In a recent cybersecurity development, experts have identified a new banking malware, crafted in Rust, that specifically targets Brazilian users. This malware, dubbed VENON by the cybersecurity firm ZenoX, marks a significant departure from the traditional Delphi-based threats commonly associated with the Latin American cybercrime landscape.
New Malware Targets Windows Systems
VENON, first detected last month, is engineered to infiltrate Windows operating systems. Its emergence represents a shift in strategy compared to previous malware families like Grandoreiro and Mekotio, as it incorporates features such as banking overlay logic, active window monitoring, and shortcut (LNK) hijacking mechanisms. Despite its sophisticated design, the malware has not been linked to any known cybercrime groups or campaigns.
Technical Insights and Distribution Tactics
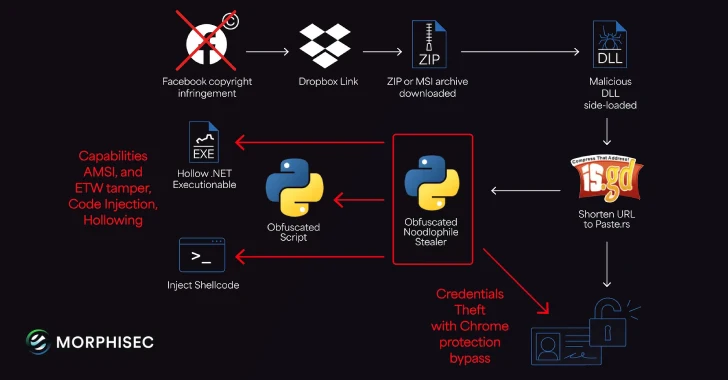
The malware’s development showcases a familiarity with Latin American banking trojans, as suggested by its Rust code structure. Notably, VENON employs DLL side-loading to execute a malicious DLL, with distribution likely facilitated through social engineering tactics like ClickFix. Users are tricked into downloading a ZIP archive via a PowerShell script, which initiates the infection chain.
Once the DLL is activated, it employs numerous evasion techniques, including anti-sandbox checks and AMSI bypasses, before proceeding to its malicious tasks. It communicates with a Google Cloud Storage URL to obtain configuration details and establishes a WebSocket connection to a command-and-control server.
Impact and Broader Threat Landscape
VENON’s attack strategy is comprehensive, targeting 33 financial institutions and digital asset platforms. It uses browser and window monitoring to deploy fake overlays for credential theft, particularly targeting the Itaú banking application by hijacking system shortcuts.
The malware’s disclosure coincides with ongoing campaigns exploiting WhatsApp’s popularity in Brazil, where a worm named SORVEPOTEL is used to spread banking malware such as Maverick and Astaroth. This method involves leveraging WhatsApp’s desktop version to deliver malicious links through compromised chats, leading to the execution of malware directly in memory.
As the threat landscape evolves, VENON’s sophisticated approach underscores the growing complexity of cyber threats facing financial institutions. Continuous vigilance and advanced protective measures are crucial to counteract such innovative malware tactics.