Security experts have identified six new families of Android malware designed to steal data and execute financial fraud. These malware variants include PixRevolution, TaxiSpy RAT, BeatBanker, Mirax, Oblivion RAT, and SURXRAT. Each operates with unique methods to target financial transactions and user data.
Malware Targeting Pix Payments
PixRevolution is a significant threat to Brazil’s Pix payment system. As per Zimperium, this malware intercepts transactions, redirecting funds to attackers. It operates covertly until a Pix transaction is initiated, at which point it employs a human or AI operator to alter the transaction details.
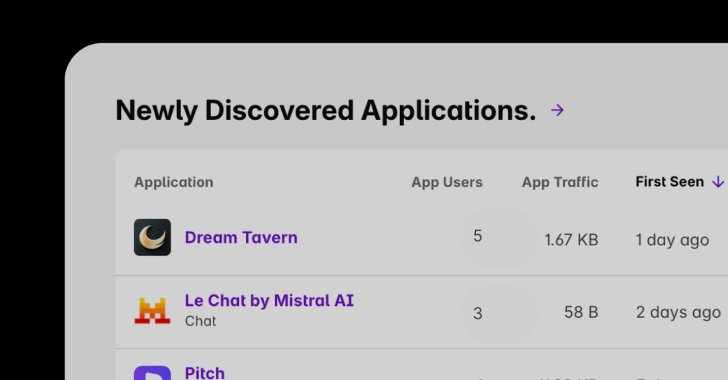
The malware tricks users by mimicking legitimate apps like Expedia and Sicredi on fake Google Play Store pages. Once installed, these apps request accessibility permissions to manipulate transactions and gather device data. PixRevolution’s primary function is to monitor screens and create overlays to deceive users, ultimately altering the recipient’s Pix key during transactions.
BeatBanker: An Evolving Threat
BeatBanker targets Brazilian users through phishing campaigns posing as Google Play Store sites. Notably, it uses a unique persistence strategy involving an audio loop to maintain its presence. The malware employs Google’s Firebase Cloud Messaging for command-and-control operations.
This malware incorporates a cryptocurrency miner and can hijack devices to spoof screens during USDT transactions. By monitoring various web browsers, it gathers personal information and controls devices remotely. Recent developments reveal BeatBanker deploying BTMOB RAT for enhanced control and surveillance capabilities.
Advanced Malware Techniques
TaxiSpy RAT exploits Android’s accessibility services to gather sensitive information, targeting Russian apps for credential theft. Using advanced evasion methods, it captures SMS, call logs, and more, leveraging Firebase for remote commands.
Mirax and Oblivion RAT have emerged as malware-as-a-service offerings, with Mirax advertising banking overlays and information gathering. Oblivion promises to bypass security features across major manufacturers, presenting a significant challenge to Android’s defenses.
SURXRAT, a commercial malware, uses accessibility permissions for persistent control, communicating with a Firebase-based infrastructure. Some samples even integrate AI elements, expanding their capabilities further.
The evolution of these malware families underscores ongoing attempts by cybercriminals to enhance their tools and exploit new technologies, posing a continuous threat to Android users worldwide.