A new variant of the PlugX worm is spreading stealthily across continents by embedding itself in USB drives, reaching regions spanning nearly ten time zones. Initially identified in Papua New Guinea in August 2022, it reemerged in January 2023 in both Papua New Guinea and Ghana, which are separated by approximately 10,000 miles. Subsequent infections were reported in Mongolia, Zimbabwe, and Nigeria, marking a significant geographical spread.
Global Spread of PlugX Worm
The PlugX malware is not a new threat; it is a remote access Trojan (RAT) originating from China that has been utilized by cybercriminals for years. This new variant is distinguished by a novel payload and its connection to a command-and-control (C2) server previously not closely associated with this malware family. The worm employs DLL sideloading, a method that coerces a legitimate application into loading a malicious library, allowing the malware to execute its code without immediate detection.
Technical Analysis and Infection Mechanism
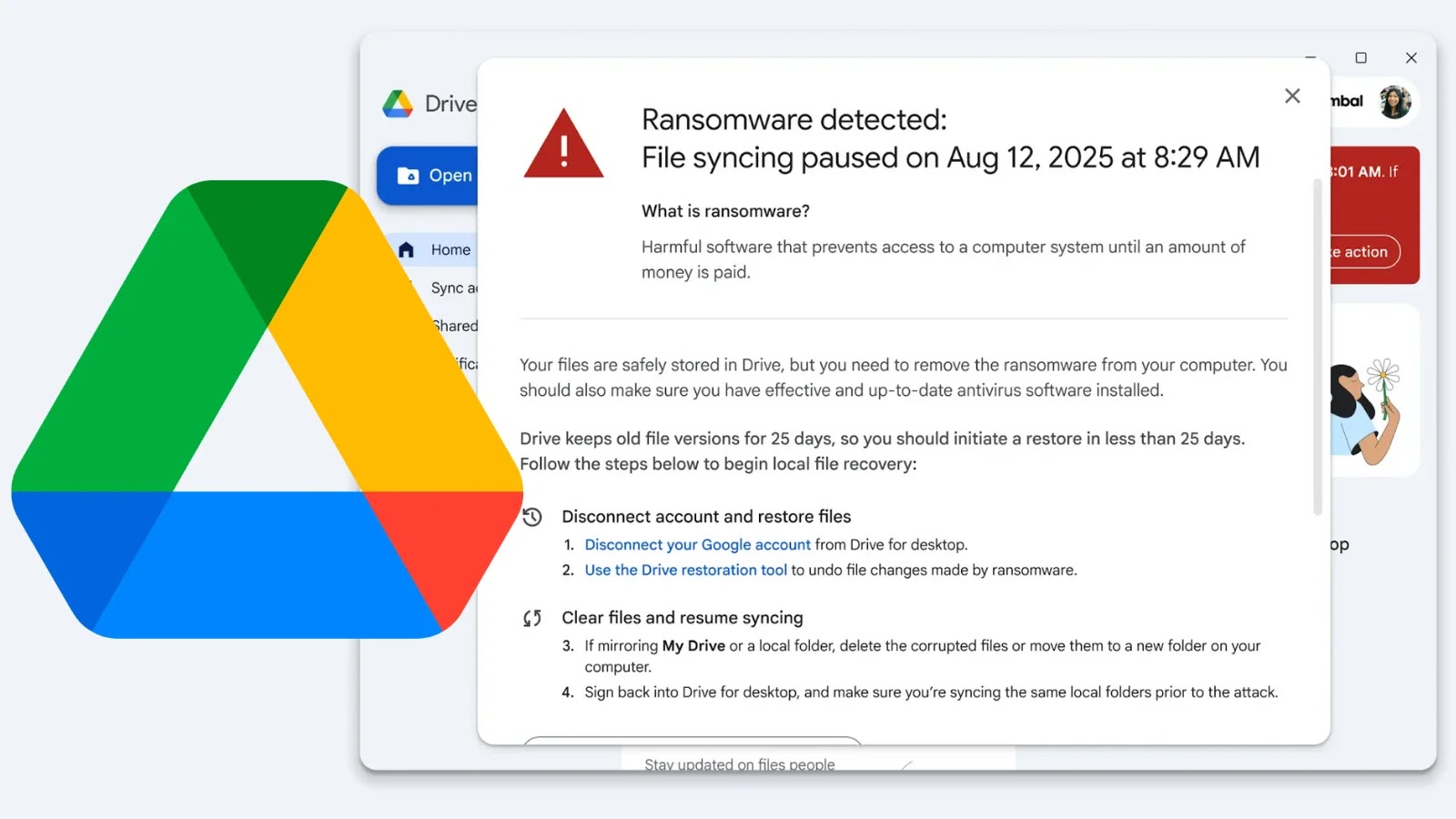
Researchers from Sophos X-Ops, led by analyst Gabor Szappanos, uncovered this variant following a CryptoGuard alert, likely triggered by a data theft attempt. The infection package comprises a legitimate AvastSvc.exe executable, vulnerable to DLL sideloading, a malicious DLL called wsc.dll, and an encrypted payload file. These components collaborate to discreetly operate the PlugX backdoor on compromised systems.
The C2 activity was traced to IP address 45.142.166[.]112, previously mentioned in a 2019 report by Unit 42 as loosely connected to PlugX but not directly linked to any known threat actor. Sophos researchers now assert that the tactics used are consistent with those of PKPLUG, also known as Mustang Panda, a China-linked advanced persistent threat (APT) group.
Preventive Measures Against USB-Based Malware
The PlugX variant uses deception as its core infection strategy. When the worm copies itself onto a USB drive, it utilizes specific mutex strings, USB_NOTIFY_COP and USB_NOTIFY_INF, to manage the operation. Once transferred, the USB drive appears empty in a standard Windows Explorer view, masking the presence of a shortcut file designed to resemble another removable disk.
Clicking the shortcut silently executes the CEFHelper executable, a renamed AvastSvc.exe file, disguised to resemble a legitimate Adobe process. Other malicious files and directories are hidden by default in file listings. The worm stores its components within a directory named RECYCLER.BIN, using a desktop.ini file to mimic a genuine Recycle Bin, further concealing its activities.
Organizations should view USB connections as potential security threats, especially in environments handling sensitive information. Disabling AutoRun and AutoPlay for all removable media is a straightforward yet effective preventive measure. IT departments should also configure systems to display hidden and system files by default, which can help detect suspicious directories like RECYCLER.BIN. Regularly monitoring outbound C2 traffic and using endpoint protection that detects DLL sideloading activities are crucial steps for any organization confronting this targeted threat.
For more updates, follow us on Google News, LinkedIn, and X. Set CSN as a preferred source on Google.