Jan 07, 2026The Hacker NewsThreat Detection / Endpoint Safety
Safety groups are nonetheless catching malware. The issue is what they don’t seem to be catching.
Extra assaults immediately do not arrive as information. They do not drop binaries. They do not set off basic alerts. As a substitute, they run quietly via instruments that exist already contained in the atmosphere — scripts, distant entry, browsers, and developer workflows.
That shift is making a blind spot.
Be part of us for a deep-dive technical session with the Zscaler Web Entry crew. They may reveal the best way to unmask “hidden-in-plain-sight” ways, why conventional defenses fall quick, and precisely what wants to alter.
Safe your spot for the dwell session ➜
On this session, consultants will cowl:
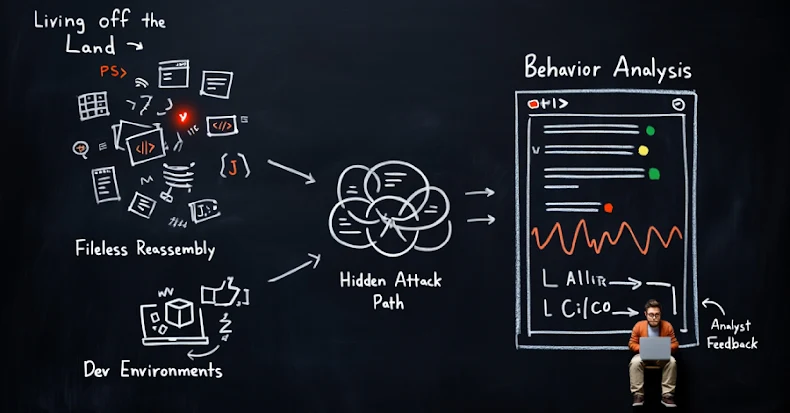
“Dwelling off the Land” Assaults: These use trusted system instruments like PowerShell, WMI, or distant desktop. File-based detection usually sees nothing incorrect as a result of, technically, nothing new was put in.
Fileless “Final Mile” Reassembly Assaults: Obfuscated HTML and JavaScript can execute malicious logic with out ever delivering a transparent payload to the endpoint. Legacy instruments battle right here as a result of there isn’t any file to scan.
Securing Developer Environments: CI/CD pipelines and third-party repositories transfer quick and rely closely on encrypted visitors. Malicious code and dangerous dependencies can slip via when inspection and visibility are restricted.
The webinar focuses on how cloud-native inspection, conduct evaluation, and zero-trust design are getting used to floor these hidden assault paths earlier than they attain customers or manufacturing methods.
This isn’t a breach postmortem or a vulnerability alert. It is a sensible have a look at how fashionable assaults function — and why counting on file-based alerts alone is not sufficient.
For SOC groups, IT leaders, and safety architects making an attempt to shut actual gaps with out slowing the enterprise, this session is designed to be quick, concrete, and immediately relevant.
Be part of us to learn to acquire visibility into the exercise that issues most.
Register for the Webinar ➜
Discovered this text fascinating? This text is a contributed piece from one in every of our valued companions. Observe us on Google Information, Twitter and LinkedIn to learn extra unique content material we put up.