Jan 13, 2026Ravie LakshmananMalware / Endpoint Safety
Cybersecurity researchers have disclosed particulars of a brand new marketing campaign dubbed SHADOW#REACTOR that employs an evasive multi-stage assault chain to ship a commercially obtainable distant administration software known as Remcos RAT and set up persistent, covert distant entry.
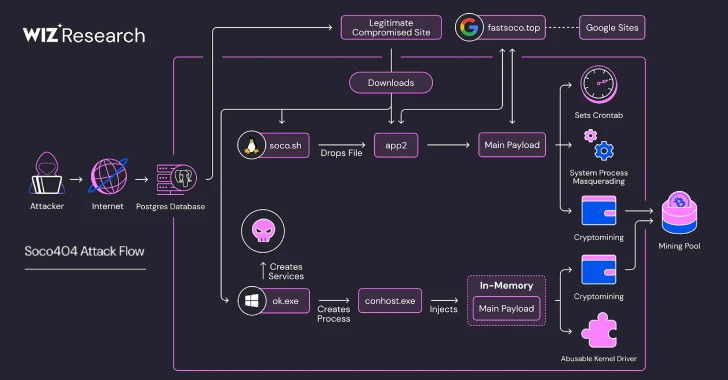
“The an infection chain follows a tightly orchestrated execution path: an obfuscated VBS launcher executed through wscript.exe invokes a PowerShell downloader, which retrieves fragmented, text-based payloads from a distant host,” Securonix researchers Akshay Gaikwad, Shikha Sangwan, and Aaron Beardslee stated in a technical report shared with The Hacker Information.
“These fragments are reconstructed into encoded loaders, decoded in reminiscence by a .NET Reactor–protected meeting, and used to fetch and apply a distant Remcos configuration. The ultimate stage leverages MSBuild.exe as a living-off-the-land binary (LOLBin) to finish execution, after which the Remcos RAT backdoor is totally deployed and takes management of the compromised system.”
The exercise is assessed to be broad and opportunistic, primarily concentrating on enterprise and small-to-medium enterprise environments. The tooling and tradecraft align with typical preliminary entry brokers, who receive footholds to focus on environments and promote them off to different actors for monetary acquire. That stated, there is no such thing as a proof to attribute it to a identified menace group.
Probably the most uncommon side of the marketing campaign is the reliance on intermediate text-only stagers, coupled with the usage of PowerShell for in-memory reconstruction and a .NET Reactor–protected reflective loader, to unpack subsequent phases of the assault with an intention to complicate detection and evaluation efforts.
The an infection sequence begins with the retrieval and execution of an obfuscated Visible Fundamental Script (“win64.vbs”) that is doubtless triggered by way of consumer interplay, akin to clicking on a hyperlink delivered through socially engineered lures. The script, run utilizing “wscript.exe,” features as a light-weight launcher for a Base64-encoded PowerShell payload.
The PowerShell script subsequently employs System.Web.WebClient to speak with the identical server used to fetch the VBS file and drop a text-based payload named “qpwoe64.txt” (or “qpwoe32.txt” for 32-bit programs) within the machine’s %TEMP% listing.
“The script then enters a loop the place it validates the file’s existence and measurement,” Securonix defined. “If the file is lacking or beneath the configured size threshold (minLength), the stager pauses execution and re-downloads the content material. If the edge shouldn’t be met inside the outlined timeout window (maxWait), execution proceeds with out terminating, stopping chain failure.”
“This mechanism ensures that incomplete or corrupted payload fragments don’t instantly disrupt execution, reinforcing the marketing campaign’s self-healing design.”
Ought to the textual content file meet the related standards, it proceeds to assemble a second secondary PowerShell script (“jdywa.ps1”) within the %TEMP% listing, which invokes a .NET Reactor Loader that is liable for establishing persistence, retrieving the next-stage malware, and incorporating numerous anti-debugging and anti-VM checks to fly below the radar.
The loader finally launches the Remcos RAT malware on the compromised host utilizing a authentic Microsoft Home windows course of, “MSBuild.exe.” Additionally dropped over the course of the assault are execution wrapper scripts to re-trigger the execution of “win64.vbs” utilizing “wscript.exe.”
“Taken collectively, these behaviors point out an actively maintained and modular loader framework designed to maintain the Remcos payload moveable, resilient, and troublesome to statically classify,” the researchers famous. “The mix of text-only intermediates, in-memory .NET Reactor loaders, and LOLBin abuse displays a deliberate technique to frustrate antivirus signatures, sandboxes, and fast analyst triage.”