A critical security vulnerability has been identified in ClawHub, the skill registry platform for the OpenClaw agentic ecosystem. This flaw has been exploited by attackers to artificially enhance the download counts of harmful skills, thus bypassing security measures and altering search rankings.
Manipulation of Skill Rankings
The vulnerability allowed threat actors to elevate compromised skills to the top of the rankings, enabling widespread supply-chain attacks targeting both human users and autonomous AI agents. ClawHub, akin to npm for OpenClaw agents, is used by developers to publish integrations for various tasks, including calendar management and web searches.
Users and AI models often rely on download statistics as a trust metric. Consequently, inflated download numbers can easily deceive targets into installing malicious code posing as popular skills.
Technical Details of the Exploit
The vulnerability originated from ClawHub’s backend implementation using the convex framework, which employs a typed Remote Procedure Call (RPC) model. In this system, backend functions are defined as either public or internal.
Silverfort researchers discovered that the downloads: increment function was incorrectly exposed as a public mutation, rather than an internal function. This misconfiguration allowed attackers to send unauthenticated requests to the exposed URL with any skill identifier. Without authentication, rate limiting, or deduplication, the endpoint could be triggered repeatedly, artificially inflating download metrics.
Impact and Response
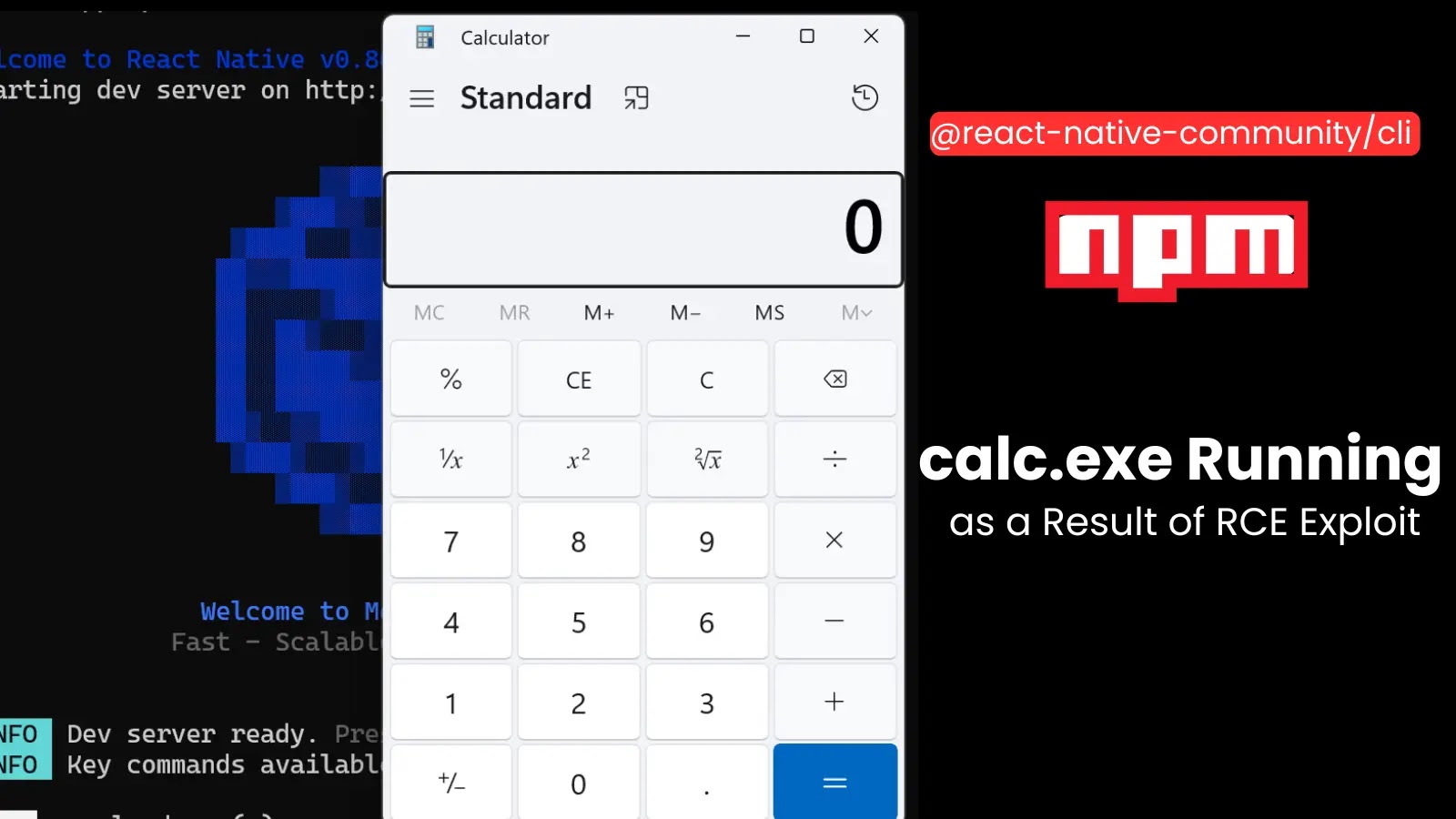
To demonstrate the risk, Silverfort executed a proof-of-concept supply chain attack, publishing a legitimate-looking skill with a hidden data-exfiltration payload. By exploiting the RPC endpoint, they increased the skill’s download count, falsely elevating its ranking in ClawHub search results.
Within days, the skill achieved nearly 4,000 executions across multiple locations, infiltrating various corporations. The attack highlighted how easily threat actors could gather sensitive data, such as usernames and domain names, from the execution context of an agent.
Silverfort disclosed the flaw to OpenClaw’s team on March 16, 2026. Lead developer Peter Steinberger and the security team quickly addressed the issue, implementing a fix within 24 hours. This incident underscores the hidden security challenges in fast-paced development environments and the risks of AI agents choosing installations based solely on social proof.
To prevent future vulnerabilities, Silverfort has introduced ClawNet, a new open-source security plugin for OpenClaw. ClawNet operates during runtime to intercept installation attempts, scanning skills for malicious patterns before execution is allowed.