Austin, Texas – A groundbreaking AI-native threat intelligence platform has been launched by Mallory, aiming to transform enterprise security practices. Spearheaded by a team of seasoned security experts, including a former Google and Mandiant executive, the platform is set to address pressing questions posed by Chief Information Security Officers (CISOs) and their teams.
Revolutionizing Threat Intelligence
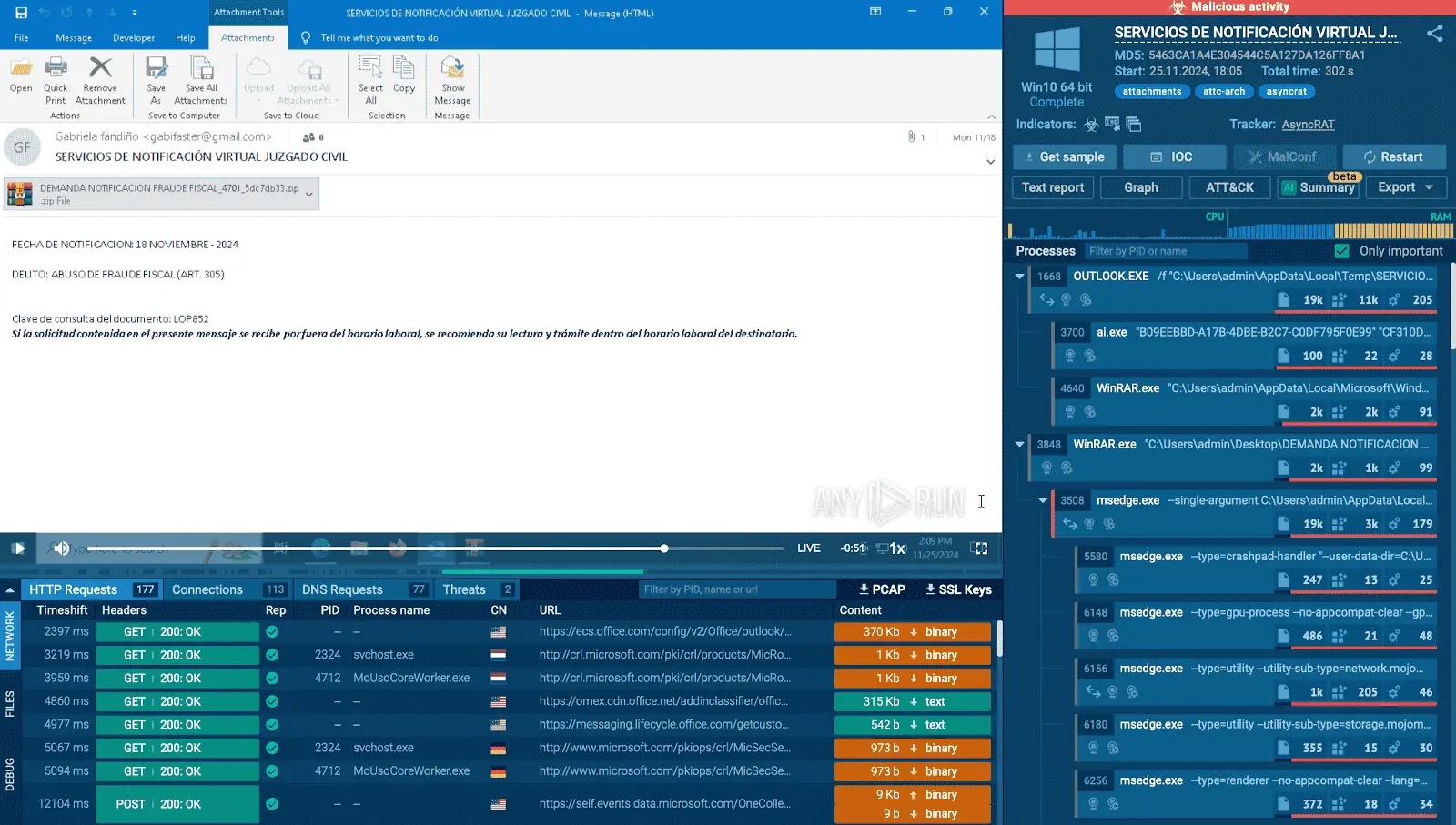
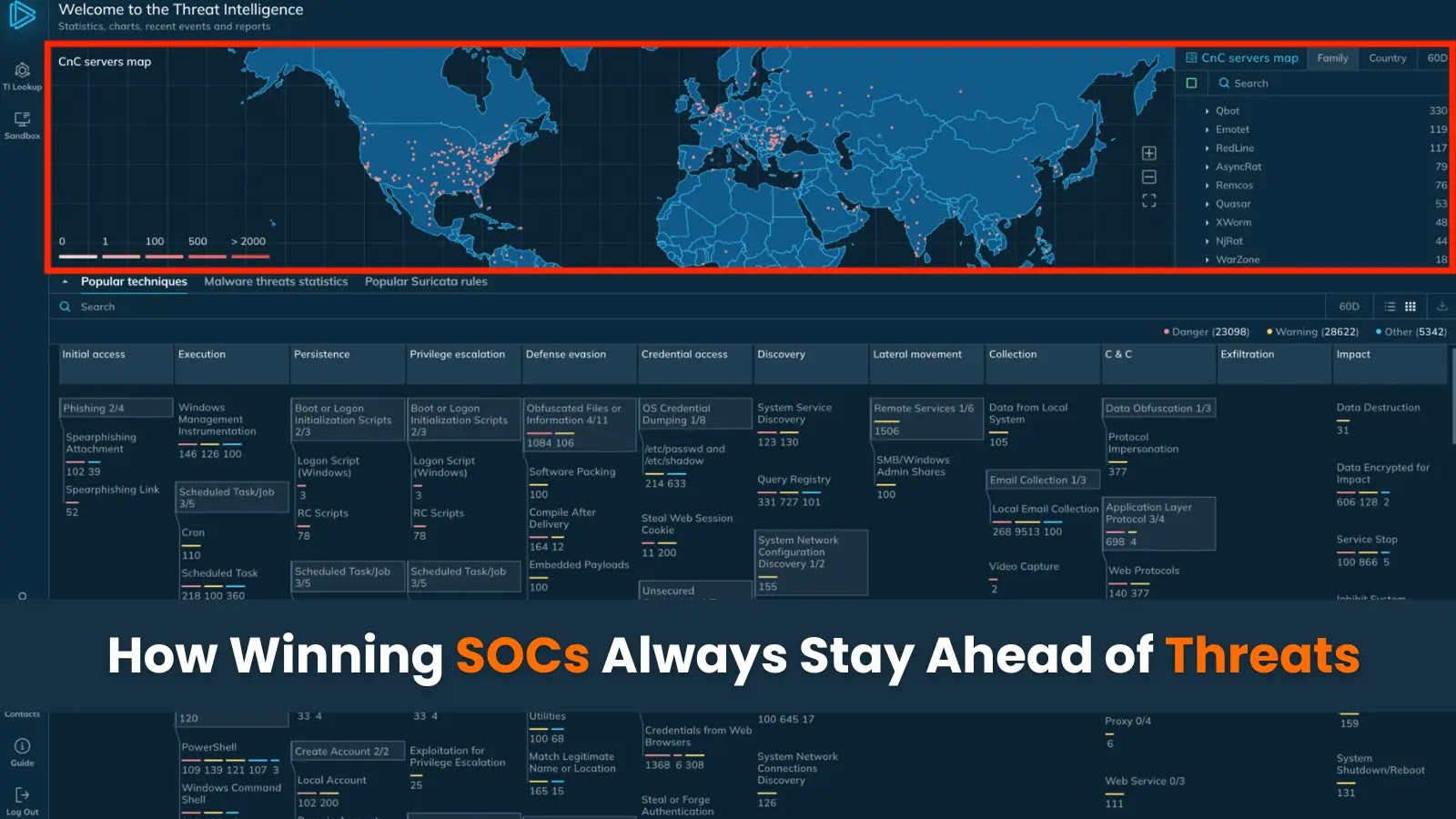
Mallory’s innovative platform is designed to deliver actionable intelligence, answering critical questions such as identifying genuine threat vectors, assessing exploitable vulnerabilities, and determining proactive mitigation strategies. By monitoring thousands of threat sources and contextualizing data against the user’s attack surface, Mallory provides comprehensive intelligence solutions for hunting, detection, and exposure management.
Security teams are often overwhelmed with signals and alerts, struggling to transition from reactive to proactive defenses. Mallory integrates seamlessly with existing security tools, offering not just alerts but actionable insights on new vulnerabilities. The platform tracks exploitation activity, evaluates organizational risk, and suggests remediation steps.
Meeting Modern Security Demands
According to Jonathan Cran, Mallory’s founder and CEO, the speed and capability of AI-enabled attackers necessitate equally advanced defensive measures. The platform focuses on providing answers rather than generating more alerts, helping security teams understand attacker capabilities, evaluate control effectiveness, and identify immediate threats.
Mallory’s approach results in a prioritized set of evidence-based cases, mapped directly to the user’s environment. This enables swift action and informed decision-making, as highlighted by John Sapp, CISO of Texas Mutual Insurance, who values the platform’s ability to deliver rapid context for emerging threats.
Investment and Market Entry
Mallory’s launch is bolstered by a seed investment from Decibel Partners, with contributions from Live Oak Venture Partners and industry leaders from companies like Google and Cisco. Dan Nguyen-Huu, a partner at Decibel, emphasizes the platform’s potential to address the context and reasoning challenges in cybersecurity by connecting real-time threat activity to organizational environments.
Available immediately as a SaaS platform, Mallory supports integrations with existing security infrastructure, allowing teams to customize and extend its functionalities. Interested users can explore the platform with a 30-day free trial.
About Mallory
Mallory stands as a leader in AI-native threat intelligence, offering cyber defenders a means to monitor global adversary activities and prioritize threats effectively. For more information, visit mallory.ai.
Contact
Marketing
Chris Tilton
Mallory
[email protected]