Salesforce has recently alerted users to a surge in malicious activities targeting Experience Cloud sites through a modified version of the AuraInspector tool. These threats exploit misconfigured guest user settings, potentially exposing sensitive data.
Understanding the Threat
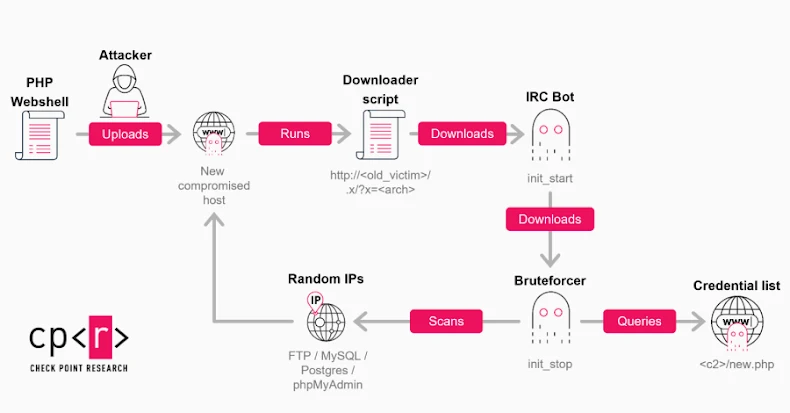
According to Salesforce, the increase in attacks involves leveraging overly permissive configurations of guest user profiles on publicly accessible Experience Cloud sites. By using a customized version of the open-source tool AuraInspector, attackers can extract data beyond merely identifying weak spots. Originally, AuraInspector was created to help security teams audit access control configurations within the Salesforce Aura framework, a tool released by Mandiant in January 2026.
Typically, guest user profiles are used for accessing general content such as landing pages and FAQs. However, misconfigurations can grant these profiles access to unintended data, allowing attackers to query Salesforce CRM objects without logging in. This vulnerability arises when Experience Cloud customers use guest user profiles without adhering to Salesforce’s configuration guidelines.
Potential Impacts and Recommendations
Salesforce has not found any inherent vulnerabilities in its platform related to these attacks, which focus on customer-side configuration issues. The company suspects a known threat group, possibly ShinyHunters, could be behind these attacks. ShinyHunters has been linked to previous incidents involving Salesforce environments via third-party applications like Salesloft and Gainsight.
To mitigate these risks, Salesforce advises customers to review and tighten their Experience Cloud guest user settings. Recommendations include setting the Default External Access for all objects to Private, disabling public API access for guest users, and restricting visibility settings. Additionally, turning off self-registration if unnecessary and monitoring logs for unusual queries are also advised steps.
Broader Implications and Future Outlook
This wave of attacks highlights a growing trend of identity-based targeting in the cybersecurity landscape. The data obtained through these breaches, such as personal contact details, is often used in subsequent social engineering and vishing tactics. Organizations must remain vigilant and proactive in securing their configurations to prevent such exploits.
As cyber threats evolve, the importance of adhering to recommended security practices cannot be overstated. Salesforce continues to emphasize the need for regular security audits and adherence to best practices to safeguard against potential attacks. Keeping systems updated and configurations secure will be crucial in mitigating the risks posed by these sophisticated threat actors.