Cybercriminals have discovered a method to bypass conventional security measures by exploiting the AI workflow automation tool known as n8n. This strategy involves repurposing a legitimate productivity platform to distribute phishing emails and harmful software directly to target devices.
Exploitation of n8n Platform
The misuse of the n8n platform was initially detected in October 2025, continuing through to March 2026. During this timeframe, attackers registered free developer accounts on n8n, which automatically generated subdomains under the *.app.n8n[.]cloud namespace. These subdomains, associated with a well-known service, allowed emails and web requests to be perceived as credible by many corporate security systems.
This tactic enabled malicious content to be transmitted via a channel that would not typically trigger alarms in most email security frameworks. Researchers from Cisco Talos, Sean Gallagher and Omid Mirzaei, uncovered this exploitation and released an in-depth analysis of these cyber campaigns.
Malware Delivery and Device Fingerprinting
The investigation by Cisco Talos revealed that the primary vulnerability lay in n8n’s URL-exposed webhooks, a standard feature that facilitates real-time data exchange between applications. The researchers noticed a significant uptick in emails containing n8n webhook URLs, with a 68% increase in March 2026 compared to January 2025, indicating a deliberate escalation in platform misuse.
Two primary attack vectors were identified: malware deployment and device fingerprinting. Attackers embedded invisible tracking pixels in HTML emails using n8n webhook URLs to gather device information from recipients who opened the email. Concurrently, phishing campaigns distributed active malware payloads via the same webhook delivery system.
In-Depth Look at the Attack Chain
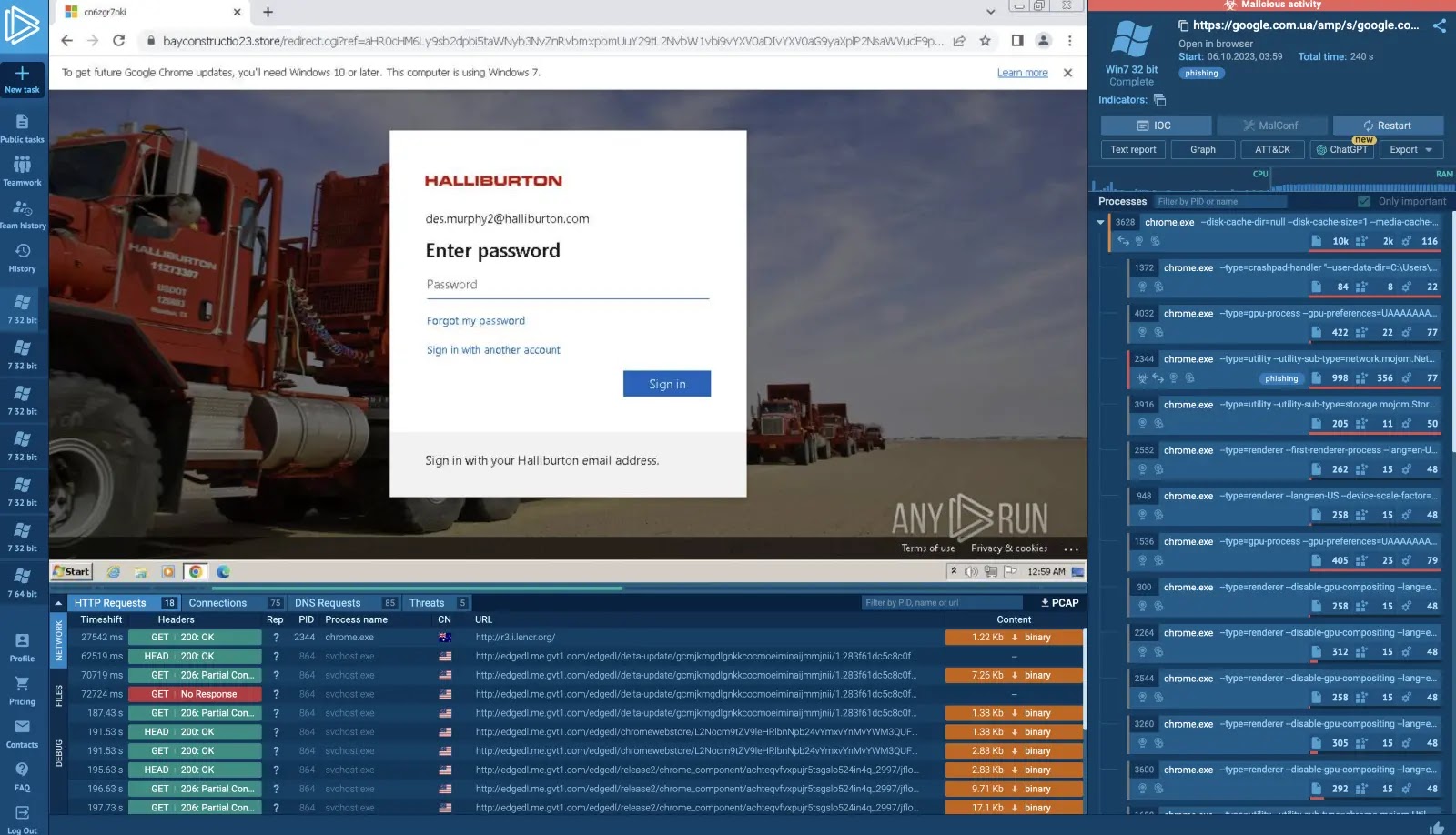
One notable campaign involved phishing emails masquerading as Microsoft OneDrive notifications. Clicking the embedded n8n webhook link led recipients to an HTML page with a CAPTCHA challenge. This step filtered out automated scanners, ensuring only human users proceeded.
Upon solving the CAPTCHA, users were prompted to download a file named DownloadedOneDriveDocument.exe, which was fetched from an external source but appeared to originate from n8n’s trusted infrastructure. This executable installed a modified version of the Datto Remote Monitoring and Management tool, which then used PowerShell commands to establish a persistent connection to a malicious domain before erasing traces of its presence.
Another campaign utilized a similar approach to distribute a corrupted Microsoft Windows Installer file that installed the ITarian Endpoint Management tool, serving as a backdoor for data exfiltration.
Recommendations for Security Teams
Cisco Talos advises security teams to move beyond static domain blocking, as blocking n8n[.]cloud entirely could disrupt legitimate operations. Instead, they suggest implementing behavioral detection systems to flag unusual traffic toward automation platform domains.
Organizations should also monitor endpoints communicating with AI automation domains not included in their approved workflow inventory, as this may indicate a compromise. Sharing indicators of compromise, such as specific webhook URL structures and malicious file hashes, through intelligence platforms like Cisco Talos Intelligence is also recommended. Deploying AI-driven email security solutions that assess behavioral signals can further bolster defenses against threats leveraging trusted infrastructures.
Stay updated by following us on Google News, LinkedIn, and X, and consider setting CSN as a preferred source on Google for more instant updates.