The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a directive for Federal Civilian Executive Branch (FCEB) agencies to enhance the management of edge network devices. This initiative requires the removal of devices no longer receiving security updates from their original manufacturers within the next 12 to 18 months. The directive aims to reduce technical vulnerabilities and mitigate risks associated with these devices, which are increasingly targeted by state-sponsored cyber threats.
Understanding the Role of Edge Devices
Edge devices, which include components such as load balancers, firewalls, routers, and Internet of Things (IoT) devices, play a critical role in network traffic management and security. Positioned at the perimeter of networks, they hold significant access privileges and are susceptible to exploitation if not adequately supported with updates and patches. CISA emphasizes the vulnerabilities these devices present when they are no longer maintained by vendors.
CISA’s Strategic Actions for Cybersecurity
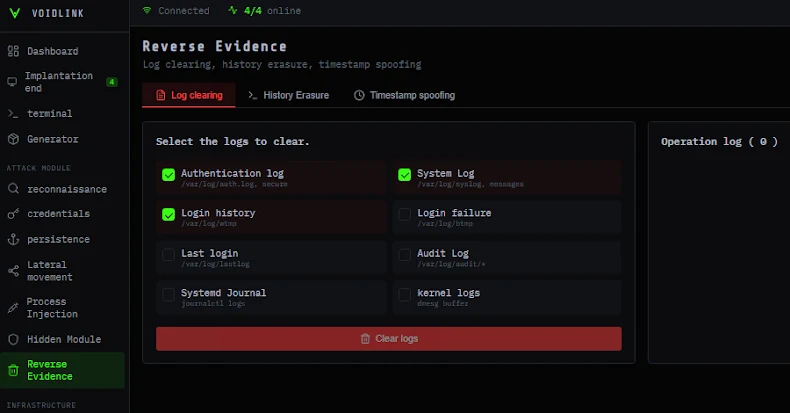
To assist agencies in complying with this directive, CISA has compiled an end-of-support edge device list. This repository provides crucial information about devices that have reached or are nearing the end of their support life, detailing product names, version numbers, and end-of-support dates. The newly implemented Binding Operational Directive 26-02 lays out clear steps for agencies to follow in addressing these risks.
These actions include updating all vendor-supported edge devices to the latest software versions immediately, cataloging and reporting end-of-support devices to CISA within three months, and decommissioning unsupported devices within 12 months. The directive also calls for the establishment of a lifecycle management process to continuously monitor and manage edge devices expected to reach end-of-support status.
Implications and Future Outlook
CISA Acting Director Madhu Gottumukkala underscores the significant threat posed by unsupported devices to federal systems. By proactively managing the lifecycle of these assets and removing outdated technology, federal agencies can enhance their network resilience and contribute to safeguarding the global digital infrastructure. This directive is a step towards fortifying cybersecurity measures across federal networks.
As agencies work to comply with these new requirements, the directive emphasizes the importance of ongoing vigilance and strategic management of network assets. Looking forward, the focus will remain on maintaining robust security protocols to protect against evolving cyber threats.