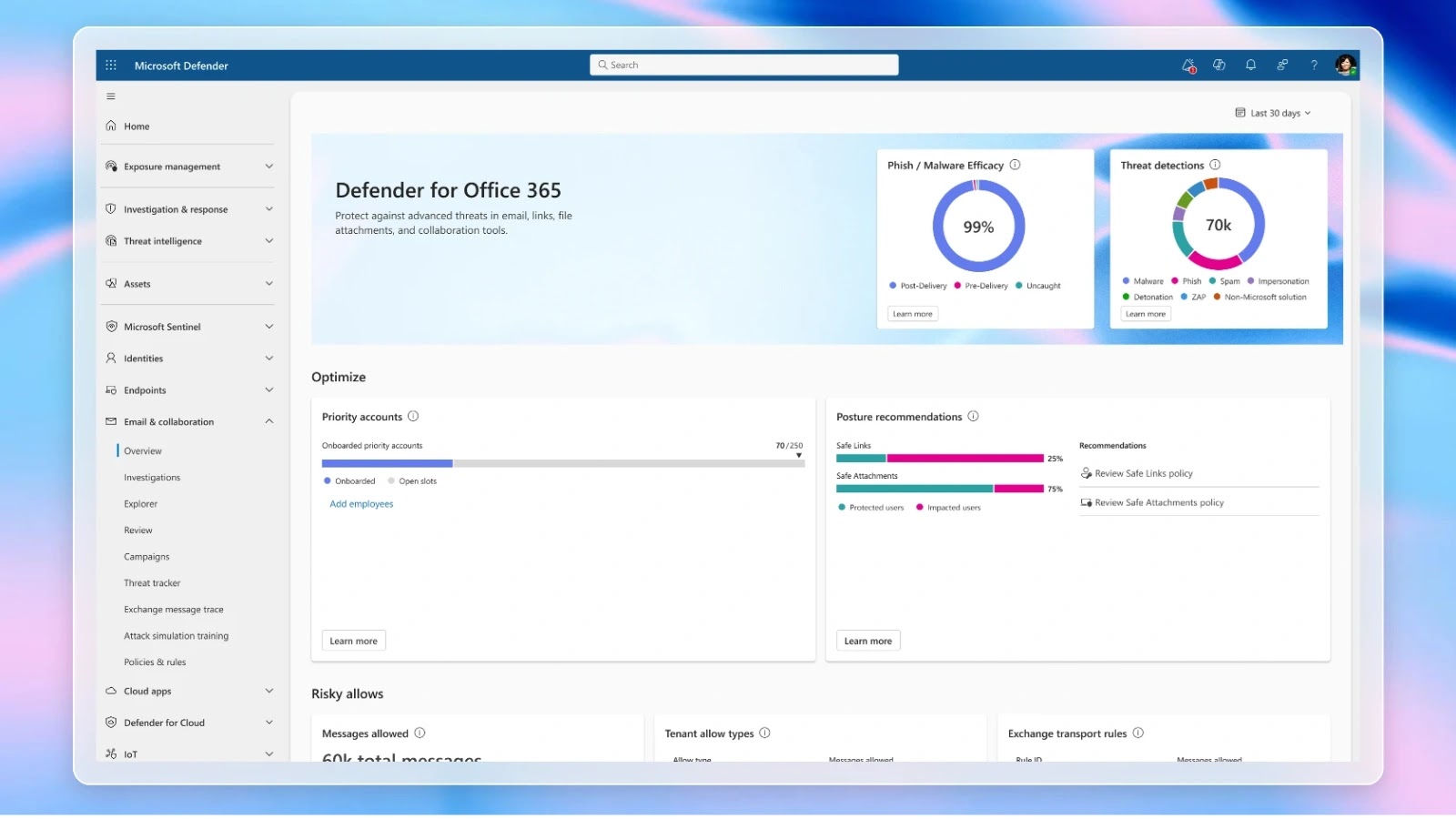
Detection requires behavioral monitoring via Endpoint Detection and Response options fairly than typical file scanning.
Safety groups ought to monitor irregular DLL loading from temp directories, suspicious youngster processes spawned from respectable executables, and outbound connections to cloud infrastructure instantly following doc execution.
The marketing campaign underscores how risk actors proceed refining their methodologies to use belief and technical detection gaps concurrently.
Observe us on Google Information, LinkedIn, and X to Get Extra Prompt Updates, Set CSN as a Most well-liked Supply in Google.