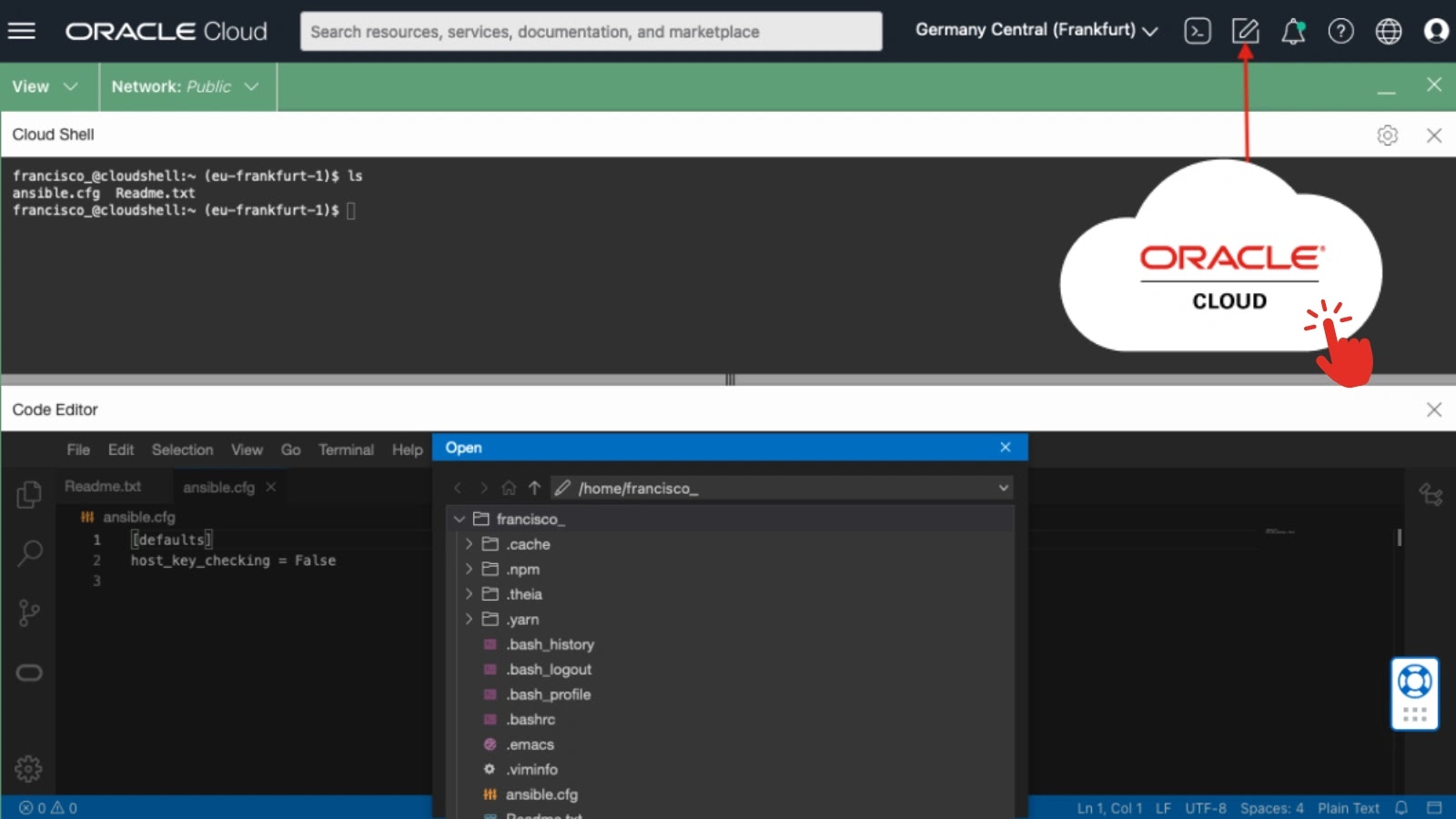
Security researchers from JFrog have identified a complex supply chain attack targeting the npm ecosystem. Discovered on March 12, 2026, this attack involved threat actors using malicious npm packages disguised as a legitimate Roblox script executor to distribute information-stealing malware.
Details of the Malicious Campaign
Named the Cipher stealer, this campaign involved two harmful packages: bluelite-bot-manager and test-logsmodule-v-zisko. These packages deployed a Windows executable designed to extract sensitive data such as Discord credentials, browser information, and files from cryptocurrency wallets.
The packages executed a pre-install script to silently download a Windows binary named solara 1.0.0.exe or solara 1.0.1.exe from a Dropbox-hosted URL. This process required no user interaction, making it particularly insidious.
Discord and Browser Targeting
Cipher’s primary focus was on Discord, where it stole session tokens from LevelDB databases in all installed Discord clients and Chromium-based browsers. This information was then verified against Discord’s API to ensure validity.
For users of BetterDiscord, the malware altered the core index.js file to bypass webhook protections, facilitating the transmission of stolen data to the attacker. Additionally, a secondary payload from GitHub was injected into Discord’s desktop client, capturing sensitive user information during the re-login process.
Impact on Browsers and Crypto Wallets
The malware operated on two fronts to steal browser credentials. Using Windows DPAPI libraries, it extracted encryption keys and passwords from several major browsers. Concurrently, a Python script covered additional browsers, obtaining cookies, credit card details, and more.
Furthermore, the malware searched for directories associated with various cryptocurrency wallets, copying and attempting to decrypt their contents. Stolen data was then archived and uploaded to a command-and-control server, with a report sent to the attacker’s Discord webhook.
Although the malicious npm packages have been removed and the Dropbox links deactivated, the GitHub repository hosting the injection script was still active at the time of discovery. Users are advised to uninstall the packages, reinstall Discord, update passwords, and secure their cryptocurrency wallets.