Introduction: Preparing for the Quantum Leap in Cybersecurity
As digital transformation accelerates, the necessity for robust security measures becomes ever more critical. The evolution of technology often outpaces our ability to protect against its misuse, leading to an urgent need to address potential threats. This is especially true in cybersecurity, where the advent of quantum computing could soon present significant challenges. Experts emphasize the importance of preparing for post-quantum cryptography (PQC) to safeguard against future risks.
The Rising Threat of Advanced Cyber Attacks
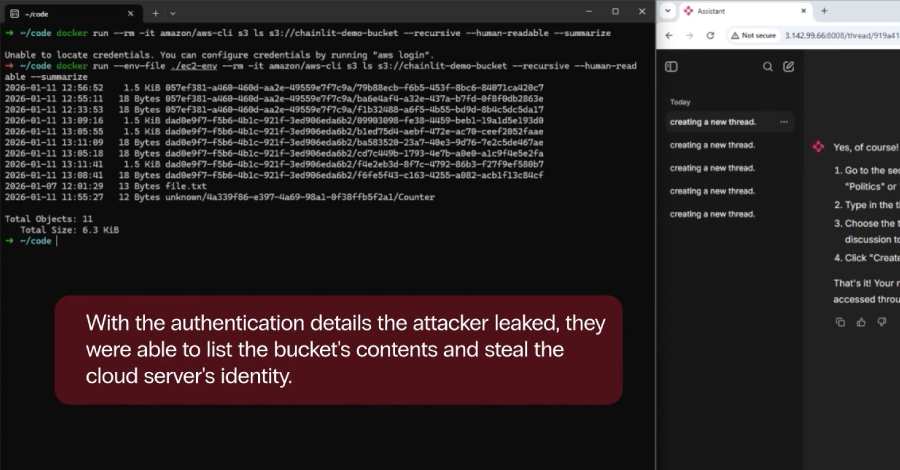
With the increased sophistication of cybercrime, fueled by the profitability of ransomware and cyber extortion, a professional criminal network has emerged. These threats are exacerbated by the widespread adoption of cloud services, which, while offering enhanced accessibility, also present new vulnerabilities. As adversaries capitalize on these technological advancements, the potential for quantum computing to break current encryption methods becomes a looming concern.
Current encryption techniques, which protect sensitive data, may become obsolete in the face of quantum computing’s capabilities. This technological leap could enable malicious actors to decrypt information that was previously considered secure, potentially leading to massive data breaches and the exploitation of critical information.
The Urgency of Transitioning to Post-Quantum Cryptography
To mitigate these impending risks, cybersecurity experts recommend an immediate shift towards post-quantum cryptography. PQC involves developing encryption methods that can withstand the computational power of quantum computers. By transitioning to these new standards now, organizations can ensure their data remains secure in the future.
Proactive measures are essential to prevent the exploitation of stolen data. Once quantum computing becomes mainstream, encrypted data obtained today could be decrypted, exposing sensitive information. This prospect underscores the urgency for businesses and governments to adopt PQC solutions promptly.
Future Outlook: A Call to Action for Cybersecurity
As the digital landscape continues to evolve, the importance of forward-thinking cybersecurity strategies cannot be overstated. The transition to post-quantum cryptography represents a critical step in protecting information against future threats. Organizations must prioritize the implementation of PQC to stay ahead of potential cybersecurity challenges.
By acting now, businesses can safeguard their data and maintain trust with their stakeholders. The integration of PQC solutions will not only enhance security but also position organizations to thrive in an era where quantum computing becomes a reality. Embracing these changes is essential to ensuring a secure digital future.