An advanced persistent threat group has devised a method to conceal malicious activities within Microsoft Outlook, complicating detection by standard security systems.
Innovative Espionage Tactics
The hacking collective, Harvester APT, believed to be state-sponsored and active since 2021, has launched a Linux version of its GoGra backdoor. This malware uses Microsoft Graph API and Outlook mailboxes as a hidden command-and-control channel, enabling it to evade traditional network defenses.
Focusing on espionage, this campaign primarily targets South Asia, with initial malware submissions from India and Afghanistan suggesting localized targeting. The use of culturally relevant decoy documents further indicates a strategic approach to espionage.
Cross-Platform Expansion
Security researchers from Symantec and Carbon Black identified this Linux variant as an evolution of Harvester’s previous Windows-focused operations. They noted significant code similarities, indicating that Harvester is expanding its capabilities across different platforms.
The group’s initial access method involved social engineering, using decoy documents that appeared legitimate but harbored malicious Linux ELF binaries. Once executed, these files initiated a stealth infection process, embedding persistence mechanisms to withstand reboots.
Leveraging Microsoft Infrastructure
Technically, the most notable feature of the backdoor is its use of legitimate Microsoft cloud services for covert communication. After infecting a system, a Go dropper delivers an executable payload to initiate and maintain the backdoor’s operations.
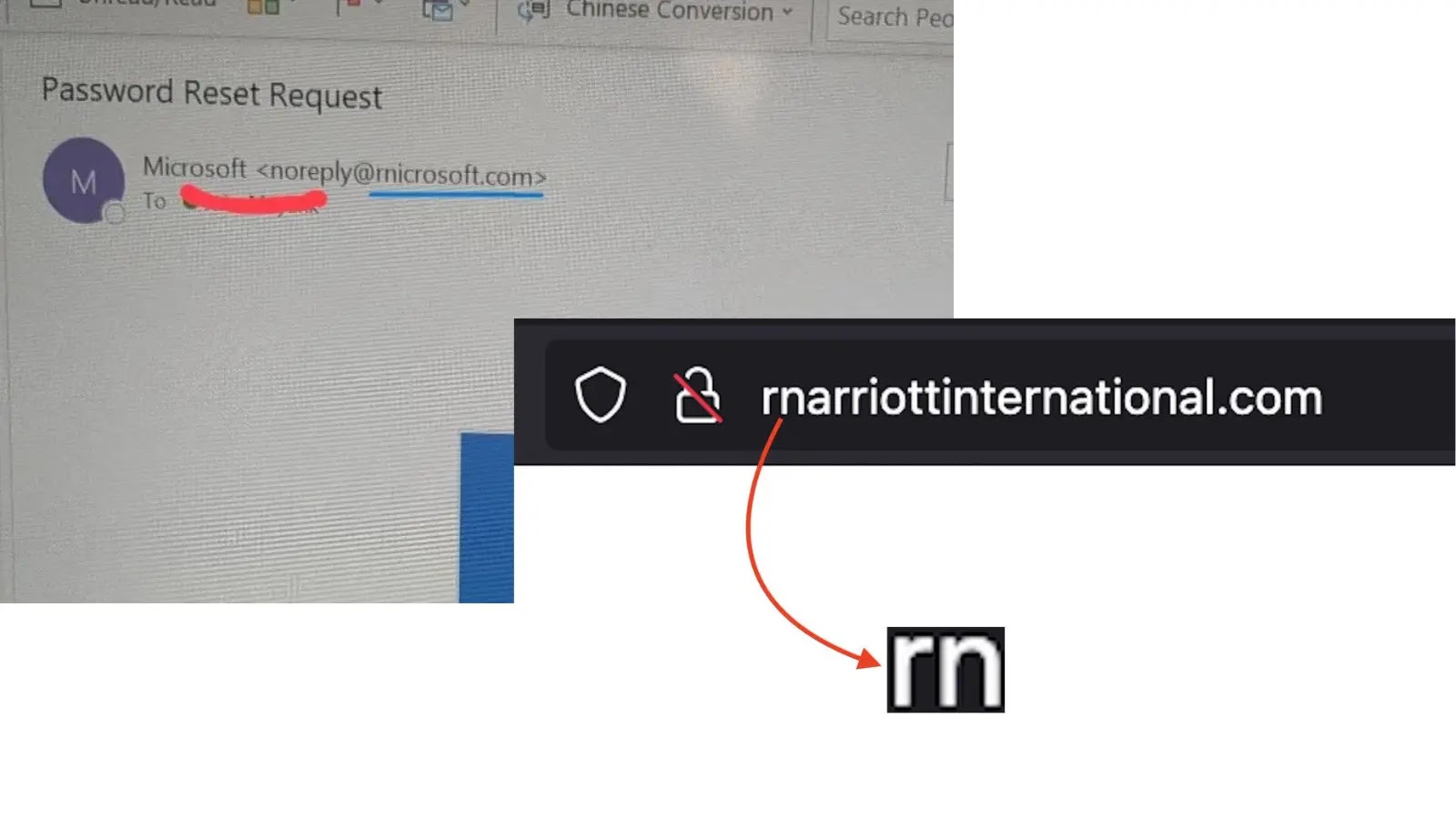
The malware uses hardcoded Azure AD credentials to obtain OAuth2 tokens, enabling it to communicate through a designated Outlook mailbox. Commands are sent via emails, decrypted, executed, and the results are securely returned, erasing traces of the interaction.
Security teams are advised to scrutinize unexpected autostart entries and systemd services, particularly those mimicking legitimate software. Organizations should monitor OAuth2 token requests and Microsoft Graph API activity for irregularities. Blocking unknown Azure AD credentials can mitigate such threats.
For further insights and updates, follow our channels on Google News, LinkedIn, and X.