The Cybersecurity and Infrastructure Security Agency (CISA) has raised alarms over a significant vulnerability in Apache ActiveMQ, urging prompt action from federal and private sectors.
On April 16, 2026, this vulnerability, identified as CVE-2026-34197, was officially placed into CISA’s Known Exploited Vulnerabilities (KEV) catalog. This move mandates immediate attention from federal agencies and private security teams to secure their systems against potential breaches.
Apache ActiveMQ is a crucial open-source tool facilitating communication between complex enterprise applications. Its widespread use underscores the importance of addressing any security weaknesses promptly.
Exploitation Risks and Vulnerability Details
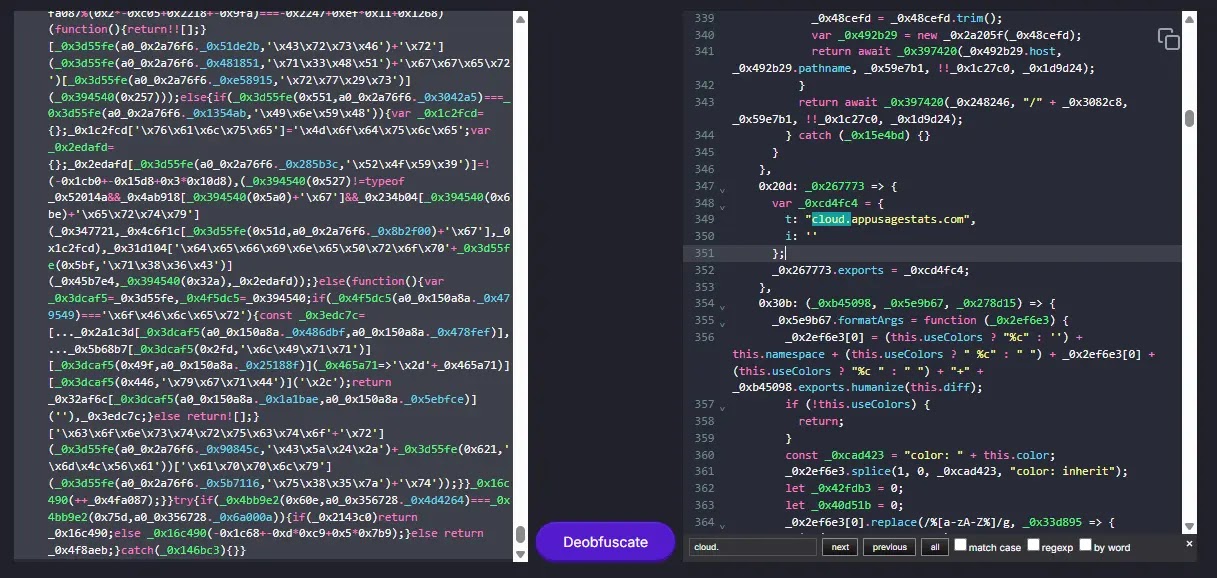
This particular flaw stems from inadequate input validation within the Apache ActiveMQ framework, allowing for severe code injection attacks. Such vulnerabilities offer attackers a strategic advantage, given ActiveMQ’s role in internal data management.
Classified under CWE-20 for improper input validation and CWE-94 for improper control of code generation, the flaw enables malicious command execution. Attackers can exploit unsanitized user input to inject harmful payloads, leading to unauthorized code execution on the server.
With confirmed reports of active exploitation, cybercriminals are increasingly targeting exposed ActiveMQ instances to gain initial access to networks. This vulnerability poses a critical threat, with potential for lateral movement and privilege escalation within compromised systems.
Current Threat Landscape
While there is no concrete evidence of ransomware groups leveraging CVE-2026-34197, the threat remains high. The flaw’s capacity for remote code execution makes it attractive to both initial access brokers and advanced persistent threat (APT) groups.
Organizations with unpatched ActiveMQ systems face significant risks, including data theft and full system takeover. The urgency of addressing this vulnerability cannot be overstated, given its potential for widespread impact.
Protective Measures and Compliance
In response to the escalating threat, CISA has enforced strict timelines through Binding Operational Directive (BOD) 22-01. Federal agencies are required to secure their systems by April 30, 2026, with a strong recommendation for private entities to follow suit.
Immediate actions for organizations include applying the latest security updates as per Apache’s official guidance, adhering to BOD 22-01 for cloud services, and potentially discontinuing ActiveMQ use if updates are unavailable.
Monitoring network traffic and server logs for unusual activity is crucial for detecting and preventing code injection attempts. Organizations are encouraged to remain vigilant and proactive in safeguarding their infrastructure.
For ongoing cybersecurity updates, follow us on Google News, LinkedIn, and X. Contact us for potential feature stories.