In a significant cybersecurity development, North Korean hackers have reportedly unleashed over 1,700 malicious packages across npm, PyPI, Go, Rust, and other ecosystems. This operation, known as Contagious Interview, aims to undermine software supply chains by mimicking legitimate developer tools while secretly deploying malware. This finding was highlighted in a recent report by Socket security researcher Kirill Boychenko.
Malicious Packages Targeting Developers
The hackers have strategically targeted various programming ecosystems, including Go, Rust, and PHP, to distribute their harmful packages. These packages are designed to act as loaders, fetching malware with infostealer and remote access trojan (RAT) capabilities. The primary targets include web browsers, password managers, and cryptocurrency wallets. Notably, a Windows variant, delivered via ‘license-utils-kit’, features a comprehensive post-compromise toolkit capable of executing shell commands, keylogging, and more.
Boychenko notes the sophisticated nature of these attacks, which involve embedding malicious code within legitimate functions. For instance, in the Rust ecosystem, the ‘logtrace’ package conceals its payload within the ‘Logger::trace(i32)’ method. This subtlety ensures that the malicious code remains undetected during installation, posing a significant threat to developer environments.
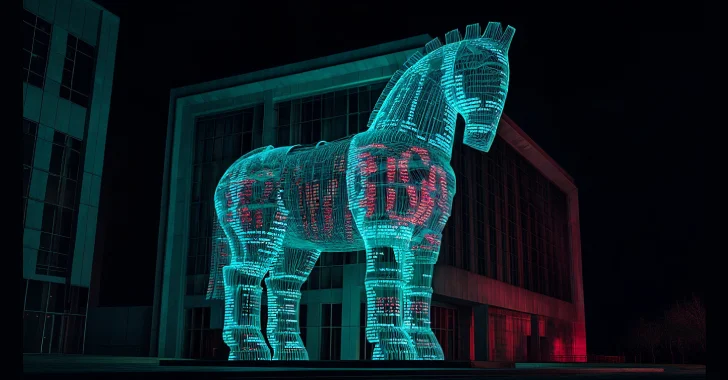
Implications of the Supply Chain Attack
This campaign is part of a broader effort by North Korean groups to compromise software supply chains. The attackers have extended their reach across various open-source platforms, aiming to gain initial access for espionage and financial theft. Since January 2025, over 1,700 malicious packages have been linked to this activity, signifying the scale and persistence of the threat.
Additionally, the campaign has involved the manipulation of popular npm packages such as Axios, used to distribute the WAVESHAPER.V2 implant. This was achieved by compromising the package maintainer’s account through tailored social engineering tactics. The group responsible, identified as UNC1069, shares affiliations with other known entities like BlueNoroff and Stardust Chollima.
Social Engineering and Broader Threats
The hackers employ sophisticated social engineering techniques, including impersonating credible contacts and brands on platforms like Telegram and Slack. By creating fake meeting links for services like Zoom and Microsoft Teams, they execute malware that communicates with attacker-controlled servers for data theft.
Security experts emphasize the patience of these attackers, as compromised devices often remain inactive for extended periods before exploitation. This strategic delay maximizes the hackers’ ability to extract valuable information before detection. Microsoft has observed consistent evolution in their tactics, indicating ongoing adaptation and persistence in their operations.
In conclusion, the activities of North Korean hackers pose a significant threat to global cybersecurity. Their ability to infiltrate software supply chains across multiple ecosystems highlights the need for enhanced vigilance and improved security measures. As these attacks evolve, organizations must remain proactive in identifying and mitigating potential threats.