A critical remote code execution (RCE) vulnerability in Marimo, a widely used open-source Python tool for data science, was exploited just hours post-disclosure, as revealed by cybersecurity firm Sysdig. Identified as CVE-2026-39987, the flaw affects all Marimo versions up to and including 0.20.4, with a patch available in version 0.23.0.
Vulnerability Details and Exploitation
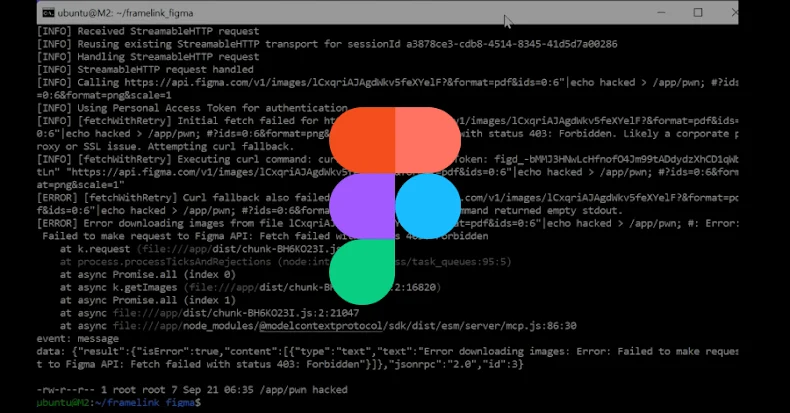
The vulnerability, rated with a CVSS score of 9.3, stems from insufficient authentication checks at the /terminal/ws WebSocket endpoint. This oversight allows attackers to execute arbitrary commands on the system without authentication, unlike other endpoints that require proper validation.
Within 9 hours and 41 minutes of its public disclosure, the vulnerability witnessed its first exploitation attempt. Attackers, leveraging the security lapse, gained unauthorized shell access to Marimo instances, highlighting the urgency of patching the affected systems.
Threat Actor Activity and Methods
The exploitation was traced to an unknown actor who accessed a honeypot system via the vulnerable WebSocket endpoint. The adversary conducted manual reconnaissance to explore the file system, focusing on sensitive files like the .env file and SSH keys.
Sysdig reported that the attacker engaged in this activity four times over 90 minutes, seemingly following a systematic approach to confirm findings and assess the presence of other threat actors, though no additional malware was deployed.
Implications for Cybersecurity
The rapid exploitation of this flaw underscores a broader trend where threat actors swiftly act on newly disclosed vulnerabilities, often before patches are widely adopted. This trend challenges defenders to respond promptly to public vulnerability announcements.
Experts warn that any application with a critical vulnerability, regardless of its user base size, is a potential target. The Marimo RCE exploitation serves as a stark reminder of the need for rigorous security measures and swift patch management to mitigate risks.
In conclusion, the Marimo incident exemplifies the crucial need for vigilance in vulnerability management, ensuring timely updates to safeguard systems against emerging threats.