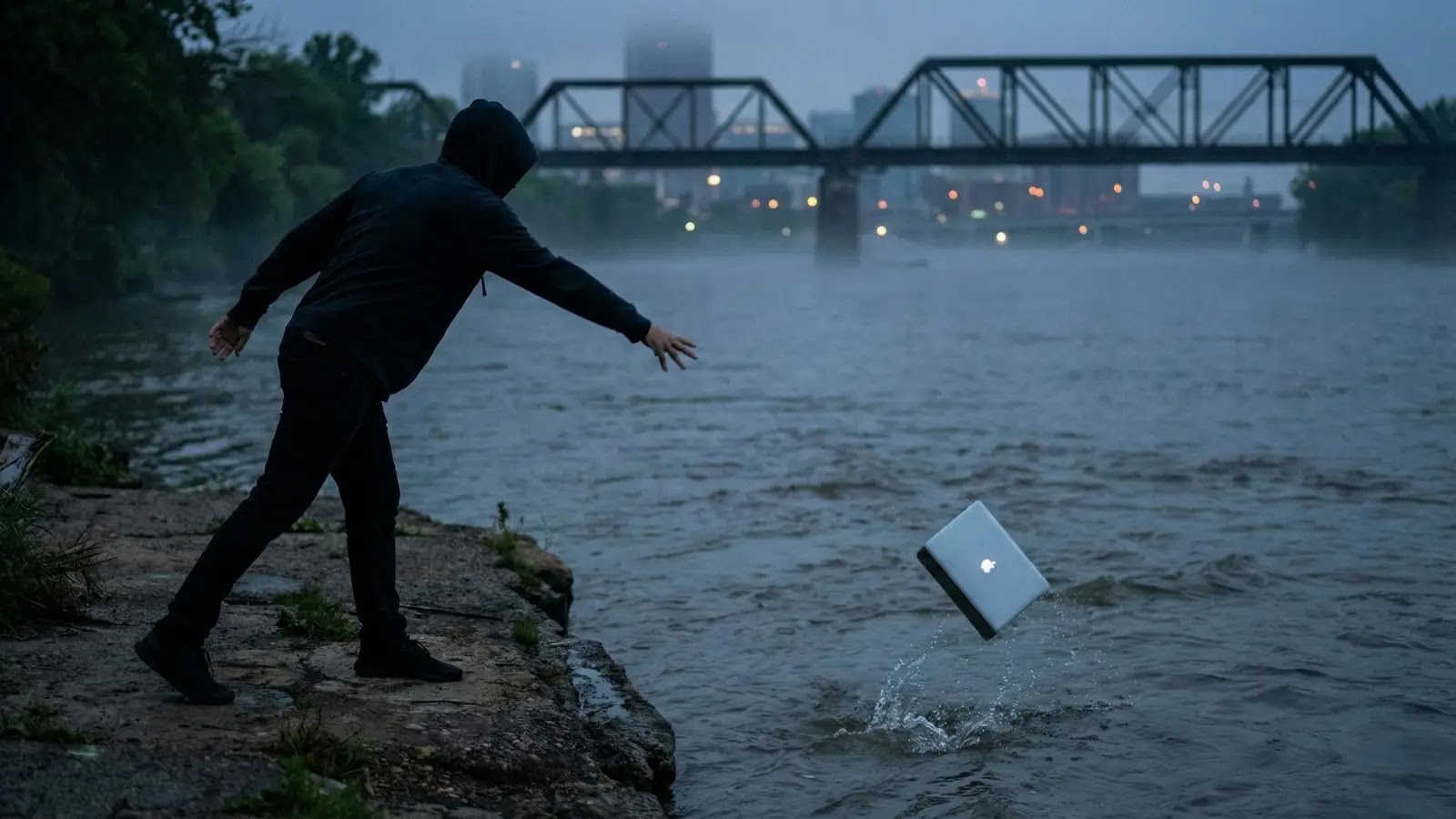
In a determined try and cowl his tracks, the hacker behind Coupang’s large private knowledge leak hurled his MacBook Air into a close-by river, just for firm investigators to fish it out days later.
This cinematic twist emerged as South Korean e-commerce big Coupang detailed its government-directed probe into the breach affecting 33.7 million clients, whereas unveiling a 1.685 trillion gained ($1.2 billion) compensation package deal to rebuild belief.
The incident unfolded after Coupang disclosed in late November that hackers had accessed delicate consumer knowledge, together with names, addresses, and cellphone numbers.
Public criticism elevated amid claims of a weak response, however on December 26, the corporate clarified that it was not a solo effort. As an alternative, beginning December 1, Coupang labored below every day authorities oversight to coordinate a multi-week operation monitoring the attacker.
Official letters and directives guided each step. On December 9, authorities instructed Coupang to succeed in out to the leaker, fastidiously scripting messages.
Preliminary conferences occurred on the 14th, yielding a full confession, desktop, arduous drives, and sworn testimony, all promptly handed over. By December 16, main units had been secured; on the seventeenth, they reached authorities analysts.
The plot thickened on December 18: Responding to additional orders, Coupang’s forensics staff retrieved the submerged MacBook Air, documented it in a chain-of-custody model, and delivered it instantly.
Further arduous drives and three fingerprinted declarations adopted on December 21 and had been routed to the police. Coupang maintained radio silence per a authorities mandate, whilst media and lawmakers criticized it.
“This was no self-investigation,” Coupang emphasised, countering “false insecurity” from misreports. The agency briefed officers on December 23 and up to date clients on the twenty fifth, vowing full cooperation towards secondary harms.
Quick-forward to December 29: Interim CEO Harold Rogers introduced the unprecedented voucher blitz, equal to 50,000 gained ($37) per affected account overlaying WOW members, cancellations, and all notified customers.
Beginning January 15, texts will alert recipients to 4 single-use coupons through the app: 5,000 gained every for core Coupang merchandise (Rocket Supply, and so on.) and Eats; 20,000 gained apiece for Journey and luxurious R.LUX.
Rogers expressed deep remorse: “We deeply remorse the misery induced… That is our accountable motion.” He pledged a “customer-centric” pivot: “We’ll remodel into an organization clients belief.”
Cybersecurity consultants hail the restoration as a win towards knowledge destruction ways, however questions linger on prevention. Coupang’s saga underscores provide chain dangers in cloud-scale retail, the place one insider breach ripples into billions.
Observe us on Google Information, LinkedIn, and X for every day cybersecurity updates. Contact us to function your tales.