Cybersecurity experts have uncovered details about a new cyber espionage campaign named CRESCENTHARVEST that appears to target supporters of Iran’s recent protests. The Acronis Threat Research Unit (TRU) identified the operation post-January 9, highlighting its aim to deploy a remote access trojan (RAT) and information stealer for executing commands, logging keystrokes, and extracting sensitive data. The success of these attacks remains unclear.
Exploitation of Geopolitical Events
The campaign leverages current geopolitical tensions, enticing victims with malicious .LNK files disguised as protest-related media. Researchers Subhajeet Singha, Eliad Kimhy, and Darrel Virtusio reported that these files come bundled with genuine content and a Farsi-language report on Iran’s protest activities. This approach aims to enhance credibility among Farsi-speaking individuals seeking protest updates.
CRESCENTHARVEST’s origins are not explicitly known, but it is suspected to be linked to an Iran-aligned threat group. This revelation marks it as the second identified campaign targeting specific individuals following nationwide protests that started in late 2025. Previously, French cybersecurity firm HarfangLab detailed a related threat cluster, RedKitten, which targeted NGOs and individuals documenting human rights abuses in Iran, using a custom backdoor called SloppyMIO.
Social Engineering Tactics
The initial method of delivering the malware remains uncertain, though spear-phishing and prolonged social engineering efforts are suspected. Iranian hacking groups such as Charming Kitten and Tortoiseshell are known for sophisticated operations, building trust with targets over time before delivering malicious payloads.
The Swiss-based security company noted the use of Farsi language and protest-themed files as a strategy to attract and exploit Farsi-speaking individuals supportive of the protests. The attack begins with a deceptive RAR archive, claiming to contain protest-related data, including images and videos, alongside two Windows shortcut files masquerading as media files using the double extension trick.
Technical Aspects of the Attack
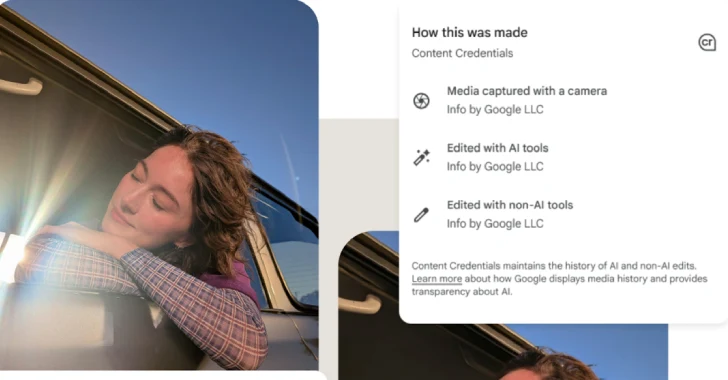
Once executed, the deceptive file uses PowerShell to download another ZIP archive while displaying a harmless image or video, misleading the victim. This ZIP archive contains a legitimate Google-signed binary and several DLL files, including two rogue libraries that are sideloaded to achieve the threat actor’s goals.
The CRESCENTHARVEST campaign employs Windows Win HTTP APIs for communication with its command-and-control server, blending with normal traffic. It supports various commands, such as anti-analysis checks, browser history theft, directory listing, keystroke logging, and more, highlighting its comprehensive capabilities.
Acronis stated that CRESCENTHARVEST continues a longstanding pattern of suspected state-sponsored cyber espionage targeting journalists, activists, researchers, and diaspora communities worldwide. Its tactics reflect well-established methods, including LNK-based access, DLL side-loading, credential harvesting, and event-aligned social engineering.