On November seventh, safety researchers found a harmful malicious npm package deal known as “@acitons/artifact” that had already been downloaded greater than 206,000 occasions.
The package deal was designed to seem like the professional “@actions/artifact” package deal utilized by builders constructing instruments with GitHub Actions.
This was a basic typosquatting assault the place the attackers swapped the letters to make the title seem appropriate at first look.
The malware’s purpose was clear and centered. When this package deal was put in throughout a construct course of in GitHub-owned repositories, it could steal authentication tokens accessible within the construct surroundings.
With these tokens, attackers may then publish new malicious code immediately from GitHub’s personal account, making a critical menace to your complete platform’s safety.
The assault labored by way of a hidden set up script embedded within the package deal. Particularly, six variations of the malicious package deal included a post-install hook that routinely downloaded and ran hidden malware code.
Veracode safety analysts recognized that this malware was not detected by widespread antivirus software program when first found, making it particularly harmful to organizations counting on these safety instruments.
This marketing campaign highlights a crucial vulnerability within the software program provide chain, which is why it ranked because the third most vital safety concern within the OWASP High 10 2025 listing.
The assault focused GitHub’s steady integration and steady deployment platform, displaying how criminals are more and more specializing in the instruments that builders belief each day.
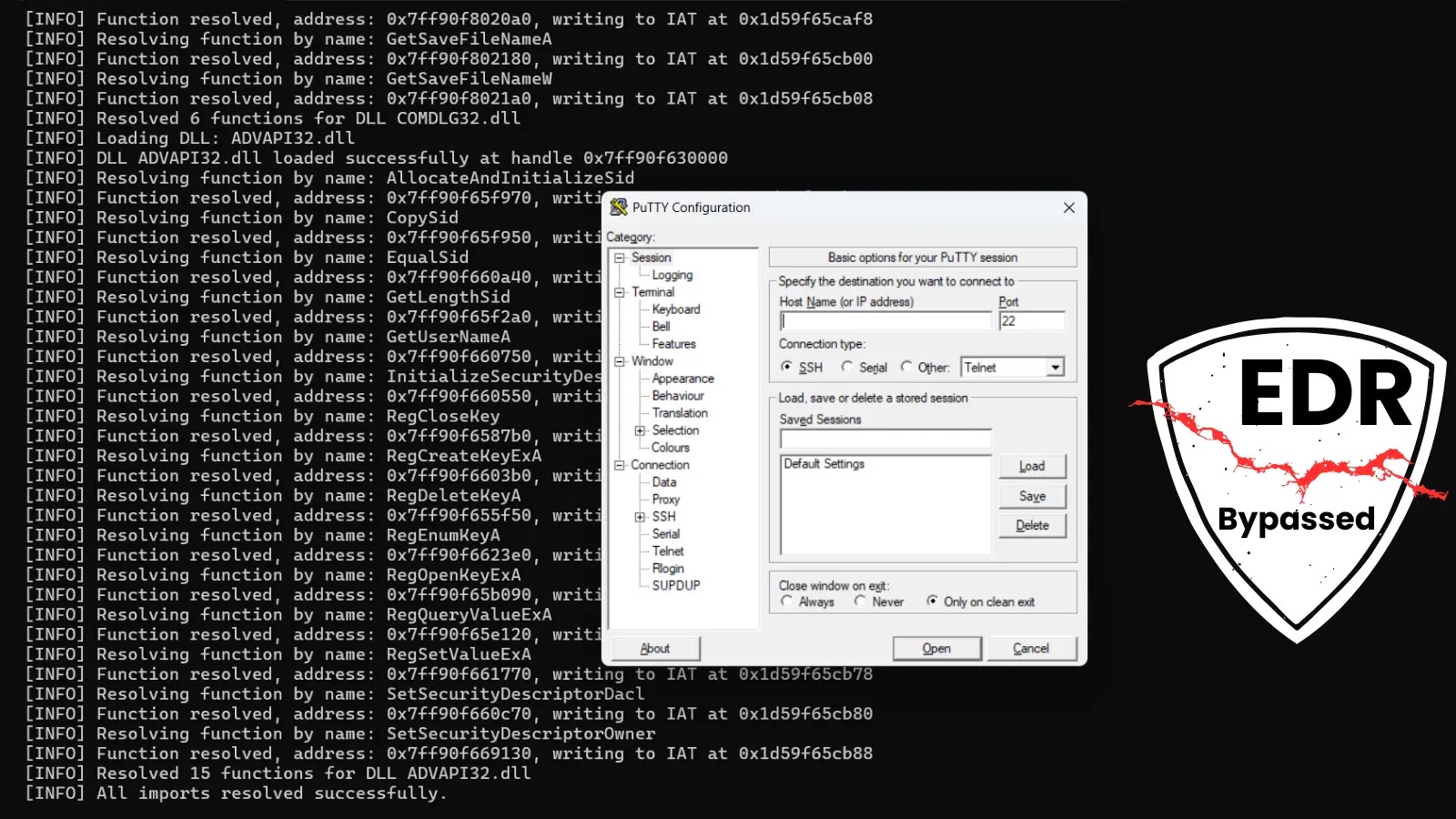
Veracode safety researchers famous that the malware used intelligent strategies to cover its true habits and keep away from automated detection.
Malicious code
The malicious code was obfuscated and compiled utilizing particular instruments that convert shell scripts into binary information, making it tougher to investigate.
The package deal contained a selected mechanism to cease working after a sure date, with every model set to run out inside days of launch.
This time-based set off suggests the attackers had been testing completely different variations of their code whereas staying hidden from safety programs.
The an infection mechanism labored in phases. When put in, the malware executed as a bash script that reset its personal surroundings variables to alter the way it ran.
This triggered the loading of an obfuscated file known as “confirm.js” hidden inside a Node package deal. The confirm.js file contained checks for particular GitHub surroundings variables that solely exist when code runs inside GitHub Actions.
The code particularly focused solely repositories owned by the GitHub group itself, confirming this was a precision assault.
The malware obtained an encryption key from an exterior server, encrypted the stolen tokens, after which despatched this encrypted knowledge to a command and management server.
Builders utilizing Veracode’s Package deal Firewall had been protected against this menace instantly after the invention, however the incident demonstrates how susceptible package deal managers stay to those refined provide chain assaults.
Comply with us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most popular Supply in Google.