Cybersecurity experts have unveiled detailed insights into a new artificial intelligence (AI)-generated malware known as Slopoly. This malware is reportedly leveraged by the financially driven cybercrime group, Hive0163, to enhance their ransomware operations.
AI-Driven Malware in Cybercrime
Slopoly, though not particularly advanced, signifies how easily AI can be harnessed to streamline malware creation. IBM X-Force researcher Golo Mühr highlighted this in a report shared with The Hacker News, noting the speed at which AI can help develop new malware frameworks. Hive0163’s activities primarily involve data theft and extortion through ransomware, utilizing an array of malicious tools such as NodeSnake and Interlock RAT.
In a notable attack from early 2026, Hive0163 used Slopoly during the post-exploitation phase to ensure ongoing access to a compromised server for over a week.
Technical Details of Slopoly
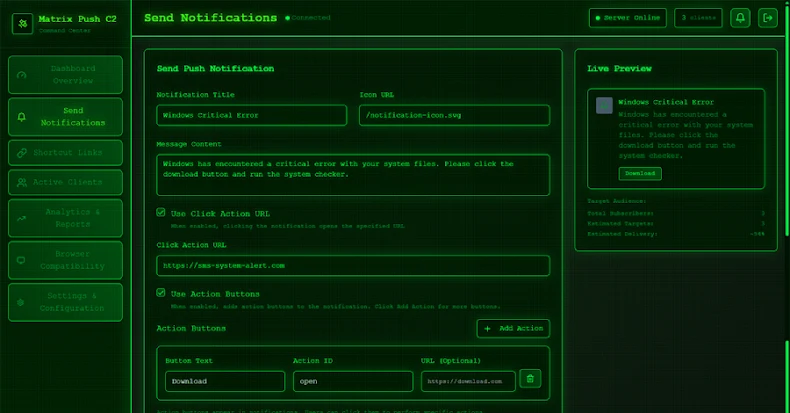
The discovery of Slopoly is linked to a PowerShell script, likely deployed via a builder that also sets up a scheduled task named “Runtime Broker” for persistence. Evidence suggests the malware’s development involved an unidentified large language model (LLM), characterized by comprehensive comments, structured logging, and well-named variables. These attributes suggest a command-and-control (C2) framework, although the script lacks true polymorphic capabilities.
Functioning as a backdoor, the PowerShell script regularly communicates with a C2 server, sending system information and awaiting new commands. The exact commands executed on compromised systems remain uncertain.
Hive0163’s Attack Strategies
Hive0163 often employs social engineering techniques like ClickFix to deceive victims into executing PowerShell commands, which subsequently download malware like NodeSnake. This initial component can execute shell commands, maintain persistence, and initiate broader malware frameworks, including Interlock RAT.
For initial access, Hive0163 relies on methods such as malvertising and collaboration with access brokers like TA569 and TAG-124. Their malware framework supports multiple programming languages, ensuring compatibility across Windows and Linux systems, and enabling actions like spawning reverse shells and deploying further payloads.
Implications of AI in Cybersecurity
The introduction of AI-assisted malware such as Slopoly, alongside others like VoidLink and PromptSpy, underscores the evolving threat landscape. While not technically groundbreaking, these developments allow threat actors to expedite attack preparation and execution, posing significant challenges for cybersecurity defenses.
IBM X-Force emphasizes that while AI-generated malware does not introduce technically complex threats, it significantly aids cybercriminals by shortening the time required to develop and execute attacks.