Two critical vulnerabilities identified in Progress ShareFile pose significant threats to on-premises server security, allowing attackers to potentially gain control without authentication. These flaws specifically affect customer-managed ShareFile Storage Zones Controller version 5.x deployments.
Critical Vulnerabilities Identified
The vulnerabilities, tracked as CVE-2026-2699 and CVE-2026-2701, have been classified as critical with CVSS scores of 9.8 and 9.1, respectively. Progress advises customers to upgrade to version 5.12.4 or transition to any 6.x release to mitigate these risks.
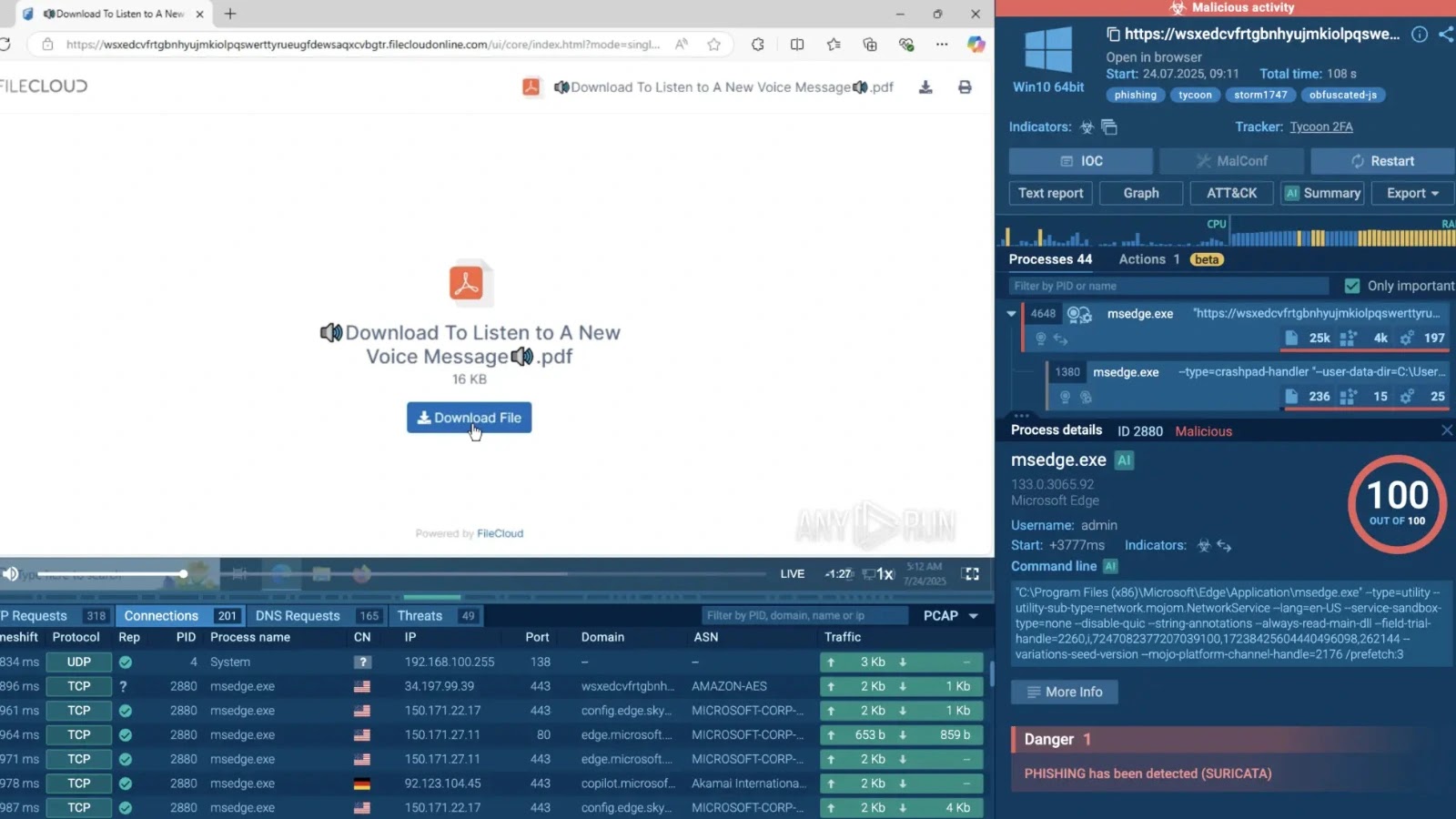
These security issues include an authentication bypass that makes restricted configuration pages accessible and a remote code execution flaw that can be exploited through malicious file uploads.
Implications for Enterprise Security
The ShareFile Storage Zones Controller, a crucial component for organizations managing data with cloud-based interfaces, is particularly vulnerable. This setup is popular among enterprises with compliance and security mandates, with approximately 30,000 instances reportedly exposed on the internet.
Such exposure makes these servers appealing targets for ransomware groups and other cybercriminals. The authentication bypass issue arises from an Execution After Redirect condition, where application logic continues after a redirect, potentially exposing admin functionalities to unauthorized users.
Urgent Mitigation and Response
Upon obtaining unauthorized access, attackers could alter critical settings, such as storage paths and passphrase configurations. Moreover, the second vulnerability enables malicious archives to be uploaded and extracted into server-controlled, web-accessible paths, facilitating remote code execution.
While Progress has not received reports of exploitation to date, the severity of these issues prompted urgent fixes released on April 2, 2026. These vulnerabilities were disclosed privately in February, with fixes implemented by March 10.
Organizations using affected versions should prioritize identifying exposed systems, applying patches promptly, and scrutinizing for unusual configuration changes or unexpected files.
Stay informed on cybersecurity developments by following us on Google News, LinkedIn, and X. Contact us to share your cybersecurity stories.