The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) has imposed sanctions on six individuals and two entities linked to a scheme operated by the Democratic People’s Republic of Korea (DPRK). This network of information technology (IT) workers is accused of defrauding U.S. businesses to generate funds for North Korea’s weapons of mass destruction (WMD) programs.
Sanctioned Entities and Individuals
According to the Treasury, North Korean IT operatives target American companies by using deceptive tactics to extract payments, manipulating sensitive data, and engaging in extortion. The fraudulent operation, known by names such as Coral Sleet and PurpleDelta, uses fake documents and identities to secure employment in legitimate firms, channeling a significant portion of the earnings back to North Korea for illicit activities.
Among those sanctioned is the Amnokgang Technology Development Company, responsible for managing overseas IT workers and engaging in illegal procurement of military technology. Also targeted is Nguyen Quang Viet, CEO of a Vietnamese firm that converted millions into cryptocurrency, facilitating transactions for North Koreans.
Cybersecurity Concerns and International Operations
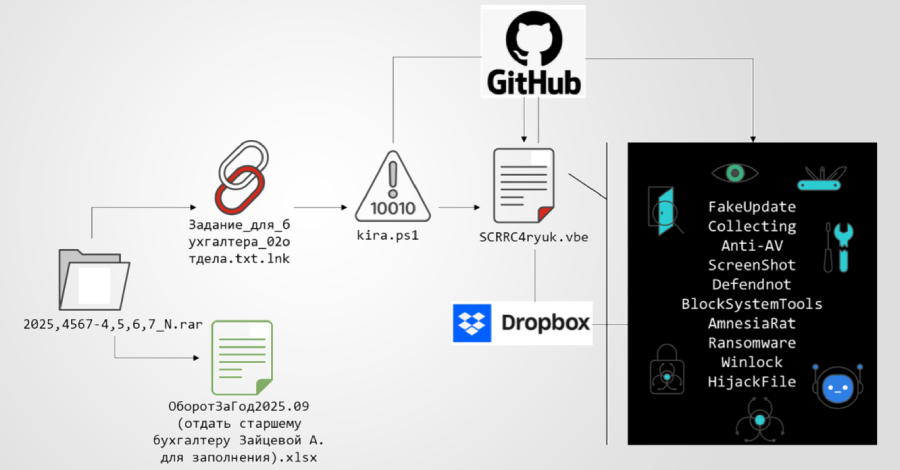
These operations are often supported by malware that steals proprietary information and demands ransoms to prevent data leaks. The tactics involve leveraging VPN services like Astrill to bypass geographic barriers, allowing operatives to appear as domestic employees by routing traffic through U.S. nodes.
Security experts highlight the network’s use of Astrill VPN to operate clandestinely from countries like China, where internet infrastructure is more reliable. These VPN services help mask the true origin of the operatives, contributing to their ability to conduct unrestricted global operations.
Role of Artificial Intelligence in Threat Operations
The network’s sophistication extends to the use of artificial intelligence (AI) in creating convincing digital personas and fake company websites. AI tools like Faceswap are employed to fabricate identities, enhancing the credibility of job applications with realistic digital headshots.
This technological edge allows North Korean IT workers to maintain extended and trusted access within organizations. The threat actors exploit AI to streamline operations, including malware development and social engineering, heightening the challenge for cybersecurity defenses worldwide.
Reports by cybersecurity firms Flare and IBM X-Force reveal a complex operational structure behind the IT worker scheme, involving recruiters, facilitators, and collaborators. These roles collectively enable North Korean operatives to infiltrate organizations and evade detection, contributing to the DPRK’s broader revenue-generation efforts.
The involvement of Western collaborators, often recruited through platforms like LinkedIn and GitHub, further bolsters the scheme’s reach and effectiveness, underscoring the pervasive nature of North Korea’s IT worker operations in circumventing international sanctions.