Cybersecurity experts have identified a new iteration of the Chaos malware, which now targets improperly configured cloud environments. This development represents a significant expansion of the botnet’s typical attack range, which previously focused on routers and edge devices.
Targeting Misconfigured Cloud Deployments
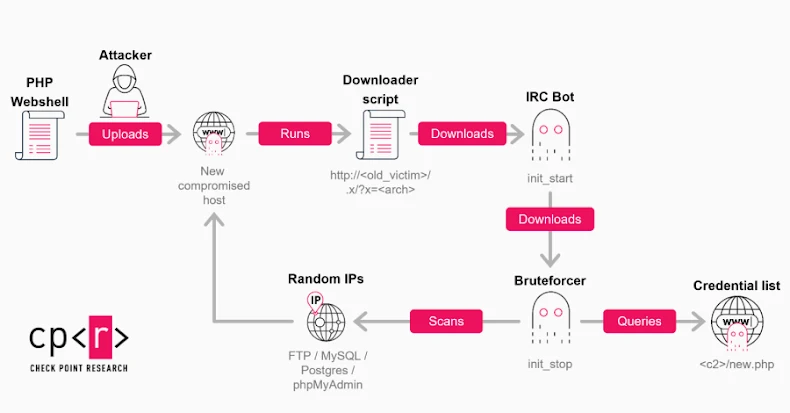
Chaos, initially documented by Lumen Black Lotus Labs in September 2022, is a versatile malware capable of operating on both Windows and Linux platforms. Its functionalities include executing remote shell commands, deploying additional modules, brute-forcing SSH keys, mining cryptocurrency, and launching DDoS attacks across various protocols such as HTTP, TLS, TCP, UDP, and WebSocket.
The malware is considered an evolution of the Kaiji DDoS malware, previously known for exploiting vulnerable Docker instances. Although the identities of the operators remain unknown, the presence of Chinese language elements and infrastructure suggests a possible Chinese origin.
New Variant and Its Methodology
Darktrace recently identified this new variant within its honeypot network through a misconfigured Hadoop instance that facilitates remote code execution. The attack began with an HTTP request aimed at the Hadoop deployment, which initiated the creation of a new application.
This application executed a series of shell commands to download a Chaos agent binary from a server controlled by the attackers, modify permissions to allow execution, and then remove the binary to reduce forensic evidence. The domain linked to this activity was previously involved in phishing campaigns orchestrated by the Chinese group Silver Fox, known as Operation Silk Lure.
Functional Changes and Implications
The 64-bit ELF binary of the Chaos variant has undergone restructuring and updates, while retaining most of its core features. Notably, it has removed functions for spreading via SSH and exploiting router vulnerabilities, replacing them with a new SOCKS proxy feature. This addition allows the compromised system to relay traffic, obscuring the origins of malicious activities and complicating detection efforts.
Darktrace also noted alterations in functions previously associated with Kaiji, indicating extensive refactoring or rewriting by the threat actors. The integration of the proxy feature suggests an intention to monetize the botnet further by offering diverse illicit services, beyond just cryptocurrency mining and DDoS attacks.
The continuous development of Chaos underscores the commitment of cybercriminals to enhance their tools and expand their botnets. The incorporation of proxy services in botnets like AISURU and Chaos signifies a shift in tactics, where denial-of-service attacks are just one of several threats posed to organizations and their security teams.