Experts in cybersecurity have revealed a significant vulnerability affecting GitHub.com and GitHub Enterprise Server, which permits an authenticated user to execute remote code through a singular ‘git push’ command. Identified as CVE-2026-3854, this command injection flaw has been assigned a CVSS score of 8.7. It allows attackers with push permissions to execute code remotely on the server.
Vulnerability Details and Discovery
The vulnerability was discovered by Wiz, a cloud security firm under Google’s ownership, and reported on March 4, 2026. GitHub responded swiftly, verifying and patching the issue on GitHub.com within a mere two hours. The flaw was rectified in several versions of GitHub Enterprise Server, specifically versions 3.14.25 and later.
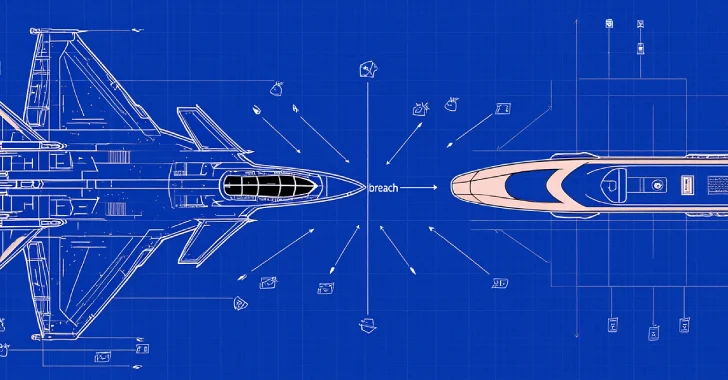
According to GitHub, the flaw affects multiple services including GitHub.com and various forms of GitHub Enterprise Cloud and Server. The core issue arises from inadequate sanitization of user-provided git push options, which were incorporated into internal X-Stat headers. This oversight allowed attackers to insert arbitrary commands via crafted push option values.
Exploitation and Impact
The exploit is notably straightforward, enabling remote code execution on shared storage nodes. Wiz reported that up to 88% of instances were vulnerable at the time of disclosure. The exploitation chain involves three key injections: bypassing sandboxes, redirecting hook directories, and executing arbitrary commands through crafted hooks.
GitHub’s multi-tenant architecture exacerbates the threat, as an attack on GitHub.com could lead to cross-tenant exposure, allowing unauthorized access to millions of repositories. This vulnerability emphasizes the need for immediate updates to protect against potential breaches.
Security Recommendations and Response
GitHub has advised users to apply the latest updates promptly to mitigate the risks associated with this vulnerability. The company highlights the importance of auditing multi-service architectures, particularly where user input influences critical security configurations.
Wiz emphasizes that the flaw underscores a critical attack surface when multiple services communicate through shared internal protocols. The need for rigorous security measures in handling user-controlled data is paramount to prevent such vulnerabilities in complex architectures.
In conclusion, the discovery of CVE-2026-3854 serves as a crucial reminder of the vulnerabilities inherent in software systems. It is a call to action for organizations to strengthen their security practices and remain vigilant against emerging threats.