Triage is designed to streamline operations, yet often it complicates them, particularly in Security Operations Centers (SOCs). When early assessments fall short, alerts can spiral into repeated checks and unnecessary escalations. This inefficiency not only disrupts the SOC but also leads to missed Service Level Agreements (SLAs), increased costs, and potential oversight of genuine threats.
Identifying the Root Causes of Triage Failures
A primary issue in triage inefficiency is decision-making based on partial or inadequate evidence. This can result in premature case approvals or escalations, fueling false positives and allowing actual threats to linger unnoticed. The uncertainty inherent in this process raises costs and delays containment efforts.
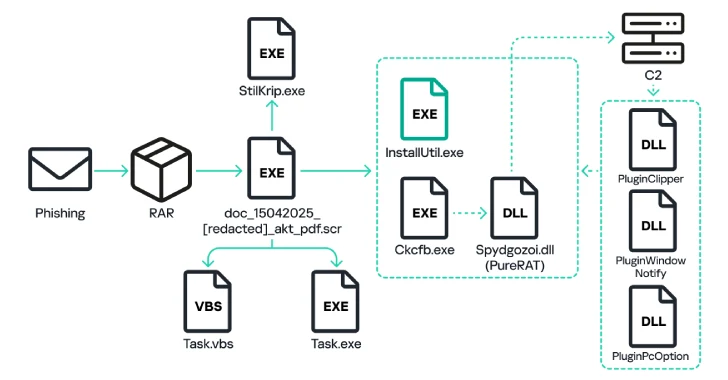
To mitigate these risks, top-performing teams emphasize validating behaviors early in the triage process. Utilizing sandboxes, such as ANY.RUN’s interactive tool, allows teams to visualize the entire attack chain within seconds. This method transforms ambiguous alerts into decisive actions, enhancing the speed and confidence of threat assessments.
The Impact of Analyst Experience on Triage Quality
Another challenge is the dependence on analyst seniority for triage quality. In many SOCs, the outcome hinges on whether a senior analyst can recognize threat patterns, while less experienced staff may default to escalation due to a lack of confidence. This leads to inconsistent responses and a workflow that struggles to scale.
High-functioning teams address this by instituting repeatable triage processes based on shared evidence. Tools like ANY.RUN facilitate consistent outcomes across shifts by enabling real-time information sharing and reducing unnecessary escalations.
Accelerating Triage to Counteract Threats
Delays in triage can grant attackers additional time to exploit vulnerabilities. Manual checks and queued escalations prolong action, increasing the likelihood of data breaches. Businesses face higher incident costs and SLA violations as a result.
To shrink time-to-decision, efficient teams focus on rapid behavior confirmation. By leveraging tools that provide immediate visibility into suspicious activities, teams can significantly reduce Mean Time to Respond (MTTR) and improve operational efficiency.
In summary, improving triage processes is crucial for reducing business risks. By shifting to evidence-driven methodologies and utilizing interactive automation, security teams can enhance their responsiveness, lower costs, and better protect their organizations from evolving threats.