A new cyber threat has emerged as PylangGhost, a remote access trojan, makes its debut on the npm registry, hidden within two harmful JavaScript packages. This marks a notable rise in software supply chain attacks, with developers worldwide now at risk.
Background on PylangGhost and FAMOUS CHOLLIMA
First disclosed by Cisco Talos in June 2025, PylangGhost is attributed to the North Korean state-sponsored group FAMOUS CHOLLIMA. Known for targeting developers via trojanized repositories and social engineering, this group has now moved to npm, a popular open-source package registry, aiming to compromise development pipelines on a larger scale.
Researchers from Kmsec.uk identified two malicious packages, @jaime9008/math-service and react-refresh-update, published by the user jaime9008. These packages, appearing in late February and early March 2026, respectively, contained the PylangGhost loader within key JavaScript files.
Technical Details of the Attack
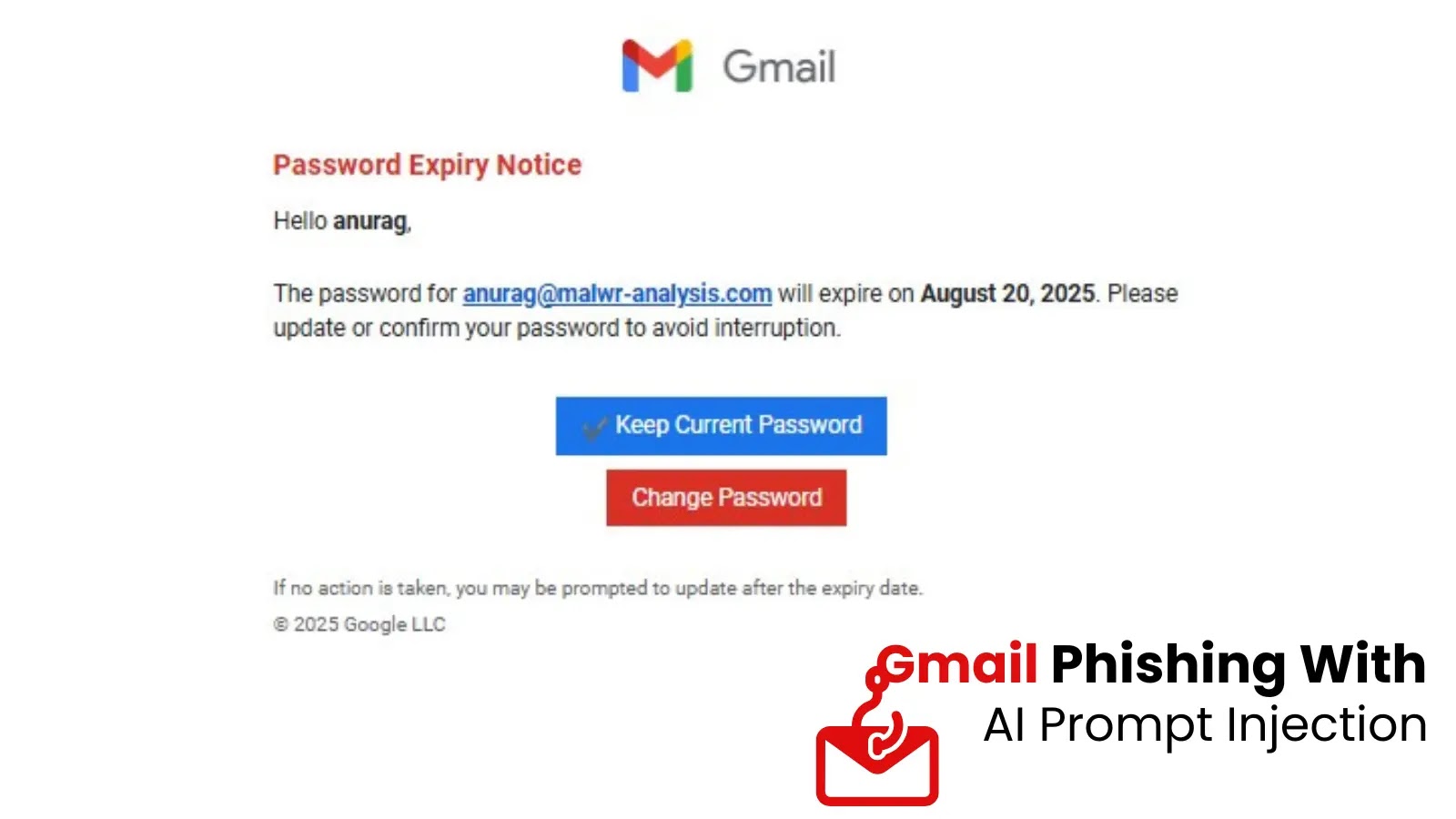
The malware’s campaign identifier, “ML2J,” and its command-and-control infrastructure, using the domain malicanbur[.]pro, highlight its sophistication. Any developer installing these packages might have unknowingly compromised their system, as the malware operates silently, evading detection.
This threat extends beyond individual developers; since npm packages are integral to large projects and CI/CD pipelines, a single infected dependency can jeopardize entire organizations. Using misleading package names like react-refresh-update exacerbates the risk, as such threats evade routine checks.
Infection Mechanics and Mitigation
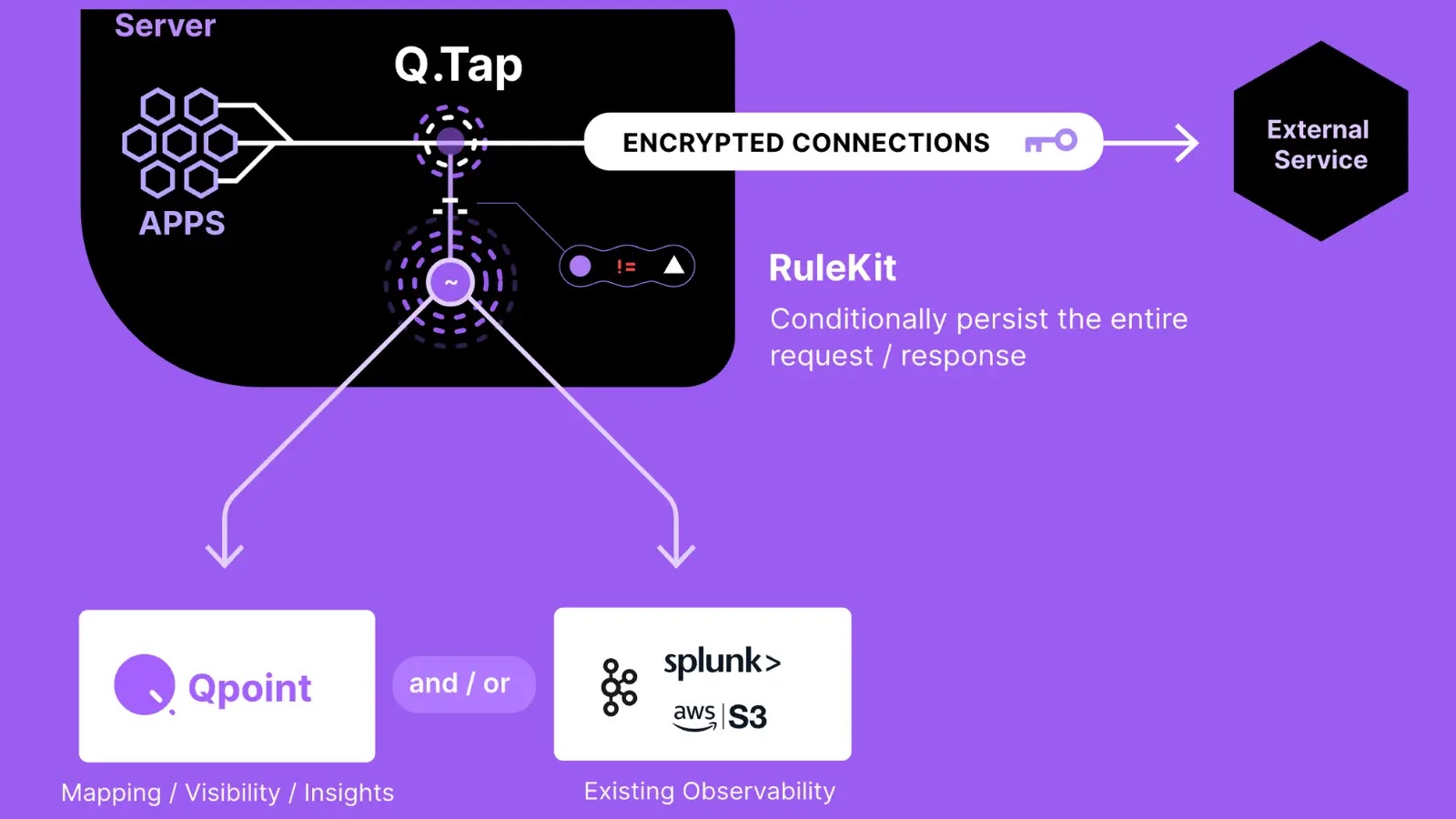
The infection mechanism is designed to operate quietly across various systems, including Windows, macOS, and Linux. Upon installation, a JavaScript loader executes a decode-decrypt-evaluate sequence using a specific XOR key to unlock the payload.
On Windows, the malware downloads a ZIP archive in fragments to avoid detection, while for macOS and Linux, it deploys an executable shell script. The RAT can extract Chrome extension IDs, granting attackers access to sensitive data.
Developers and security teams must audit their npm dependencies for the compromised packages and block traffic to malicanbur[.]pro. Employing software composition analysis tools can preemptively catch such threats, and any unusual network activity should be investigated promptly.
Staying updated on cybersecurity threats is crucial. Follow us on Google News, LinkedIn, and X for real-time updates and set CSN as your preferred source on Google.