The cybersecurity landscape is rapidly evolving, with new threats emerging from seemingly innocuous sources. Whether it’s a simple ad or a routine software update, these threats are becoming more sophisticated, gaining faster access and establishing control more swiftly. As a result, mitigation becomes increasingly challenging.
AI Integration in Kali Linux
Kali Linux, a renowned tool for penetration testing and network security, has integrated Anthropic’s Claude, a large language model, via the Model Context Protocol (MCP). This integration allows users to issue commands in natural language, translating them into technical directives, thereby enhancing its usability for ethical hacking purposes.
Malicious Spyware Operations
A Belarusian spyware, ResidentBat, has been identified as a tool used for surveillance against journalists and activists. First documented in December 2025, its origins trace back to 2021. The spyware grants access to sensitive data like call logs and encrypted communications. Its infrastructure is largely based in Europe and Russia, utilizing a limited port range for control.
Phishing Tactics in Cryptocurrency
The rise of phishing campaigns mimicking cryptocurrency services such as Bitpanda poses a significant threat. These campaigns trick users into divulging sensitive information under the guise of account verification or multi-factor authentication. Such tactics, noted by security experts, exploit user trust and the realistic appearance of phishing content.
Accelerated Cyber Intrusions
Reports from CrowdStrike and ReliaQuest highlight a concerning trend: the time between initial access and lateral movement within networks has drastically reduced. In 2025, this time shrank to 29 minutes, a significant increase in speed. Attackers leverage AI and legitimate credentials to blend into network traffic, bypassing traditional security measures and rapidly escalating privileges.
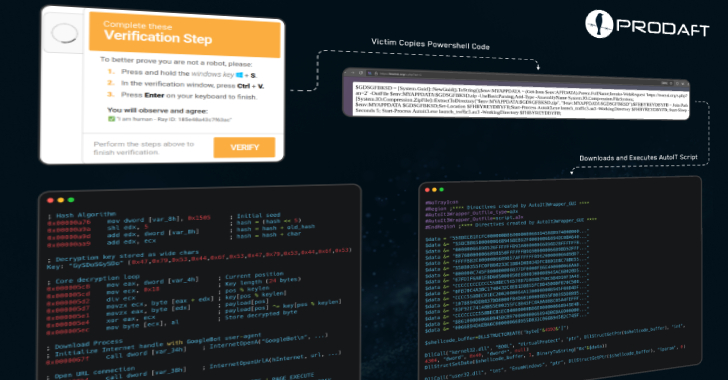
Malvertising and Mac Security Threats
A malvertising campaign targets Mac users searching for popular software. By hijacking Google advertiser accounts, attackers direct users to fraudulent sites that deliver malware. These campaigns use social engineering techniques and hijacked ads to distribute malware, highlighting the persistent threat of deceptive online advertisements.
Encryption and Security Concerns
Meta’s decision to encrypt messaging on its platforms, despite internal concerns, underscores the ongoing debate around encryption and user safety. While aiming to protect user privacy, encryption can hinder law enforcement’s ability to monitor illegal activities, raising questions about the balance between privacy and security.
Ransomware and Exploited Vulnerabilities
Recent exploits of vulnerabilities, such as in Apache ActiveMQ servers, demonstrate the persistent threat of ransomware. Attackers continue to leverage security flaws to deploy ransomware like LockBit, emphasizing the need for timely patching and robust security measures to prevent repeated breaches.
Persistent Threats in Browser Extensions
Google Chrome extensions have been identified as vectors for crashing browsers and executing malicious commands. These extensions, while offering legitimate functionalities, exploit their users by mimicking legitimate processes, highlighting the importance of vigilance in software extension usage.
The rapid evolution of cyber threats demands continuous awareness and adaptation. With deception tactics improving and attackers blending into everyday activities, staying informed and vigilant is critical. The cybersecurity landscape is changing weekly, but the pressure to maintain security remains constant.