Interlock Ransomware Targets Cisco Vulnerability
Amazon Threat Intelligence has identified an ongoing Interlock ransomware campaign exploiting a critical vulnerability in Cisco’s Secure Firewall Management Center (FMC) Software. Known as CVE-2026-20131, this vulnerability has a perfect CVSS score of 10.0 and involves insecure deserialization of a Java byte stream, allowing unauthorized remote attackers to execute code as root on affected devices.
According to Amazon, the flaw has been actively exploited as a zero-day since January 26, 2026, well before Cisco publicly disclosed it. CJ Moses, Amazon’s CISO, highlighted the urgency of this issue, noting that attackers had a significant advantage before defenders could even respond. Amazon’s MadPot global sensor network was crucial in uncovering this exploitation, which they promptly reported to Cisco.
Details of the Exploit and Attack Chain
The attack begins with crafted HTTP requests targeting specific paths in the vulnerable software to execute arbitrary Java code. Once compromised, the system sends an HTTP PUT request to an external server, confirming the exploitation’s success. The next phase involves downloading an ELF binary from a remote server, which hosts additional tools linked to the Interlock group.
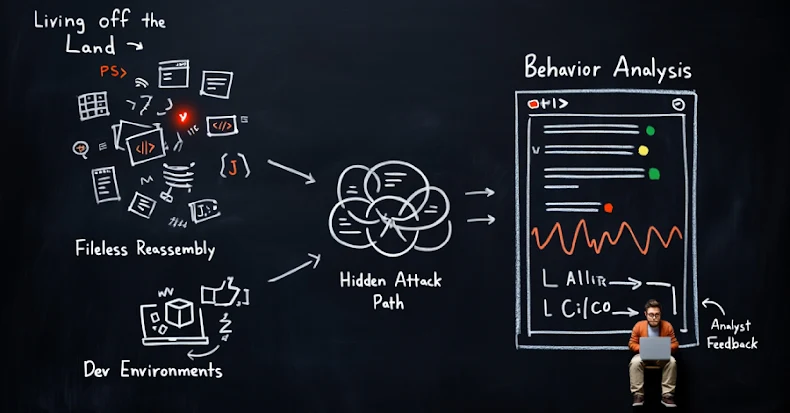
These tools include a PowerShell script for Windows environment reconnaissance, gathering system details, and a variety of custom remote access trojans for command execution and file transfer. There is also a Bash script that configures Linux servers as HTTP reverse proxies, obscuring the attacker’s origins and aiding in evasion.
Tools and Techniques Used by Interlock
Interlock employs a range of sophisticated tools and techniques. A memory-resident web shell inspects requests for encrypted payloads, which are decrypted and executed. A lightweight network beacon checks for successful code execution and network reachability post-exploitation.
Additional tools include ConnectWise ScreenConnect for persistent remote access and Volatility Framework for memory forensics. The threat actor’s identity is linked to specific operational indicators, including a unique ransom note and TOR negotiation portal, suggesting activity in the UTC+3 time zone.
Recommendations and Broader Implications
In response to the active exploitation, users are urged to apply patches immediately, assess security measures, and scrutinize ScreenConnect installations for unauthorized access. The incident underscores the challenges posed by zero-day exploits and the necessity of defense-in-depth strategies to protect organizations during the critical window before patches are available.
Google’s recent findings indicate that ransomware actors are adapting their tactics due to declining ransom payments, focusing more on vulnerabilities in VPNs and firewalls. The reliance on built-in Windows tools and compromised credentials for initial access is becoming more common, reflecting a shift in attack strategies.
Despite these changes, ransomware remains a significant global threat. As profits decline, threat actors might explore alternative monetization methods, such as data theft or using compromised infrastructure for secondary malicious activities.