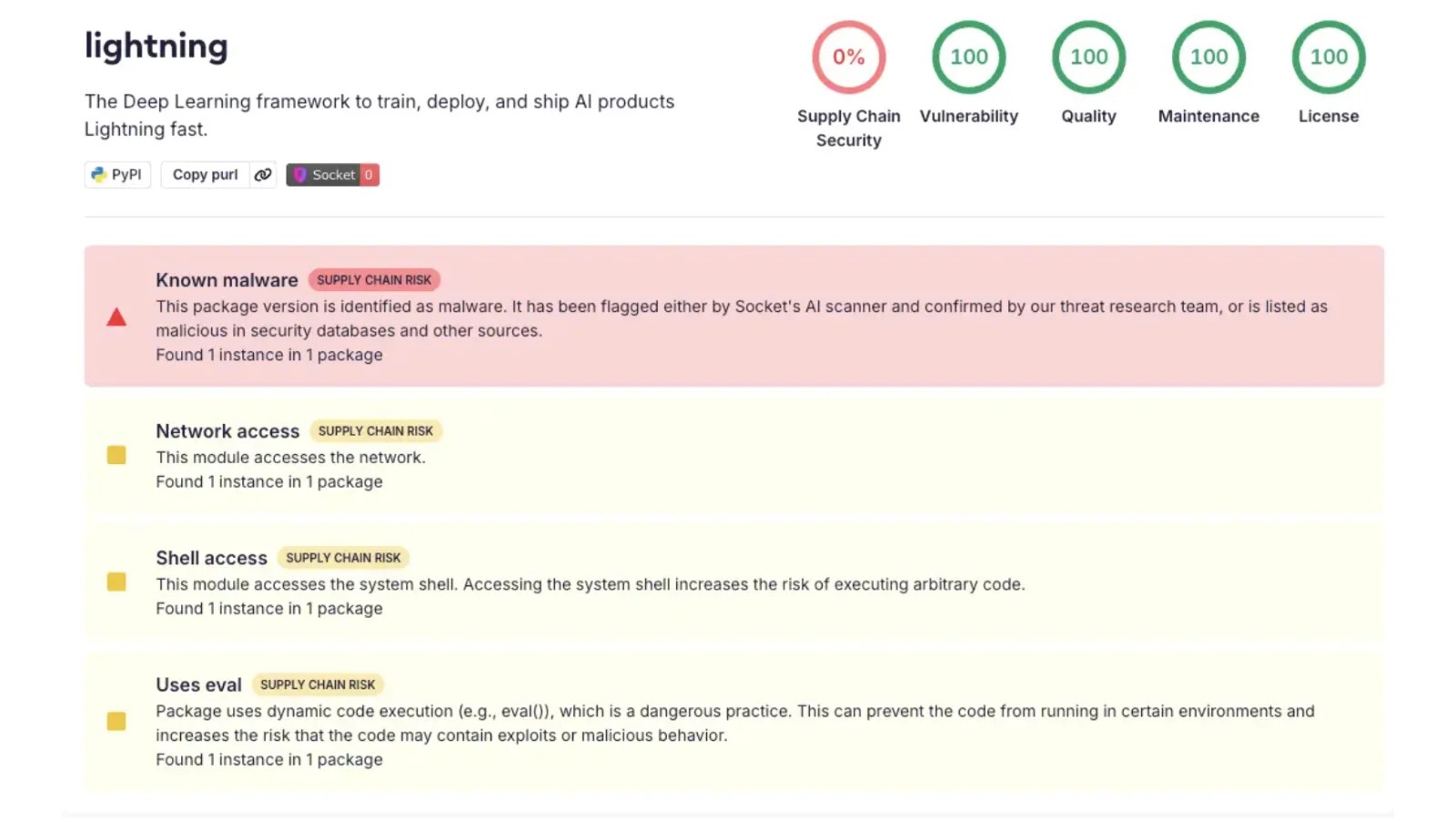
An alarming supply chain attack has targeted the widely-utilized Python package, lightning, a crucial tool in the realm of AI and machine learning development. The breach has not only executed credential-stealing malware but also compromised GitHub maintainer accounts, raising significant security concerns.
Identified by Socket’s Research Team, the malicious versions 2.6.2 and 2.6.3 of the lightning package were flagged a mere 18 minutes post-publication on April 30, 2026. In contrast, version 2.6.1, released earlier in January, remains unaffected and is deemed safe for use, serving as the last secure benchmark.
Implications of the Compromised Package
This breach targets developer workstations, continuous integration/continuous deployment (CI/CD) pipelines, and cloud build environments. Systems that have installed and imported the compromised package versions are vulnerable to the attack.
Socket’s research uncovered a covert _runtime directory within the compromised packages, housing a multi-stage execution chain that activates without user intervention upon module import. This includes components like start.py, which downloads and runs Bun, a JavaScript runtime, and router_runtime.js, a heavily obfuscated payload.
Technical Details of the Malware
The router_runtime.js payload, measuring 11 MB, is extensively obfuscated, with numerous references to system processes and authentication materials, making detection challenging. The malware silently exfiltrates credentials, targeting GitHub tokens, NPM tokens, and cloud account details.
Further analysis reveals parallels with the Shai-Hulud attack campaign, sharing similar credential targeting patterns and obfuscation techniques. This incident is part of an ongoing open-source supply chain campaign by Team PCP, which has previously compromised other platforms.
Response and Future Actions
Reports from the community and subsequent actions taken on GitHub indicate a possible compromise of the project’s GitHub account. Security teams are advised to treat environments using lightning versions 2.6.2 and 2.6.3 as compromised.
Immediate actions include removing the affected versions, reverting to version 2.6.1, and rotating all credentials. A thorough audit of GitHub repositories and system logs is also recommended to identify unauthorized activities. Socket continues to investigate and will provide further insights as the situation evolves.
Stay informed with the latest updates on this security breach by following us on Google News, LinkedIn, and X. For more insights, contact us with your cybersecurity stories.