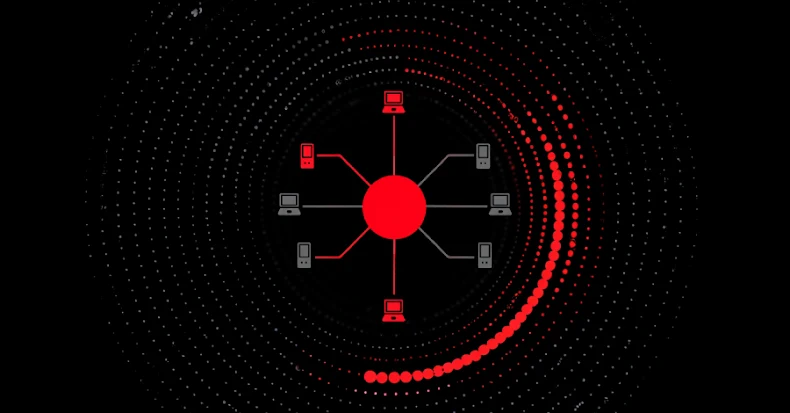
Malware campaigns distributing the RondoDox botnet have expanded their focusing on focus to take advantage of greater than 50 vulnerabilities throughout over 30 distributors.
The exercise, described as akin to an “exploit shotgun” strategy, has singled out a variety of internet-exposed infrastructure, together with routers, digital video recorders (DVRs), community video recorders (NVRs), CCTV programs, internet servers, and numerous different community units, in keeping with Pattern Micro.
The cybersecurity firm mentioned it detected a RondoDox intrusion try on June 15, 2025, when the attackers exploited CVE-2023-1389, a safety flaw in TP-Hyperlink Archer routers that has come underneath lively exploitation repeatedly because it was first disclosed in late 2022.
RondoDox was first documented by Fortinet FortiGuard Labs again in July 2025, detailing assaults aimed toward TBK digital video recorders (DVRs) and 4-Religion routers to enlist them in a botnet for finishing up distributed denial-of-service (DDoS) assaults towards particular targets utilizing HTTP, UDP, and TCP protocols.
“Extra not too long ago, RondoDox broadened its distribution through the use of a ‘loader-as-a-service’ infrastructure that co-packages RondoDox with Mirai/Morte payloads – making detection and remediation extra pressing,” Pattern Micro mentioned.
RondoDox’s expanded arsenal of exploits contains practically 5 dozen safety flaws, out of which 18 do not have a CVE identifier assigned. The 56 vulnerabilities span numerous distributors resembling D-Hyperlink, TVT, LILIN, Fiberhome, Linksys, BYTEVALUE, ASMAX, Brickcom, IQrouter, Ricon, Nexxt, NETGEAR, Apache, TBK, TOTOLINK, Meteobridge, Digiever, Edimax, QNAP, GNU, Dasan, Tenda, LB-LINK, AVTECH, Zyxel, Hytec Inter, Belkin, Billion, and Cisco.
“The newest RondoDox botnet marketing campaign represents a major evolution in automated community exploitation,” the corporate added. “It is a clear sign that the marketing campaign is evolving past single-device opportunism right into a multivector loader operation.”
Late final month, CloudSEK revealed particulars of a large-scale loader-as-a-Service botnet distributing RondoDox, Mirai, and Morte payloads by means of SOHO routers, Web of Issues (IoT) units, and enterprise apps by weaponizing weak credentials, unsanitized inputs, and previous CVEs.
The event comes as safety journalist Brian Krebs famous that the DDoS botnet often known as AISURU is “drawing a majority of its firepower” from compromised IoT units hosted on U.S. web suppliers like AT&T, Comcast, and Verizon. One of many botnet’s operators, Forky, is alleged to be primarily based in Sao Paulo, Brazil, and can be linked to a DDoS mitigation service referred to as Botshield.
In latest months, AISURU has emerged as one of many largest and most disruptive botnets, answerable for a number of the record-setting DDoS assaults seen up to now. Constructed on the foundations of Mirai, the botnet controls an estimated 300,000 compromised hosts worldwide.
The findings additionally comply with the invention of a coordinated botnet operation involving over 100,000 distinctive IP addresses from a minimum of 100 nations focusing on Distant Desktop Protocol (RDP) providers within the U.S., per GreyNoise.
The exercise is claimed to have commenced on October 8, 2025, with the vast majority of the site visitors originating from Brazil, Argentina, Iran, China, Mexico, Russia, South Africa, Ecuador, and others.
“The marketing campaign employs two particular assault vectors – RD Net Entry timing assaults and RDP internet consumer login enumeration – with most collaborating IPs sharing one related TCP fingerprint, indicating centralized management,” the risk intelligence agency mentioned.