Bitwarden CLI Breach Unveiled
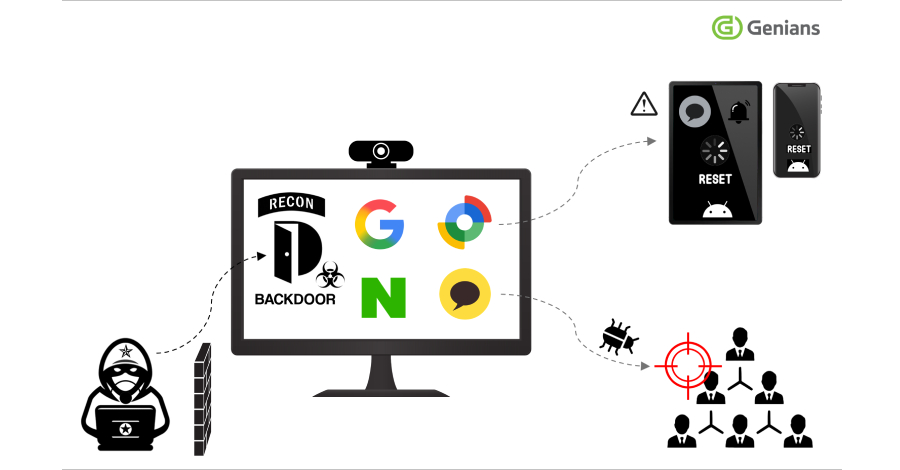
In a significant security incident, the Bitwarden CLI has been compromised as part of the Checkmarx supply chain campaign, according to recent analyses by JFrog and Socket. The package affected is identified as @bitwarden/[email protected], with malicious code embedded in the ‘bw1.js’ file. This breach follows a pattern wherein a compromised GitHub Action in Bitwarden’s CI/CD pipeline was exploited, mirroring other incidents within the campaign.
Details of the Compromise
JFrog reported that the compromised package was designed to extract GitHub/npm tokens, .ssh keys, environment variables, shell histories, and cloud secrets, transmitting this data to private domains and through GitHub commits. Although this rogue version is no longer available on npm, the attack vector aligns with previously identified methods in the Checkmarx campaign.
Security researcher Adnan Khan noted the attackers used stolen GitHub tokens to inject a malicious workflow into the GitHub Actions pipeline. This workflow was then used to publish the compromised Bitwarden CLI, marking a significant breach in npm’s trusted publishing model.
The Threat Actor and Attack Analysis
TeamPCP is suspected to be behind this latest attack aimed at Checkmarx. Their social media presence has been curtailed, as their account on the platform X was suspended. OX Security’s investigation highlighted a string within the package, “Shai-Hulud: The Third Coming,” suggesting a continuation of the supply chain attack campaign that emerged last year.
Moshe Siman Tov Bustan from OX Security emphasized the gravity of the incident, noting that data exfiltrated to GitHub is often overlooked by security tools, thus increasing the risk of exposure as it can be accessed by anyone searching the platform.
Response and Mitigation Efforts
Bitwarden confirmed the breach but assured that no user data was accessed. The security team quickly contained the threat, revoking unauthorized access, deprecating the malicious npm release, and implementing corrective measures. The affected package was available only briefly on April 22, 2026, and no legitimate Bitwarden CLI codebase or stored vault data was compromised.
Bitwarden has completed a thorough review of its systems, confirming no further impact on other products or environments. A CVE for the Bitwarden CLI version 2026.4.0 is being issued. This incident underscores the need for heightened vigilance in monitoring supply chain security.
This story is ongoing, and updates will follow as more details emerge.