Emerging Threat of Steganography in Cyber Attacks
In a recent discovery, cybersecurity experts have uncovered a new technique where hackers use steganographic methods within images to deploy malware. The malicious NPM package, named buildrunner-dev, conceals .NET malware in PNG images, allowing it to bypass antivirus scans and install a Remote Access Trojan (RAT) on Windows systems.
This campaign, identified in February 2026, highlights a significant evolution in supply chain attacks. The malicious code remains hidden within what appears to be benign image files, representing a growing challenge for security measures.
Malware Delivery Through Image Concealment
The buildrunner-dev package exploits a tactic known as typosquatting, mimicking legitimate NPM packages like buildrunner and build-runner, which have been abandoned by their creators. Unsuspecting developers could easily download this harmful version, mistaking it for an updated package.
Upon installation via npm install, a postinstall script initiates a file named init.js, which downloads a batch file from a Codeberg repository. This file embeds itself in the Windows Startup folder to ensure it runs with every system boot.
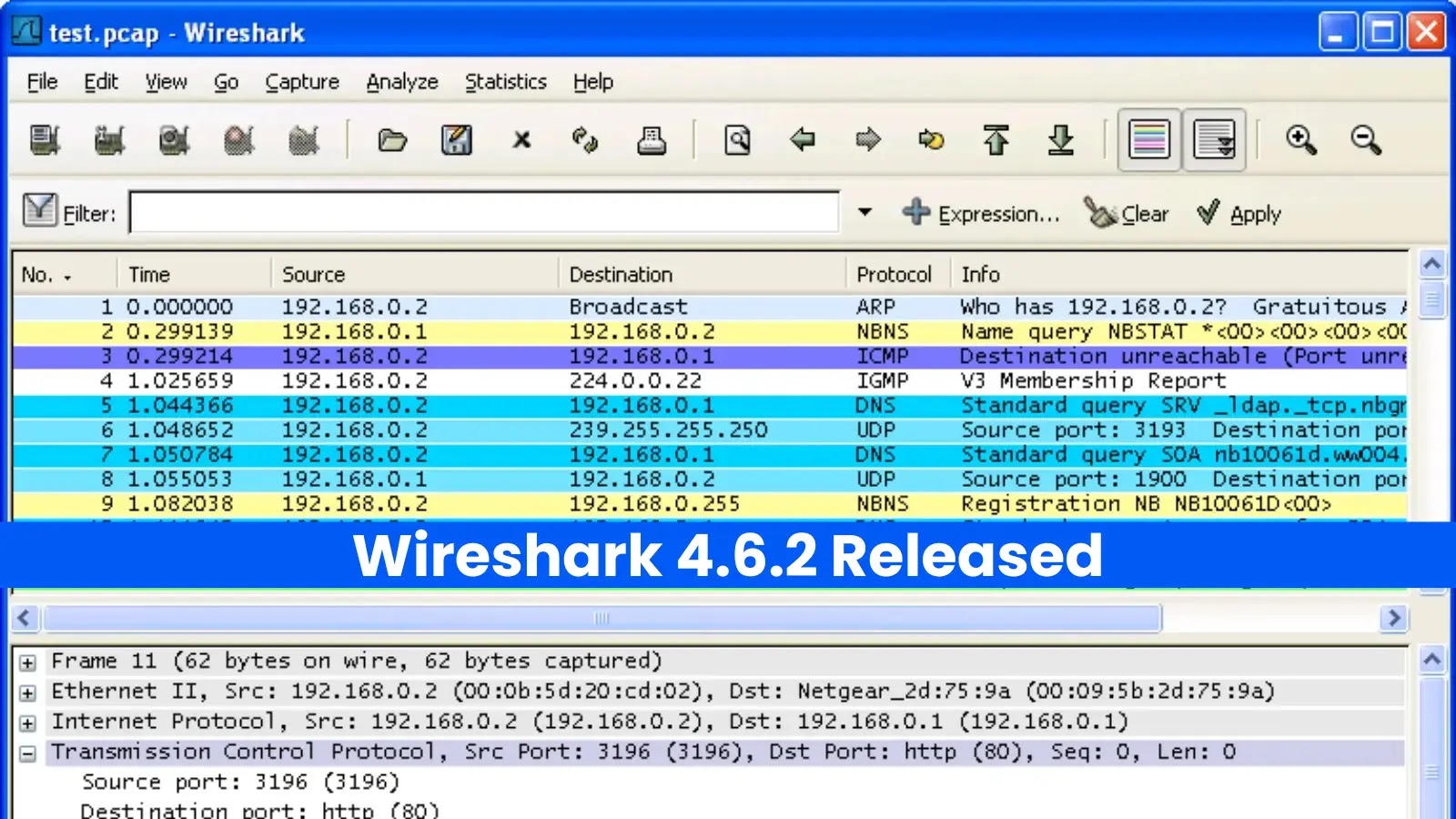
Analyzing the Attack Mechanism
Veracode researchers, after dissecting the batch file through multiple layers of obfuscation, revealed that the file predominantly consisted of deceptive elements designed to mislead both static analysis tools and human reviewers.
Before executing its payload, the malware checks for administrative rights, employing the fodhelper.exe UAC bypass to elevate privileges without raising alerts. It then launches a hidden PowerShell session, evaluates installed antivirus software, and adapts its infection strategy accordingly.
Steganographic Techniques in Action
Two PNG images hosted on ImgBB were found to carry the malicious payloads. One image, appearing as random visual noise, concealed an AMSI bypass PowerShell script, while another encoded a .NET loader. A third image served as a communication channel, delivering the Pulsar RAT payload when required.
By embedding malware into the RGB pixel values of these images, attackers effectively circumvented standard security scans, posing a substantial risk to unprotected systems.
Preventive Measures and Recommendations
Security professionals are advised to thoroughly audit NPM packages before installation, disable automatic execution of postinstall scripts, and monitor for unusual PowerShell activity. Observing UAC bypass attempts and unexpected connections to image hosting sites can help detect similar threats early.
As cyber threats continue to evolve, staying informed and vigilant is crucial for protecting systems against such sophisticated attacks.