In a significant cybersecurity revelation, a financially driven cyber operation, named REF1695, has been actively distributing remote access trojans (RATs) and cryptocurrency mining software using counterfeit installers since November 2023. Elastic Security Labs, with researchers Jia Yu Chan, Cyril François, and Remco Sprooten, highlighted that the operation, beyond cryptomining, also profits from CPA fraud by leading users to misleading content registration pages.
The campaign’s latest versions have introduced a novel .NET implant known as CNB Bot. These attacks exploit ISO files to deploy a .NET Reactor-protected loader alongside a text file, instructing users on bypassing Microsoft Defender SmartScreen to run unverified applications by selecting ‘More info’ and ‘Run anyway’.
Technical Details and Infection Process
The infection process involves a loader that initiates PowerShell to configure Microsoft’s antivirus exclusions, allowing CNB Bot to operate undetected. Users encounter an error message stating that their system cannot launch the application, suggesting support contact. CNB Bot acts as a loader with functionalities for downloading and executing additional payloads, self-updating, and performing cleanup operations to erase traces, communicating with a command-and-control (C2) server via HTTP POST requests.
Similar operations by the threat actor employ ISO files to spread PureRAT, PureMiner, and a custom XMRig loader. This loader fetches mining configurations from a hard-coded URL to activate the miner. In the FAUX#ELEVATE campaign, a legitimate yet vulnerable Windows kernel driver, ‘WinRing0x64.sys’, is exploited to access hardware at the kernel level, optimizing CPU settings for enhanced hash rates, a tactic used in cryptojacking since December 2019.
Impact and Financial Gains
The operation has also been linked to deploying SilentCryptoMiner, which uses direct system calls to remain undetected, disables Windows sleep and hibernate functions, and establishes persistence through scheduled tasks. It too employs the ‘Winring0.sys’ driver to optimize CPU performance for mining. A watchdog process ensures that malicious components and persistence techniques are reinstated if removed. This campaign has reportedly amassed 27.88 XMR, equivalent to $9,392, indicating substantial financial benefits.
Infrastructure and Defense Strategies
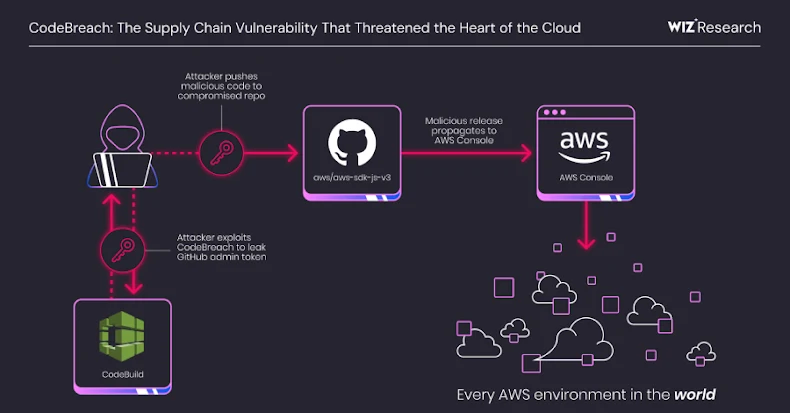
Elastic Security noted the use of GitHub as a delivery platform for payloads, with staged binaries hosted across two accounts. This approach shifts the download and execution processes from attacker-controlled infrastructure to a reputable platform, thereby reducing detection possibilities. The use of such trusted platforms makes defense strategies more challenging, emphasizing the need for improved detection and response mechanisms.
This revelation underscores the evolving tactics of cybercriminals, highlighting the importance of robust cybersecurity measures and vigilance against sophisticated cyber schemes.