A newly emerged ransomware group, Vect 2.0, is making waves in the cyber threat arena with its sophisticated Ransomware-as-a-Service (RaaS) model. This operation is targeting systems running on Windows, Linux, and VMware ESXi, posing a significant risk to multiple sectors worldwide.
Introduction of Vect 2.0
First identified in December 2025, Vect 2.0 quickly expanded its operations by February 2026, affecting at least 20 victims from various countries and key industry sectors. This development marks the evolution of the previous ‘Vect’ operation, now enhanced by a custom C++ codebase that enables cross-platform attacks.
Triple-Threat Attack Model
The Vect 2.0 group employs a three-pronged attack strategy they describe as ‘Exfiltration / Encryption / Extortion.’ Initially, they extract sensitive data, then encrypt it to lock out the affected organizations, and finally, they threaten to release the data unless a ransom is paid. This approach severely disrupts operations and poses the threat of public data release.
The Data Security Council of India (DSCI) has been actively monitoring Vect 2.0 through dark web analysis and threat intelligence. As of February 28, 2026, their findings show 20 active cases listed on the group’s Data Leak Site (DLS), with data from six victims already leaked.
Global Impact and Defensive Strategies
Countries such as Brazil, the United States, and India are prominently targeted, with several other nations also affected. The most impacted sectors include manufacturing, education, healthcare, and technology, which are highly reliant on data availability.
Vect 2.0’s infrastructure is built on TOR hidden services and transactions are conducted in Monero, complicating financial tracking. Affiliates are required to pay an entry fee, except those from Commonwealth of Independent States (CIS), suggesting a possible origin in Russia or Belarus.
Strategically, organizations are advised to block known Vect 2.0 IP addresses and restrict TOR traffic. Monitoring for unusual Safe Mode reboots and enforcing multi-factor authentication on remote access services can mitigate risks. The 3-2-1 backup strategy and ongoing phishing awareness are critical for protection.
Infection Mechanisms and Evasion Techniques
Vect 2.0 utilizes distinct executables for different platforms, disguising the Windows payload as a legitimate system process, and deploying targeted binaries for Linux and VMware ESXi. The ransomware appends files with a ‘.vect’ extension and provides ransom instructions via TOR.
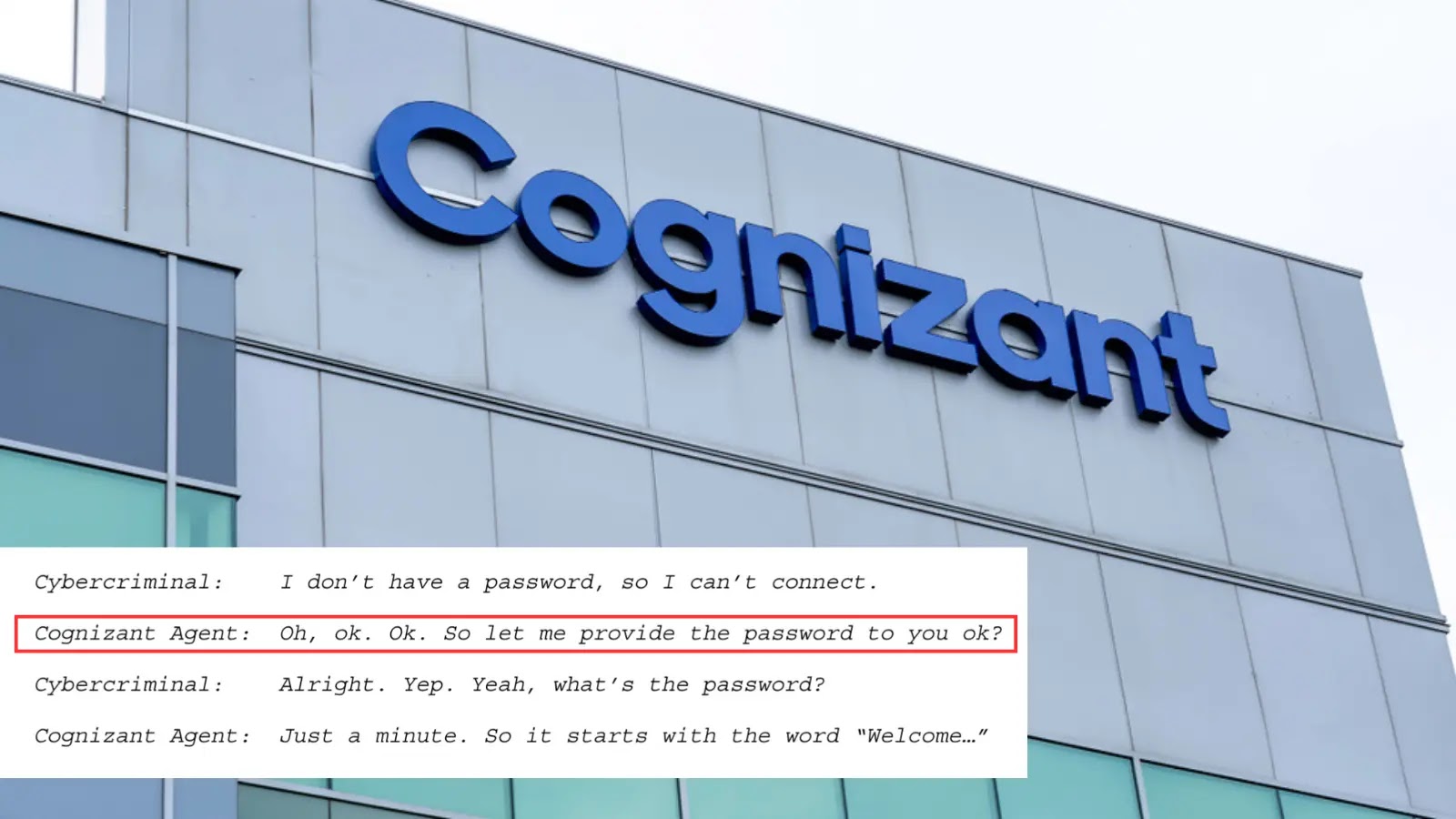
An evasion technique involves rebooting systems into Safe Mode, circumventing many security tools. Initial network access is often gained through compromised credentials, exposed RDP or VPN services, or phishing emails. The group then moves through the network, exfiltrating data before encryption.
As cyber threats evolve, staying informed and proactive in implementing security measures is crucial for safeguarding organizational data and operations.