Chief Information Security Officers (CISOs) face significant challenges when managing their Security Operations Centers (SOCs), particularly as the frontline Tier 1 analysts often lack the experience needed for optimal threat detection. This initial layer handles the bulk of alerts and performs the crucial task of initial triage, yet is frequently undermined by high turnover and alert overload, leading to potential risks for the business.
The Paradox of Tier 1 Analysts
Tier 1 analysts are essential for SOC performance yet often suffer from insufficient support and overwhelming cognitive demands. They handle vast amounts of alerts, which can lead to alert and decision fatigue, and increased burnout and turnover. These conditions transform Tier 1 performance into a business risk, as delays or errors in threat escalation can lead to increased dwell times and incident costs, ultimately degrading executive confidence in security measures.
Enhancing Monitoring and Triage Efficiency
Monitoring and alert triage are critical processes owned by Tier 1 analysts. These tasks involve monitoring signals from various sources and applying detection logic to identify potential threats. Inefficiencies in these processes can lead to Tier 2 and Tier 3 analysts being overwhelmed with noise, delayed incident responses, and increased operational costs. Effective threat intelligence is vital in providing the necessary context for Tier 1 analysts to make accurate and timely decisions.
Integrating Advanced Threat Intelligence
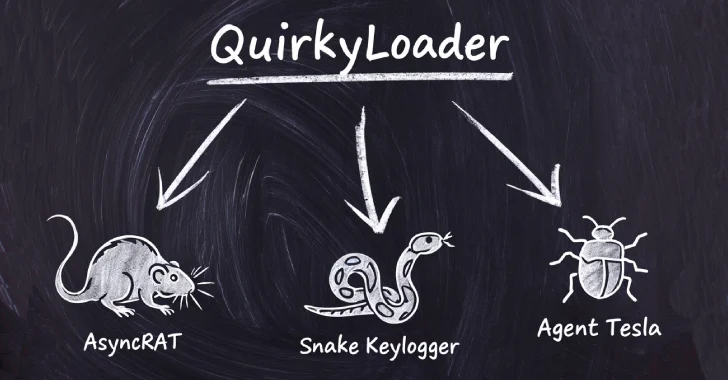
To improve Tier 1 efficiency, CISOs should integrate advanced threat intelligence feeds into their monitoring systems. These feeds provide real-time, verified indicators of compromise, enabling a more proactive approach to threat detection. By utilizing tools like the ANY.RUN’s Threat Intelligence Feeds, organizations can leverage real-world threat data to enhance detection precision and reduce mean time to detect (MTTD) and mean time to respond (MTTR).
The enrichment of alerts with actionable context is crucial for effective triage. Tools like the ANY.RUN Interactive Sandbox allow analysts to observe the behavior of suspicious files in real time, providing a deeper understanding of potential threats. This approach enhances decision-making confidence, reduces false positives, and supports better incident documentation and compliance.
Strategic Integration for Comprehensive Security
Strategic integration of threat intelligence into existing security infrastructure is critical for maximizing its value. By connecting tools like ANY.RUN’s feeds and sandbox capabilities with SIEMs, firewalls, and endpoint detection systems, organizations can ensure a cohesive and informed security posture. This integration reduces manual effort, allowing analysts to focus on investigation rather than information gathering, leading to faster and more effective threat response.
CISOs who prioritize these steps can transform their SOC into a proactive defense mechanism, significantly reducing organizational risk. By focusing on enhancing monitoring capabilities, enriching alert context, and strategically integrating threat intelligence, CISOs can ensure their SOC operates at peak efficiency, protecting the business from evolving threats.