Cybersecurity experts have identified a new wave of the GlassWorm campaign, which marks a significant intensification in its spread via the Open VSX registry. This development highlights the evolving tactics of the attackers, who now exploit extensionPack and extensionDependencies, transforming initially benign extensions into vehicles for malware delivery in subsequent updates. This strategy enables a seemingly harmless package to later download a GlassWorm-linked extension after trust has been established, according to Socket’s recent findings.
Expansion of Malicious Extensions
Since January 2026, at least 72 additional malicious Open VSX extensions have been discovered. These extensions disguise themselves as popular developer tools, including linters, formatters, and AI-powered coding assistants like Clade Code and Google Antigravity. Some identified extensions, such as angular-studio.ng-angular-extension and tamokill12.foundry-pdf-extension, have been removed by Open VSX.
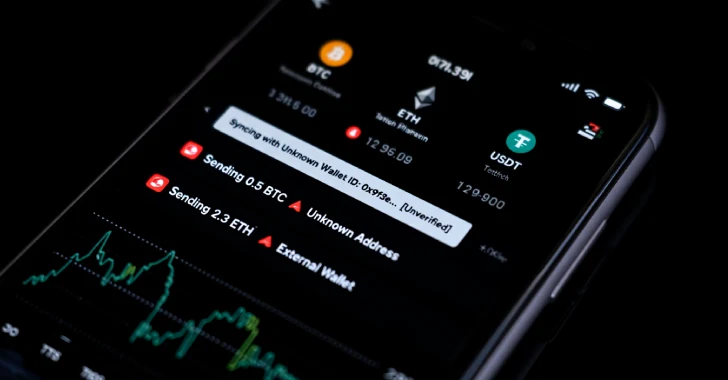
The GlassWorm campaign, known for infiltrating Microsoft Visual Studio Marketplace and Open VSX, aims to steal sensitive information and misuse infected systems for criminal activities. Initially reported by Koi Security in late 2025, similar tactics using invisible Unicode characters were found in npm packages as early as March 2025.
New Tactics and Techniques
Maintaining its core features, the latest GlassWorm iteration introduces heavier obfuscation and rotation of Solana wallets to evade detection. The campaign leverages extension relationships to deploy malicious payloads, akin to npm packages’ use of rogue dependencies. This approach allows attackers to bypass reviews by first uploading a harmless VS Code extension, then updating it to include a GlassWorm-linked package as a dependency.
Aikido’s advisory attributes the GlassWorm threat to a mass campaign affecting open-source repositories, utilizing invisible Unicode characters to encode payloads. This technique has impacted over 151 GitHub repositories between March 3 and March 9, 2026, and was also used in npm packages like @aifabrix/miso-client.
Implications and Future Outlook
In a related development, Endor Labs uncovered 88 new malicious npm packages uploaded from November 2025 to February 2026 using Remote Dynamic Dependencies (RDD). This method allows operators to modify malicious code on the fly, bypassing inspections. Although initially linked to the PhantomRaven campaign, these packages were later attributed to a security researcher’s experiment, raising questions about transparency and security risks.
These findings emphasize the importance of vigilance and improved security measures in software development environments. As attackers continue to refine their techniques, developers and security professionals must stay informed and adopt robust protective strategies to mitigate these evolving threats.