Artificial intelligence (AI) browsers are being targeted by cybercriminals, who have managed to exploit their vulnerabilities to execute phishing scams within a matter of minutes. Recent findings by security firm Guardio highlight the susceptibility of these browsers, including Perplexity’s Comet AI, to such attacks.
The Mechanics of AI Browser Exploitation
AI-powered browsers, which autonomously navigate and perform tasks across various websites, are at risk of being manipulated by malicious actors. Guardio’s research reveals how the reasoning capabilities of these browsers can be turned against them, reducing their security measures and paving the way for phishing scams. By intercepting communications between the browser and AI services, attackers can use a Generative Adversarial Network (GAN) to deceive the browser into executing phishing activities.
Security researcher Shaked Chen describes this vulnerability as ‘Agentic Blabbering,’ where the browser exposes its internal decision-making processes. This transparency allows attackers to train their scams effectively, refining them until the AI browser complies with their malicious intents.
Innovative Phishing Techniques
The exploitation of AI browsers is not new, building on previous methods like VibeScamming and Scamlexity. These techniques involve tricking AI browsers into generating deceptive pages or performing harmful actions through hidden prompt injections. Unlike traditional scams targeting human users, these attacks focus on deceiving the AI itself, creating a shift in the threat landscape.
The ultimate goal is to create a ‘scamming machine’ that perfects phishing pages to bypass browser defenses. Once tailored to one browser, the scam becomes effective against all users of that specific AI model, marking a significant evolution in phishing strategies.
Addressing the Security Challenges
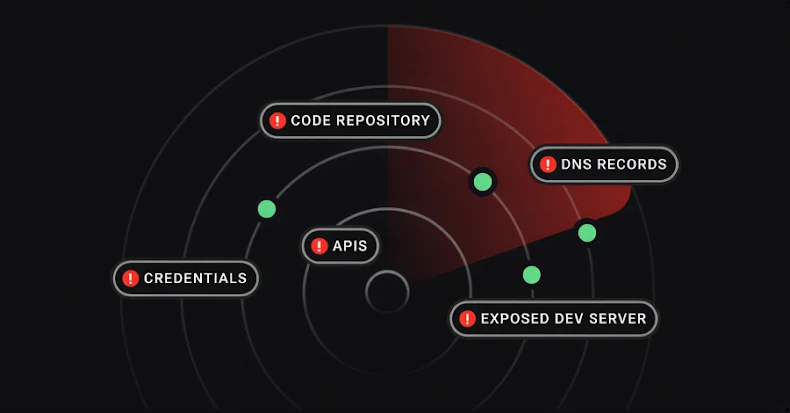
Recent demonstrations by Trail of Bits and Zenity Labs further underscore the vulnerabilities of AI browsers like Comet. These include prompt injection techniques capable of extracting private data from services such as Gmail and exploiting browser assistants to exfiltrate sensitive information.
Although some vulnerabilities, codenamed PerplexedBrowser, have been addressed, the issue remains a pressing concern. Prompt injection attacks, which blend user requests with attacker commands, pose a persistent security challenge for large language models and their integration into enterprise systems.
Despite efforts to mitigate these risks through automated discovery and adversarial training, eliminating such vulnerabilities entirely may not be feasible, as stated by OpenAI in late 2025. As AI browsers become more prevalent, the need for robust safeguards and continuous monitoring becomes increasingly critical.
In conclusion, as AI browsers continue to evolve, so do the tactics of cybercriminals seeking to exploit their weaknesses. The ongoing battle between security measures and malicious actors highlights the importance of vigilance and innovation in cybersecurity.