Jan 14, 2026Ravie LakshmananCyber Espionage / Risk Intelligence
The Laptop Emergency Response Crew of Ukraine (CERT-UA) has disclosed particulars of recent cyber assaults concentrating on its protection forces with malware referred to as PLUGGYAPE between October and December 2025.
The exercise has been attributed with medium confidence to a Russian hacking group tracked as Void Blizzard (aka Laundry Bear or UAC-0190). The risk actor is believed to be lively since a minimum of April 2024.
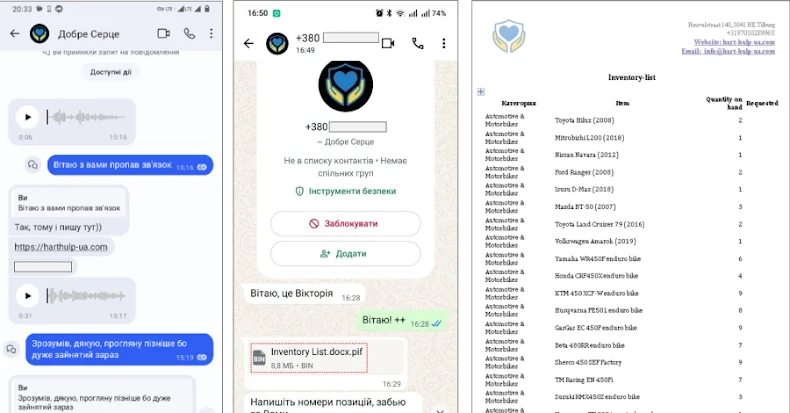
Assault chains distributing the malware leverage instantaneous messaging Sign and WhatsApp as vectors, with the risk actors masquerading as charity organizations to persuade targets into clicking on a seemingly-harmless hyperlink (“harthulp-ua[.]com” or “solidarity-help[.]org”) impersonating the inspiration and obtain a password-protected archive.
The archives comprise an executable created with PyInstaller that finally led to the deployment of PLUGGYAPE. CERT-UA mentioned successive iterations of the backdoor have added obfuscation and anti-analysis checks to stop the artifacts from being executed in a digital surroundings.
Written in Python, PLUGGYAPE establishes communication with a distant server over WebSocket or Message Queuing Telemetry Transport (MQTT), permitting the operators to execute arbitrary code on compromised hosts. Help for communication utilizing the MQTT protocol was added in December 2025.
As well as, the command-and-control (C2) addresses are retrieved from exterior paste companies equivalent to rentry[.]co and pastebin[.]com, the place they’re saved in base64-encoded type, versus immediately hard-coding the area within the malware itself. This offers attackers the power to keep up operational safety and resilience, permitting them to replace the C2 servers in real-time in eventualities the place the unique infrastructure is detected and brought down.
“Preliminary interplay with the goal of a cyber assault is more and more carried out utilizing authentic accounts and cellphone numbers of Ukrainian cellular operators, with using the Ukrainian language, audio and video communication, and the attacker could show detailed and related information in regards to the particular person, group, and its operations,” CERT-UA mentioned.
“Broadly used messengers out there on cellular gadgets and private computer systems are de facto changing into the most typical channel for delivering software program instruments for cyber threats.”
In current months, the cybersecurity company has additionally revealed {that a} risk cluster tracked as UAC-0239 despatched phishing emails from UKR[.]web and Gmail addresses containing hyperlinks to a VHD file (or immediately as an attachment) that paves the best way for a Go-based stealer named FILEMESS that collects recordsdata matching sure extensions and exfiltrates them to Telegram.
Additionally dropped is an open-source C2 framework known as OrcaC2 that allows system manipulation, file switch, keylogging, and distant command execution. The exercise is alleged to have focused Ukrainian protection forces and native governments.
Instructional establishments and state authorities in Ukraine have additionally been on the receiving finish of one other spear-phishing marketing campaign orchestrated by UAC-0241 that leverages ZIP archives containing a Home windows shortcut (LNK) file, opening which triggers the execution of an HTML Software (HTA) utilizing “mshta.exe.”
The HTA payload, in flip, launches JavaScript designed to obtain and execute a PowerShell script, which then delivers an open-source instrument known as LaZagne to recuperate saved passwords and a Go backdoor codenamed GAMYBEAR that may obtain and execute incoming instructions from a server and transmit the outcomes again in Base64-encoded type over HTTP.