In February 2026, cybersecurity experts discovered a new wave of threats as hackers deployed advanced AI tools in their campaigns. These Large Language Models (LLMs) have been integrated into attack strategies, showcasing a significant shift in how cybercrime operations are conducted globally.
Integration of AI in Cyber Attacks
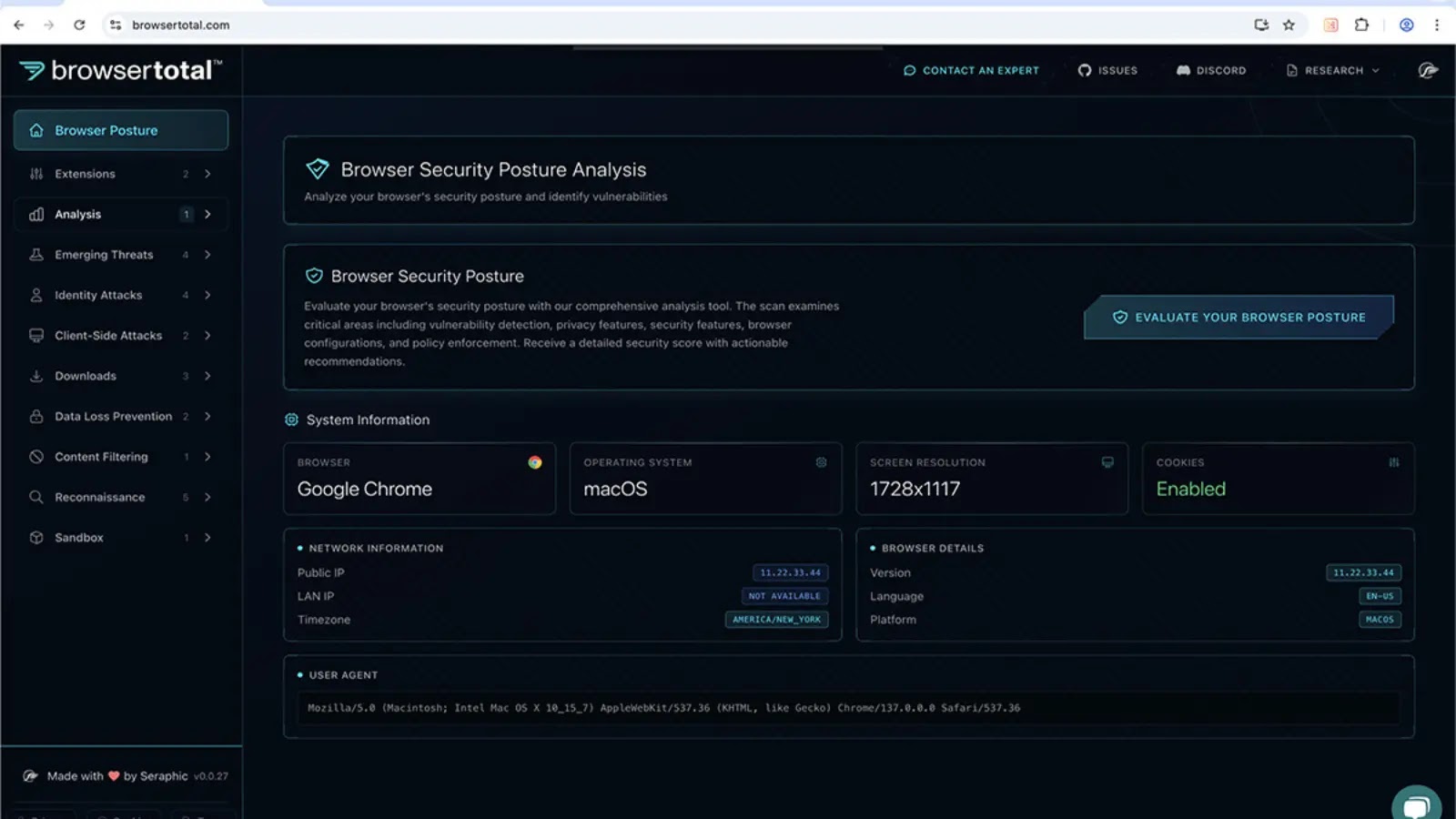
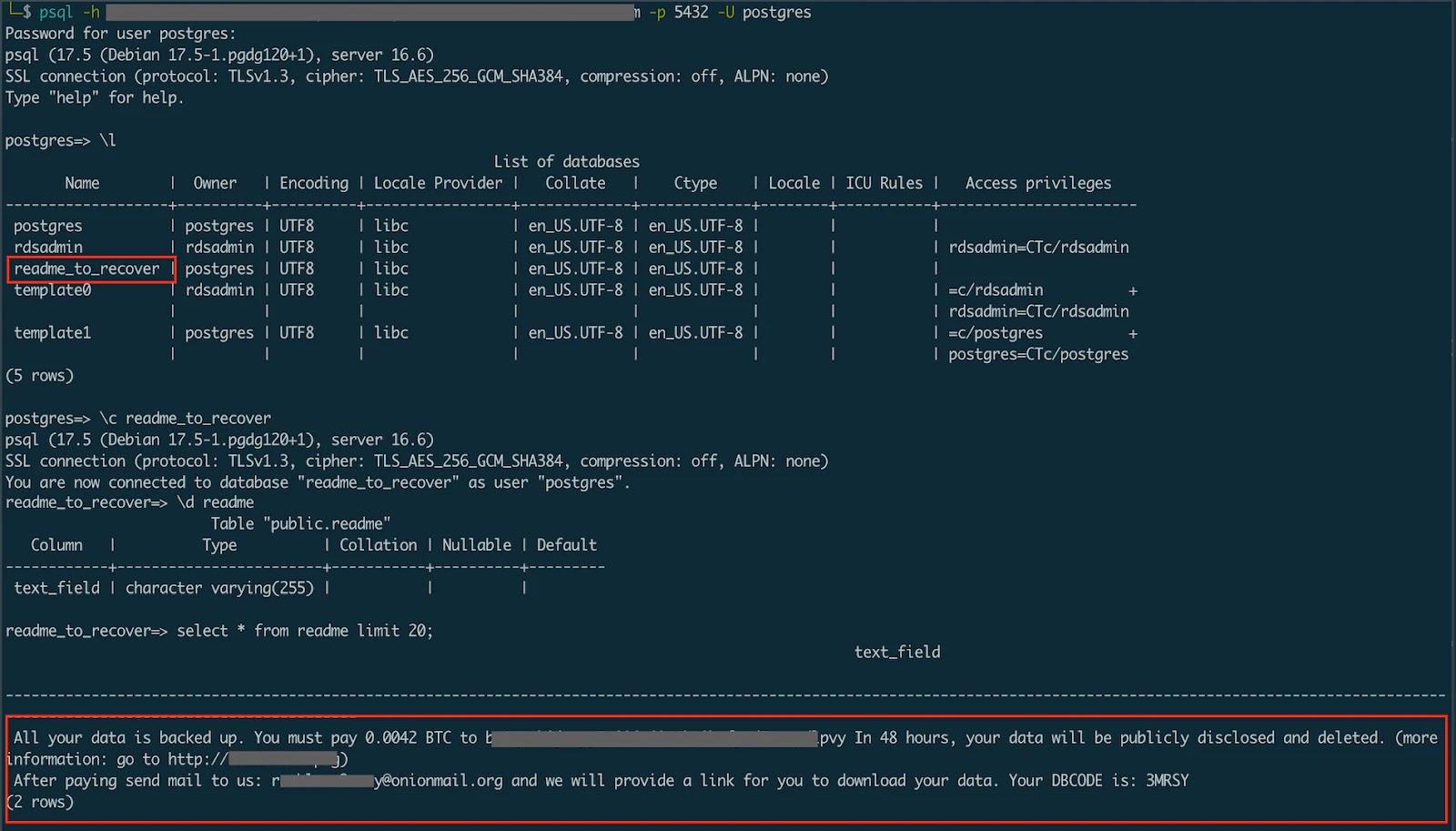
Security analysts found that misconfigured servers revealed a complex software pipeline used by attackers. This pipeline incorporated AI models, DeepSeek and Claude, into the attackers’ processes. The incorporation of these technologies signifies a dangerous trend where artificial intelligence is not only used for generating text but is also embedded into cyber-attack frameworks, automating complex tasks against worldwide targets.
The primary focus of these attacks has been on FortiGate SSL VPN appliances. By exploiting stolen configuration data, attackers could breach networks, effectively mapping internal systems and identifying key assets. The operation relied on custom-built tools to automate these intrusions, allowing them to target thousands of devices concurrently without manual input at every stage.
Global Impact and Automation
Investigations reveal that over 2,500 devices in 106 countries were attacked in parallel. Analysts from Cyber and Ramen noted the use of a dual-model strategy: DeepSeek for developing strategic attack plans and Claude for executing vulnerability assessments. This level of automation enabled even less skilled operators to manage a high volume of intrusions efficiently.
The operation’s core utilized two main components: ARXON and CHECKER2. CHECKER2, a Docker-based orchestrator, managed parallel VPN scanning, while ARXON served as a Model Context Protocol (MCP) server, bridging network data with the AI models to produce actionable steps for exploitation. The intrusion chain demonstrates how the system progresses from initial infiltration to active exploitation.
Recommendations for Mitigation
Upon network entry, the system autonomously deployed offensive tools like Impacket and Metasploit using Claude. The vulnerability assessment reports found on the server highlighted the AI’s ability to document findings and suggest prioritized actions, such as privilege escalation. Logs confirm the system’s active targeting of various sectors, including telecommunications.
To counter these AI-driven threats, immediate action is crucial. Organizations should prioritize updating their edge devices to mitigate vulnerabilities quickly. Regular audits of VPN user accounts for unauthorized activity and monitoring for unexpected SSH sessions are recommended. Verifying network configurations against known baselines can also help in detecting subtle changes typical of this campaign.
Stay updated by following us on Google News, LinkedIn, and X, and set CSN as your preferred news source on Google for more instant updates.