Since late 2025, cybercriminals have been leveraging a previously undisclosed zero-day vulnerability in Adobe Reader through malicious PDF files. Detailed by EXPMON’s Haifei Li, this sophisticated exploit has surfaced with documents like ‘Invoice540.pdf’ appearing on the VirusTotal platform. The initial instance was detected on November 28, 2025, followed by another upload on March 23, 2026.
Exploitation Tactics and Social Engineering
The strategically named PDF files suggest a social engineering component, enticing users to open these documents in Adobe Reader. Upon access, the files execute hidden JavaScript aimed at gathering sensitive information and facilitating additional payloads. A security researcher, Gi7w0rm, noted in an online post that these PDF files employ Russian language themes related to current events in the oil and gas sector.
Technical Breakdown of the Exploit
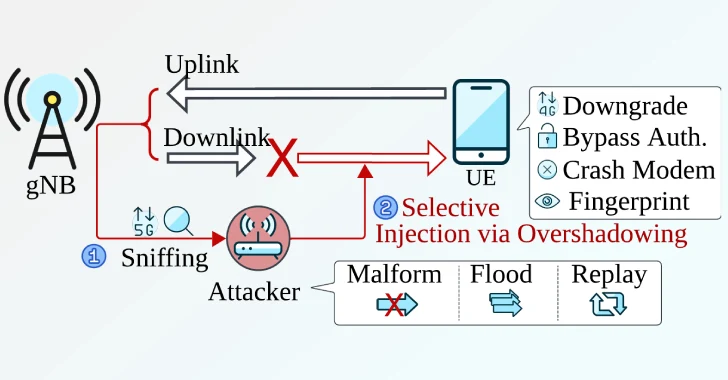
The vulnerability allows the execution of privileged Acrobat APIs in the latest Adobe Reader version, posing a significant threat. The exploit acts as an initial entry point for information collection and potential escalation to remote code execution (RCE) and sandbox escape (SBX) attacks. It also transmits collected data to a remote server, with the capacity to execute further JavaScript code.
Implications and Security Community Response
The potential for further exploitation is underscored by the possibility of collecting local data and advancing fingerprinting attacks. However, the exact nature of subsequent exploits remains unclear, as no response was received from the server, possibly due to unmet criteria in the testing environment. Despite this, Haifei Li emphasizes that the zero-day capability for broad data harvesting and possible RCE/SBX exploits necessitates heightened vigilance from the security community.
This story is under continuous development. Stay tuned for updates as more information becomes available.