The Iranian advanced persistent threat (APT) group, known as MuddyWater, has successfully breached several US-based organizations, according to recent reports from Broadcom’s Symantec and the Carbon Black threat hunting team. The cyber-attacks have affected a range of sectors, including an aerospace and defense contractor, a US airport, and a bank.
Targeted Entities in the US and Beyond
MuddyWater’s infiltration extends beyond US borders, impacting entities like a software firm operating in Israel and a non-governmental organization (NGO) active in both the US and Canada. These attacks have intensified following recent military actions by the US and Israel against Iran, which have heightened regional tensions.
The compromised software company, which serves the aerospace and defense sectors, has been a significant target due to its operations in Israel. This makes it particularly vulnerable to MuddyWater’s espionage activities.
Deployment of Sophisticated Backdoors
As part of their campaign, MuddyWater introduced a new backdoor termed ‘Dindoor’ into the networks of the targeted software company’s Israeli branch, as well as into the US bank and Canadian NGO. This backdoor carried a certificate attributed to ‘Amy Cherne’. Furthermore, the group attempted to extract sensitive data from these networks.
Additionally, the cybersecurity team identified another backdoor, ‘Fakeset’, developed using Python, which was found in the systems of a US airport and an NGO. This malware, too, was linked to certificates previously used in MuddyWater’s operations.
Ongoing Threat and Security Insights
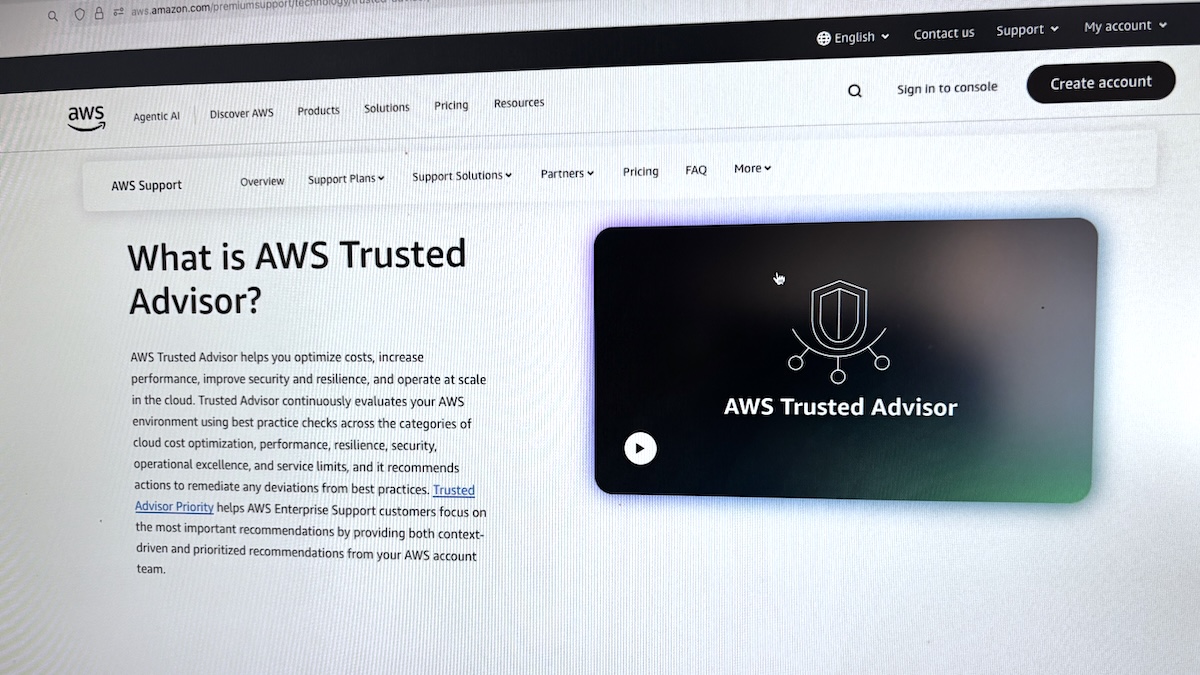
Although the malicious activities have been temporarily disrupted, the potential risk remains high. Symantec and Carbon Black warn that other organizations could still be susceptible to similar breaches. MuddyWater, also known by aliases such as Mango Sandstorm and Seedworm, is associated with Iran’s Ministry of Intelligence and Security.
Active since 2017, the group is notorious for targeting Middle Eastern entities and has recently escalated its cyber warfare capabilities. Notably, last year, Amazon documented the APT’s involvement in hacking live CCTV streams in Jerusalem to support missile attacks.
The cybersecurity landscape continues to evolve, with state-sponsored actors like MuddyWater posing significant challenges. Organizations must remain vigilant and strengthen their defenses against sophisticated cyber threats.