Public studies about cyberattacks typically current a cultured image—menace actors working methodically by a well-planned playbook with each motion completely executed.
This notion leads many to imagine that trendy attackers function with machine-like precision, seamlessly transferring from one goal to a different with out dealing with obstacles.
Nonetheless, this narrative masks a a lot totally different actuality that turns into clear when inspecting the precise proof left behind on compromised methods.
A better take a look at Home windows Occasion Logs and endpoint detection and response (EDR) telemetry reveals one thing much more human: menace actors battle, experiment, make errors, and adapt when their plans fall quick.
Whoami.exe course of lineage (Supply – Huntress)
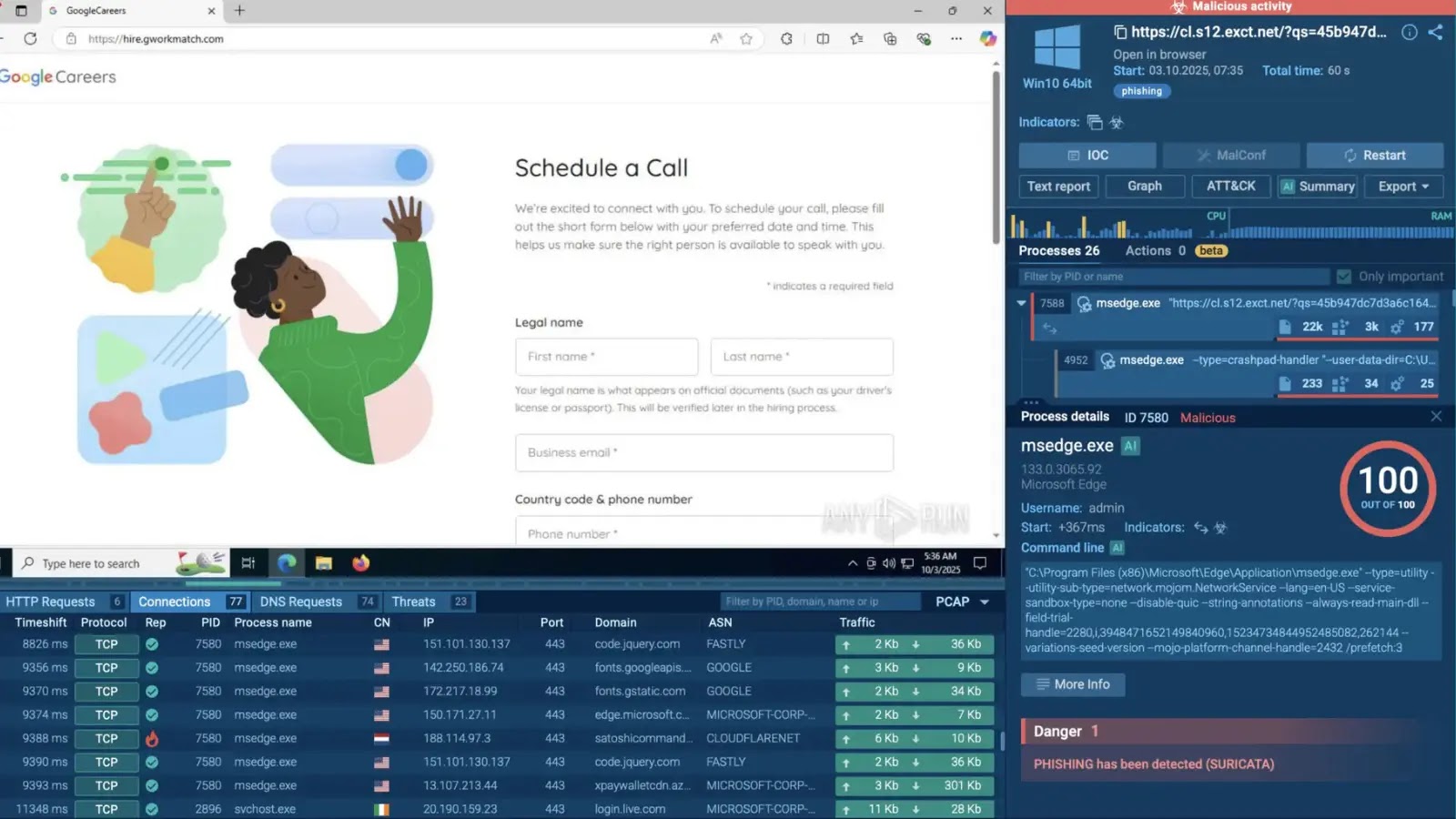
Between November and December 2025, three separate cyberattack incidents uncovered by safety researchers demonstrated precisely how trial and error form real-world malware campaigns.
These incidents shared a standard theme—attackers leveraging internet software vulnerabilities to realize preliminary entry, then trying to deploy customized malware whereas constantly adjusting their ways in response to defensive methods.
The incidents concerned a residential growth agency, a producing firm, and an enterprise shared providers group.
Throughout all three targets, the attackers exploited flaws in internet purposes working on Microsoft Web Data Server (IIS) to execute instructions remotely.
Huntress analysts recognized a Golang Trojan named agent.exe on the core of those assaults, although the attackers additionally deployed variations together with SparkRAT and different instruments to attain persistence on focused methods.
What made these assaults significantly noteworthy was not their sophistication, however the proof of studying and failure.
Home windows Defender detection of ‘ShellcodeRunner’ (Supply – Huntress)
Within the first incident, the menace actor confronted speedy detection when trying to obtain malware utilizing Home windows Defender—so in subsequent assaults, they modified their method by pre-emptively including Home windows Defender exclusions earlier than deploying their payload.
This sample demonstrates that menace actors reply to roadblocks relatively than executing good plans.
The attackers repeatedly tried to determine persistence utilizing Home windows providers, but these efforts steadily failed because of configuration errors and system limitations.
Regardless of these setbacks, the menace actors continued, returning to compromised endpoints a number of occasions with totally different instruments and strategies, every try revealing their frustration with defensive obstacles.
An infection Mechanism
Huntress analysts recognized that each one three incidents started with the identical elementary vulnerability sample—compromised IIS internet server processes executing attacker-controlled instructions.
The menace actors didn’t use conventional internet shells; as an alternative, they exploited coding flaws instantly inside internet software pages to attain distant command execution.
Within the first incident, server logs confirmed a POST request to a login web page returning successful standing code (200), instantly adopted by execution of the whoami.exe command by the net server course of.
Course of tree (Supply – Huntress)
This indicated the attacker had discovered a vulnerability permitting arbitrary command execution with out requiring an internet shell add. The menace actor then issued commonplace enumeration instructions: netstat, person account checks, and community configuration queries.
When trying to obtain malware utilizing certutil.exe—a standard Residing Off The Land binary approach—Home windows Defender blocked the command.
Moderately than abandoning the method, the menace actor transferred a file named 815.exe by an unknown mechanism and tried executing it 3 times earlier than lastly succeeding, solely to face isolation after the executable was recognized as a Golang-written Trojan.
In subsequent incidents, the attackers realized from failure. They issued PowerShell instructions so as to add exclusions for frequent malware file extensions earlier than deploying malware: powershell -command Add-MpPreference -ExclusionPath C -ExclusionExtension .exe, .bin, .dll -Pressure.
This adaptation proved crucial, because it demonstrated menace actors modifying habits based mostly on earlier setbacks, at the same time as they continued reusing the identical flawed persistence mechanisms that failed in earlier makes an attempt.
Observe us on Google Information, LinkedIn, and X to Get Extra Immediate Updates, Set CSN as a Most popular Supply in Google.