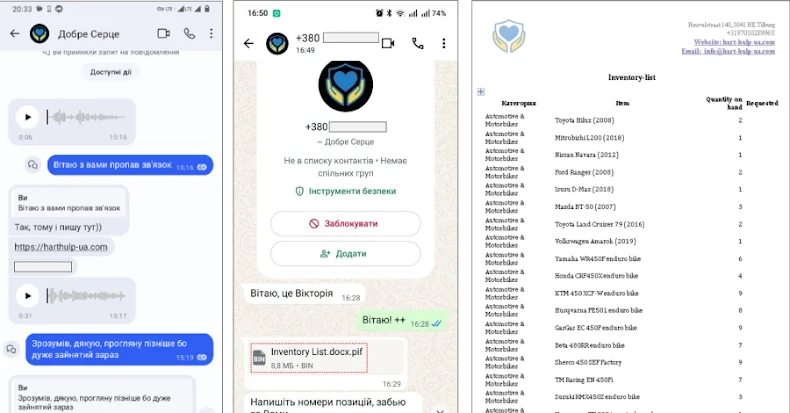
In a recent analysis, Microsoft has uncovered the use of HTTP cookies as a covert channel for controlling PHP web shells on Linux servers. This new threat vector is being exploited by cybercriminals to gain remote code execution capabilities, as reported by the Microsoft Defender Security Research Team.
Innovative Use of Cookies in Web Shells
Unlike traditional methods that expose command execution through URL parameters or request bodies, these PHP web shells leverage attacker-supplied cookie values. This technique not only facilitates execution and instruction passing but also activates malicious functionalities when specific cookies are detected, thus maintaining stealth.
This approach allows the malicious code to remain dormant, activating only upon receiving appropriate cookie values. As Microsoft points out, this behavior extends to various components of the server, including web requests and scheduled background tasks, making detection challenging.
Technical Breakdown of the Threat
The cookie-controlled execution model is implemented in several ways. One such method involves a PHP loader, which employs multiple layers of obfuscation and runtime checks to parse structured cookie inputs and execute a secondary payload. Another involves PHP scripts that utilize cookie data to reconstruct operational components, facilitating file handling and payload execution.
In certain instances, attackers gain initial access via valid credentials or by exploiting vulnerabilities to establish cron jobs. These cron jobs invoke shell routines to periodically execute obfuscated PHP loaders, creating a self-sustaining architecture that persists even after cleanup efforts.
Mitigation Strategies and Future Outlook
Microsoft suggests several measures to mitigate these threats, including enforcing multi-factor authentication for hosting control panels, monitoring login activity, restricting shell interpreter execution, auditing cron jobs, and checking for suspicious file activity in web directories.
The use of cookies as a control mechanism signifies a sophisticated reuse of existing web shell techniques, enabling persistent access while evading traditional security controls. By embedding control logic into cookies, threat actors exploit legitimate execution paths inherent in the server environment, thus maintaining a low profile.
As these tactics continue to evolve, it is critical for organizations to enhance their security measures and stay vigilant against such stealthy threats. Employing robust authentication methods and monitoring for anomalies will be key in countering these advanced cyber threats.