Cybersecurity experts have identified a significant vulnerability in Palo Alto Networks’ Cortex XDR security platform that permits attackers to circumvent behavioral detection mechanisms. This flaw was uncovered by researchers at InfoGuard Labs, who were able to reverse-engineer the encrypted rules meant to protect the system.
Decrypting the Detection Mechanism
Cortex XDR employs Behavioral Indicators of Compromise (BIOCs) to monitor and flag malicious activities. These rules are distributed in an encrypted format to prevent unauthorized access and modifications. However, during a red team assessment involving Cortex Windows agent versions 8.7 and 8.8, researchers managed to decrypt these rules.
Manuel Feifel from InfoGuard Labs used advanced kernel debugging tools to trace the decryption process. The team found that the decryption keys were derived from a hardcoded string within the agent’s files, combined with a plaintext Lua configuration file. This enabled the decryption of the entire rule set, allowing for comprehensive analysis.
The Evasion Technique Uncovered
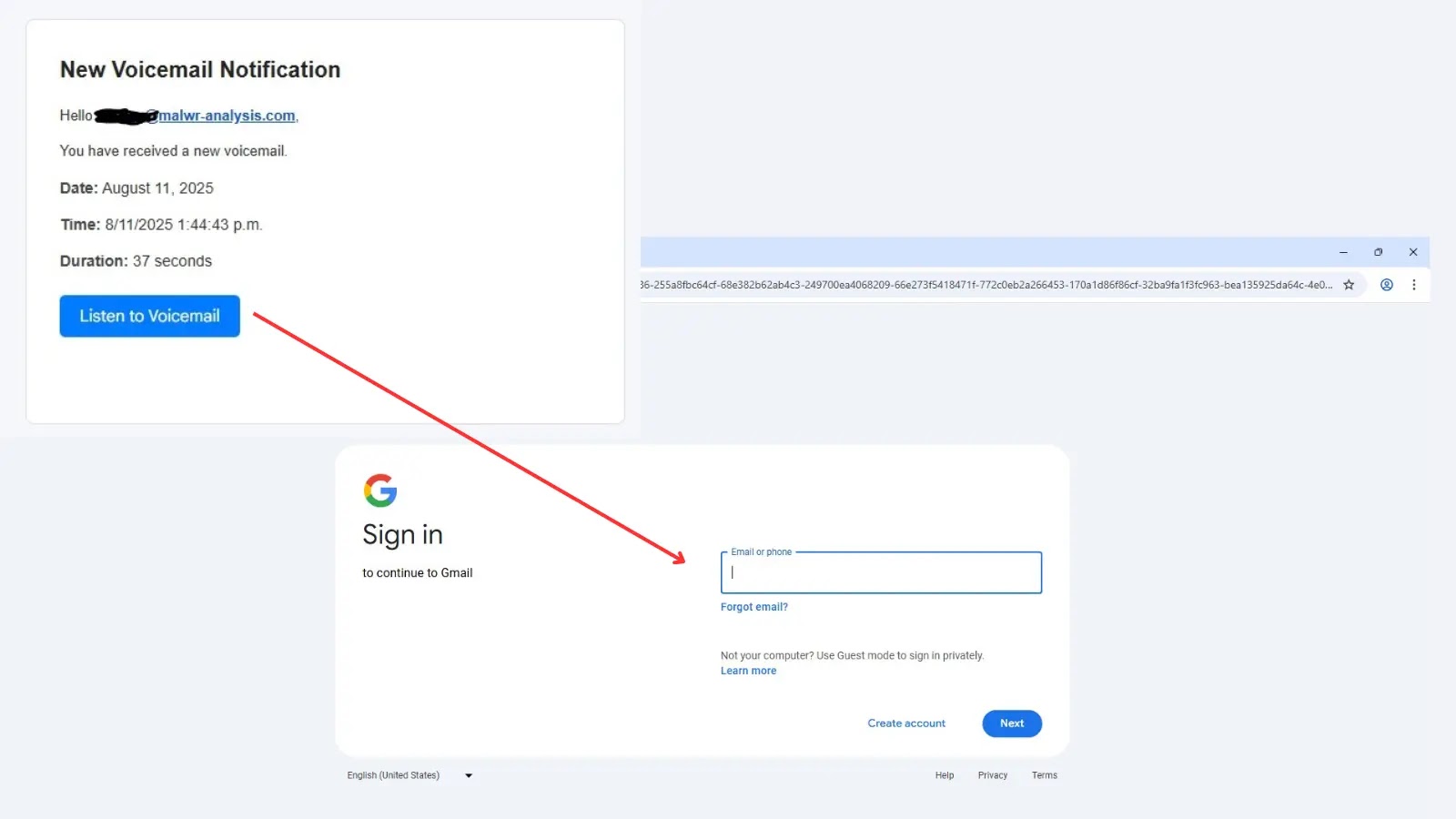
The decrypted rules revealed significant exceptions intended to prevent false positives, which attackers could exploit. The most notable finding was a global whitelist that could be misused to execute malicious operations.
One critical vulnerability was linked to a specific string, ‘Windowsccmcache’, in command-line arguments. If present, the Cortex XDR agent would exclude the process from monitoring, effectively creating a blind spot in the detection system. This single string allowed attackers to bypass approximately half of the platform’s behavioral detection rules.
Researchers demonstrated this vulnerability by using the SysInternals ProcDump utility. By appending the vulnerable string, they successfully executed a common credential theft technique without detection.
Industry Implications and Response
The InfoGuard Labs team disclosed their findings to Palo Alto Networks in July 2025. After a collaborative effort to protect users, Palo Alto released a comprehensive fix by February 2026. This incident underscores the risks associated with closed detection ecosystems that rely on encrypted, hidden rules.
While some vendors, like Elastic and HarfangLab, maintain open rule sets, closed systems like Cortex XDR can create a false sense of security if they contain fundamental flaws. Organizations are advised to thoroughly understand their security tools and avoid over-reliance on opaque detection solutions.
The decrypted rules and proof-of-concept scripts have been shared on GitHub, enabling the cybersecurity community to conduct further research and enhance threat detection capabilities.