The Russian cyber espionage group known as APT28, also referred to as Forest Blizzard and Pawn Storm, has launched a sophisticated spear-phishing operation targeting Ukraine and its NATO allies. This campaign marks the deployment of a newly discovered malware suite named PRISMEX, aiming to infiltrate various sectors by exploiting recent vulnerabilities.
Advanced Techniques and Vulnerability Exploitation
PRISMEX employs advanced methods including steganography, Component Object Model (COM) hijacking, and misuse of legitimate cloud services to maintain command-and-control. According to Trend Micro researchers Feike Hacquebord and Hiroyuki Kakara, the campaign has been active since at least September 2025. Key sectors in Ukraine such as central executive bodies, defense, and emergency services, along with transportation and logistics partners in neighboring countries, are among those targeted.
APT28’s strategy involves rapidly exploiting newly disclosed security flaws, notably CVE-2026-21509 and CVE-2026-21513. Infrastructure for these attacks was established on January 12, 2026, preceding the public disclosure of one of the vulnerabilities. This indicates a preemptive approach to vulnerability exploitation.
Insight into APT28’s Zero-Day Exploitation
The use of zero-day vulnerabilities, specifically CVE-2026-21513, was highlighted when Akamai reported on a Microsoft Shortcut (LNK) exploit linked to APT28. This exploit was uploaded to VirusTotal on January 30, 2026, before Microsoft released a patch on February 10, 2026. Such actions suggest that APT28 had prior knowledge of these vulnerabilities, allowing them to craft a sophisticated two-stage attack chain.
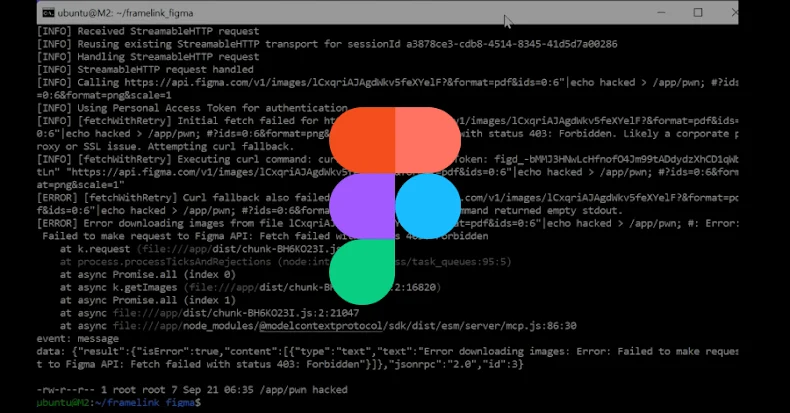
The attack sequence involves the initial exploitation of CVE-2026-21509 to deliver a malicious LNK file, which then triggers CVE-2026-21513 to circumvent security features. This results in the deployment of malware like MiniDoor and the PRISMEX suite, which utilizes steganography to hide its payloads within image files.
Components of the PRISMEX Malware Suite
The PRISMEX suite comprises several components, including PrismexSheet, PrismexDrop, PrismexLoader, and PrismexStager. Each plays a role in establishing persistence, executing payloads, and maintaining stealth. PrismexSheet exploits Excel files to conceal payloads, while PrismexLoader uses a unique algorithm to extract further payloads from images. PrismexStager, linked to the COVENANT framework, utilizes cloud storage for command-and-control operations.
Previous analysis by Zscaler ThreatLabz under the name Operation Neusploit has documented some aspects of this campaign. APT28’s use of the COVENANT framework was first reported by the Computer Emergency Response Team of Ukraine (CERT-UA) in mid-2025, indicating the ongoing development and deployment of advanced cyber tools.
Implications and Strategic Shifts
This operation underscores APT28’s aggressive tactics and strategic targeting of supply chains and operational capabilities in Ukraine and NATO. The focus on disrupting infrastructure supporting Ukraine suggests potential for more destructive cyber activities in the future. Trend Micro’s analysis highlights the danger posed by APT28 as they continue to evolve their methods and objectives.